The acronym RFID (Radio Frequency Identification) refers to a wireless technology that uses radio frequency waves to automatically, efficiently, and quickly identify all types of assets and entities (stationary or moving, slow or fast), people, animals, and objects (metallic or non-metallic, in both liquid and dry environments). It is presented as a successor to, and sometimes complementary to, barcode technology. It is widely used in Logistics and Supply Chain Management (LSCM), enabling efficient, real-time inventory traceability. RFID technology adds visibility as objects/entities flow through a supply chain from the manufacturer, shipping companies, distributors, and retail outlets. This added visibility allows for the identification of potential bottlenecks, as well as saving time and money. RFID is a rapidly evolving technology and a present and future alternative, far more advanced than traditional barcodes. However, some RFID manufacturers (such as Ferroxcube with its Ferroxtag family of tags) include a barcode on their RFID tags to allow users to benefit from the complementarity of RFID and barcode technologies. RFID applications are growing very rapidly across a highly diversified market where many new sectors can be identified, such as consumer goods, pharmaceuticals, postal packages, healthcare, e-government, e-administration, and more. Authoritative predictions indicate that China will need at least 4.5 billion RFID devices in 2008 and 5.5 billion in 2010. IDTechEX estimates that sales of RFID tags will increase from $2.77 billion to $27.88 billion between 2006 and 2017.
Origins of RFID Technology: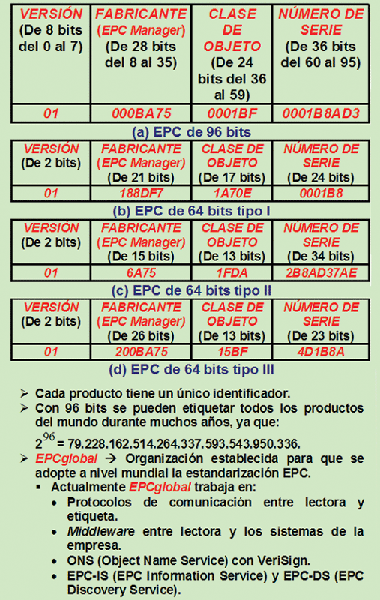 Modern automatic identification systems have a long technological history and diverse roots. The most widely recognized automatic identification system is the barcode system, developed in the early 1970s, but the technology most closely related to current RFID systems is even older. During World War II, Allied aircraft were equipped with friend-or-foe identification devices. A civilian variant known as EAS (Electronic Article Surveillance) allows for friend-or-foe discrimination within a store. Other systems of this type have also found their way into public life in the area of identifying the authorized owner to disable or activate vehicle immobilizers. In recent years, significant work has been done to bring all these root technologies together into a successor technology called RFID. Some technologies have renamed the term RFID, while others have reinvented it, as is the case with EPC (Electronic Product Code) tags, which replaced EAN (Electronic Article Number) barcodes. One of the main tasks in this sector has been reducing the cost of RFID tags. However, the possibility that the information they carry can be read wirelessly from a distance without the owner's knowledge has raised concerns about a potential loss of privacy and even security risks.
Modern automatic identification systems have a long technological history and diverse roots. The most widely recognized automatic identification system is the barcode system, developed in the early 1970s, but the technology most closely related to current RFID systems is even older. During World War II, Allied aircraft were equipped with friend-or-foe identification devices. A civilian variant known as EAS (Electronic Article Surveillance) allows for friend-or-foe discrimination within a store. Other systems of this type have also found their way into public life in the area of identifying the authorized owner to disable or activate vehicle immobilizers. In recent years, significant work has been done to bring all these root technologies together into a successor technology called RFID. Some technologies have renamed the term RFID, while others have reinvented it, as is the case with EPC (Electronic Product Code) tags, which replaced EAN (Electronic Article Number) barcodes. One of the main tasks in this sector has been reducing the cost of RFID tags. However, the possibility that the information they carry can be read wirelessly from a distance without the owner's knowledge has raised concerns about a potential loss of privacy and even security risks.
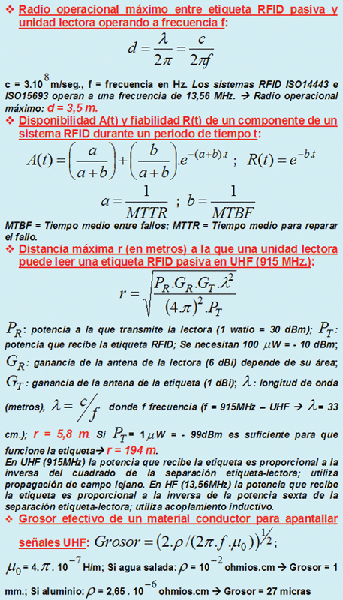
RFID System Component Architecture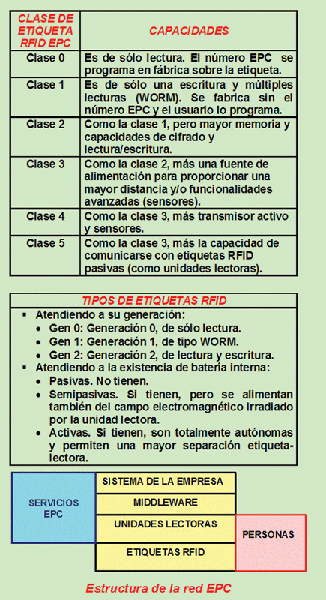 Basically, RFID technology integrates the following components: (1) RFID Tags. These are placed on or embedded in the objects or entities to be identified. A passive tag consists of a transponder and an RF coupling element. The coupling element has a coil-shaped antenna to capture the RF power, clock pulses, and data from the RFID reader. Each tag wirelessly transmits various types of information, such as the serial number, to the reader units that interrogate it. RFID tags can be of several types: passive (powered by the reader; the coupling type is inductive if they are LF or HF; if they are UHF or SHF, the coupling type is propagation), semi-passive (they have an internal battery but power from the reader unit), and active (they incorporate a battery and are self-contained; they are usually UHF or SHF microwave-based). (2) RFID Tag Readers or Interrogation Units. They can be portable or stationary; in the latter case, they are placed on gantries, doors, etc. They typically contain a transceiver, a control unit, a coupling element or antenna to interrogate the RFID tags, and a network interface. They implement a radio interface with the tags and a high-level interface with the back-end server to process the captured data. The maximum magnetic field that an inductively coupled RFID-HF reader (ISO14443/ISO15693) is allowed to emit at 13.56 MHz (ISM-licensed band) is 7.5 A/m. This value represents an upper limit under which all RFID systems must operate. The power relationship between a reader and a passive tag can be visualized as a transformer with a large separation between the primary and secondary windings. The way the magnetic field behaves with distance depends on the size of the transmitting antenna. If the current and the number of turns are kept constant, small antennas produce a high initial field that begins to decrease very rapidly. In contrast, a large antenna presents a relatively small initial field but it will remain constant at a greater distance. (3) Middleware.
Basically, RFID technology integrates the following components: (1) RFID Tags. These are placed on or embedded in the objects or entities to be identified. A passive tag consists of a transponder and an RF coupling element. The coupling element has a coil-shaped antenna to capture the RF power, clock pulses, and data from the RFID reader. Each tag wirelessly transmits various types of information, such as the serial number, to the reader units that interrogate it. RFID tags can be of several types: passive (powered by the reader; the coupling type is inductive if they are LF or HF; if they are UHF or SHF, the coupling type is propagation), semi-passive (they have an internal battery but power from the reader unit), and active (they incorporate a battery and are self-contained; they are usually UHF or SHF microwave-based). (2) RFID Tag Readers or Interrogation Units. They can be portable or stationary; in the latter case, they are placed on gantries, doors, etc. They typically contain a transceiver, a control unit, a coupling element or antenna to interrogate the RFID tags, and a network interface. They implement a radio interface with the tags and a high-level interface with the back-end server to process the captured data. The maximum magnetic field that an inductively coupled RFID-HF reader (ISO14443/ISO15693) is allowed to emit at 13.56 MHz (ISM-licensed band) is 7.5 A/m. This value represents an upper limit under which all RFID systems must operate. The power relationship between a reader and a passive tag can be visualized as a transformer with a large separation between the primary and secondary windings. The way the magnetic field behaves with distance depends on the size of the transmitting antenna. If the current and the number of turns are kept constant, small antennas produce a high initial field that begins to decrease very rapidly. In contrast, a large antenna presents a relatively small initial field but it will remain constant at a greater distance. (3) Middleware.
 It is located between the reading units and the company's information systems. It integrates the back-end servers, which are trusted entities that maintain a database containing information to identify the tags, including their identification numbers. The integrity of an RFID system depends on the correct behavior of the server. The server should be physically secured and protected against potential attacks. The middleware defines how and what information is shared between the RFID and the local databases, such as object references, descriptions, batch numbers, expiration dates, process status, etc. (4) The rest of the company's network where the information systems are located.
It is located between the reading units and the company's information systems. It integrates the back-end servers, which are trusted entities that maintain a database containing information to identify the tags, including their identification numbers. The integrity of an RFID system depends on the correct behavior of the server. The server should be physically secured and protected against potential attacks. The middleware defines how and what information is shared between the RFID and the local databases, such as object references, descriptions, batch numbers, expiration dates, process status, etc. (4) The rest of the company's network where the information systems are located.
Inherent Properties of RFID Technology:
If we compare RFID technology with barcode technology, we can observe, among others, the following advantages in favor of RFID technology: (1) It allows for the encryption of all or part of the information, thus ensuring that the information is not unprotected. (2) RFID tag reading is very fast and automated; it can read several tags simultaneously in a very short time. (3) It can identify hidden objects, for example, inside a box, shopping cart, container, or pallet without needing to open them. (4) It allows for the unique identification of objects by reading and writing data to each tag: serial number, batch number, user, etc. (5) High storage capacity, at least several kilobytes. (6) It is unaffected by humidity, dirt, or temperature; it can withstand harsh environments, being practically insensitive to its surroundings. (7) The reader can be programmed to search for a specific object, for example, a certain item of clothing of a specific size and model. (8) RFID technology allows for improvements to be introduced based on developments in the field of semiconductors.
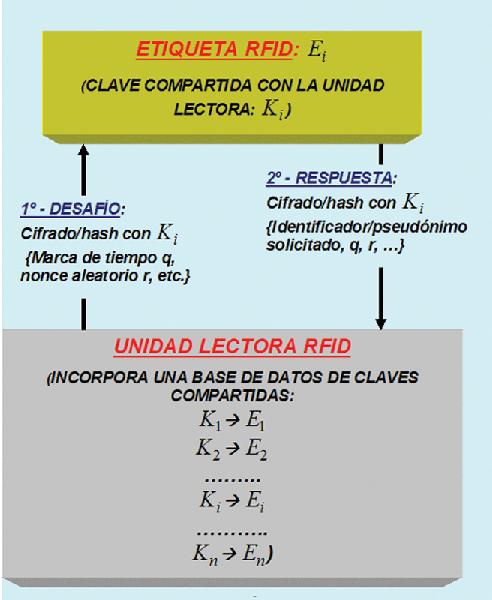
Privacy and Authentication Considerations: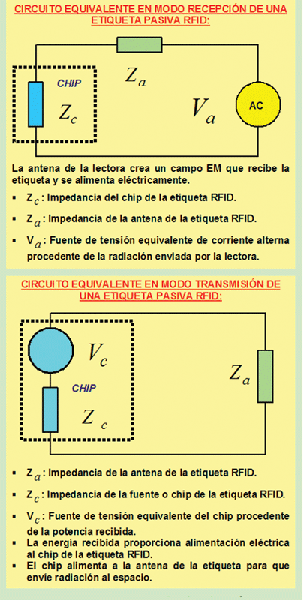 RFID tags respond to reader queries without notifying their owners or the entities carrying them, and most tags emit unique identifiers. This necessitates careful consideration of security aspects such as: (1) Location privacy. Multiple clandestine probe scans can reveal the location of the entity carrying the tag within a large facility where multiple reader units are deployed. (2) Data privacy. Certain tags, such as EPC (Electronic Product Code) tags, carry information about the products they bear. Entities carrying EPC tags are subject to clandestine inventory acquisition. (3) Privacy of RFID embedded in European banknotes. In 2001, the European Central Bank planned to embed RFID tags in banknotes as an anti-counterfeiting measure. However, the idea became increasingly impractical due to technical difficulties. (4) Privacy of RFID tags implanted in individuals. One example is VeriChip for the development of healthcare information systems. These cases have sparked criticism from privacy advocates. Foreign companies are already implanting RFID micro-tags in their employees for business purposes. (4) Privacy of RFID embedded in electronic passports. The ICAO (International Civil Aviation Organization) has issued guidelines for embedding RFID tags in passports. The US has adopted these standards. The European Union and other countries have already begun replacing traditional passports with electronic ones. In the EU, in 2009, it will be mandatory to embed personal data, photographs, and fingerprints in the RFID tag. (5) Authentication issues. Privacy concerns illegal reading units that clandestinely collect information from authorized RFID tags, while authentication refers to authorized reading units that detect clandestine and illegal RFID tags. EPC tags are vulnerable to simple counterfeiting attacks. They detect cloning through centralized and consistent data collection, but it is always possible.
RFID tags respond to reader queries without notifying their owners or the entities carrying them, and most tags emit unique identifiers. This necessitates careful consideration of security aspects such as: (1) Location privacy. Multiple clandestine probe scans can reveal the location of the entity carrying the tag within a large facility where multiple reader units are deployed. (2) Data privacy. Certain tags, such as EPC (Electronic Product Code) tags, carry information about the products they bear. Entities carrying EPC tags are subject to clandestine inventory acquisition. (3) Privacy of RFID embedded in European banknotes. In 2001, the European Central Bank planned to embed RFID tags in banknotes as an anti-counterfeiting measure. However, the idea became increasingly impractical due to technical difficulties. (4) Privacy of RFID tags implanted in individuals. One example is VeriChip for the development of healthcare information systems. These cases have sparked criticism from privacy advocates. Foreign companies are already implanting RFID micro-tags in their employees for business purposes. (4) Privacy of RFID embedded in electronic passports. The ICAO (International Civil Aviation Organization) has issued guidelines for embedding RFID tags in passports. The US has adopted these standards. The European Union and other countries have already begun replacing traditional passports with electronic ones. In the EU, in 2009, it will be mandatory to embed personal data, photographs, and fingerprints in the RFID tag. (5) Authentication issues. Privacy concerns illegal reading units that clandestinely collect information from authorized RFID tags, while authentication refers to authorized reading units that detect clandestine and illegal RFID tags. EPC tags are vulnerable to simple counterfeiting attacks. They detect cloning through centralized and consistent data collection, but it is always possible. 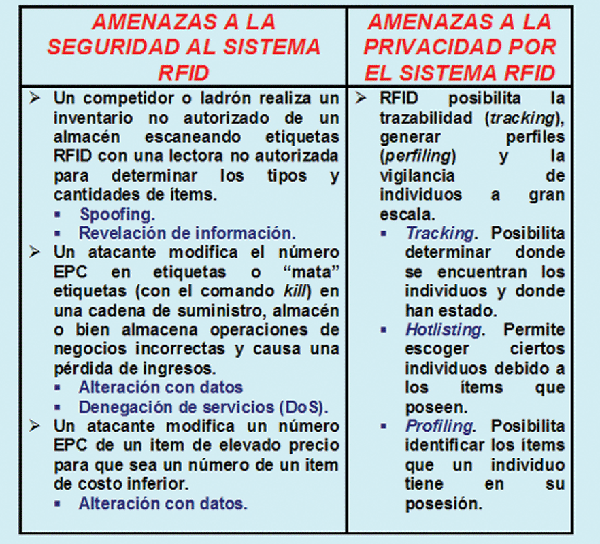 The main security objectives regarding RFID tags are: (1) Tags should not compromise the privacy of the wearers. Information should not be made available to unauthorized readers. Large-scale traceability networks should not be possible. (2) Tag wearers should be able to detect and disable the tags they are carrying. (3) The contents of private tags should be protected with encryption and access control. If public-key cryptography is used, low-cost computational technology should be employed in the tags, such as elliptic curve cryptography. (4) It should be very difficult to counterfeit (clone) RFID tags and readers. One solution to hide the 96-bit EPC code is to use Lagrange interpolation with second-degree polynomials (a.x² + b.x + secret) and create three 106-bit fragments from the 96-bit secret, which together form a 318-bit code.
The main security objectives regarding RFID tags are: (1) Tags should not compromise the privacy of the wearers. Information should not be made available to unauthorized readers. Large-scale traceability networks should not be possible. (2) Tag wearers should be able to detect and disable the tags they are carrying. (3) The contents of private tags should be protected with encryption and access control. If public-key cryptography is used, low-cost computational technology should be employed in the tags, such as elliptic curve cryptography. (4) It should be very difficult to counterfeit (clone) RFID tags and readers. One solution to hide the 96-bit EPC code is to use Lagrange interpolation with second-degree polynomials (a.x² + b.x + secret) and create three 106-bit fragments from the 96-bit secret, which together form a 318-bit code.
RFID Threat Identification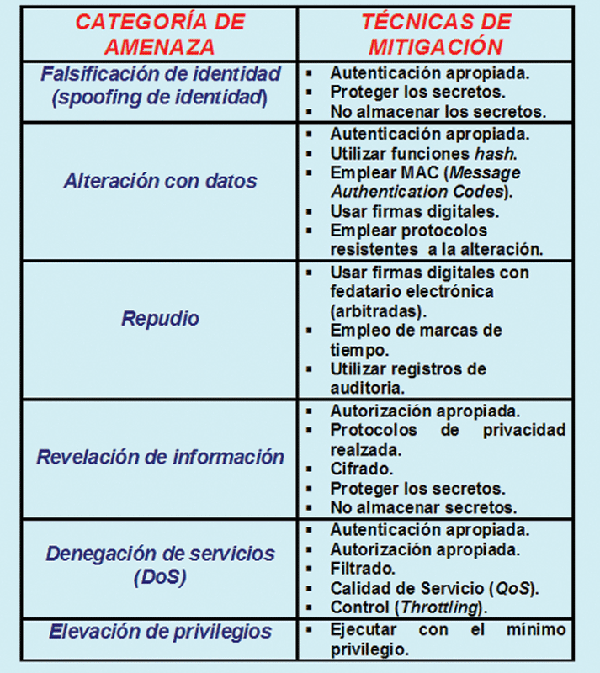 Some of the threats that can be identified regarding data security are: (1) Corporate espionage threat. Espionage through supply chain dynamics. (2) Trusted perimeter threat. Expanding the perimeter due to data sharing using networks. (3) Competitive marketing threat. This involves revealing a company's customers to competitors. (4) Infrastructure threat. Denial-of-service attacks, jamming, physical damage, counterfeit RFID tags, etc., are used. (5) RFID viruses. For example, attacks against RFID middleware software include SQL injection and buffer overflow attacks. The most relevant threats to personal privacy include: (1) Action threat. Determining actions based on the tags. (2) Association threat. Associating a person's identity with the tags. (3) Location threat. Determining the location of the RFID tag. (4) Preference threat. Revealing personal preferences. (5) Transactional threat. Determining transactional information. (6) Non-dissociation threat. It is difficult to dissociate data from identity. (7) RFID tracking and surveillance threat. Customers and companies have shared interests in making RFID systems secure. The most relevant threats to the RFID tags themselves include: (1) Eavesdropping between tag and reader. The backward channel distance can be about 5 meters between tag and reader, but the forward channel distance at which an eavesdropper can be located can be 100 meters. (2) Tracking or location. The unauthorized use of a tag identifier to obtain information about the location of a person or object. In a retail environment, a user can be associated with a product at the time of purchase. (3) Cloning/Replication.
Some of the threats that can be identified regarding data security are: (1) Corporate espionage threat. Espionage through supply chain dynamics. (2) Trusted perimeter threat. Expanding the perimeter due to data sharing using networks. (3) Competitive marketing threat. This involves revealing a company's customers to competitors. (4) Infrastructure threat. Denial-of-service attacks, jamming, physical damage, counterfeit RFID tags, etc., are used. (5) RFID viruses. For example, attacks against RFID middleware software include SQL injection and buffer overflow attacks. The most relevant threats to personal privacy include: (1) Action threat. Determining actions based on the tags. (2) Association threat. Associating a person's identity with the tags. (3) Location threat. Determining the location of the RFID tag. (4) Preference threat. Revealing personal preferences. (5) Transactional threat. Determining transactional information. (6) Non-dissociation threat. It is difficult to dissociate data from identity. (7) RFID tracking and surveillance threat. Customers and companies have shared interests in making RFID systems secure. The most relevant threats to the RFID tags themselves include: (1) Eavesdropping between tag and reader. The backward channel distance can be about 5 meters between tag and reader, but the forward channel distance at which an eavesdropper can be located can be 100 meters. (2) Tracking or location. The unauthorized use of a tag identifier to obtain information about the location of a person or object. In a retail environment, a user can be associated with a product at the time of purchase. (3) Cloning/Replication.
 Tags emitted by static identifiers are highly vulnerable. A thief can replace/rewrite a tag from an expensive product with one from a low-priced product. (4) Denial of Service (DoS). Applying conflicting RF signals can prevent legitimate tag communication. This is similar to RF jammers that block wireless communications near police cars, military tanks, vehicles of threatened individuals, some public buildings, etc. (5) Physical attacks. This involves probing a tag to extract its private data.
Tags emitted by static identifiers are highly vulnerable. A thief can replace/rewrite a tag from an expensive product with one from a low-priced product. (4) Denial of Service (DoS). Applying conflicting RF signals can prevent legitimate tag communication. This is similar to RF jammers that block wireless communications near police cars, military tanks, vehicles of threatened individuals, some public buildings, etc. (5) Physical attacks. This involves probing a tag to extract its private data.
Countermeasures against RFID tag attacks.
There is a growing number of countermeasures, but they offer only limited solutions: (1) An approach that involves permanently disabling or killing an RFID tag with the kill command, or a more subtle approach that involves putting the tag into a dormant state. This can currently be done on EPC Class-1 Gen-2 tags. When an EPC RFID tag receives a kill command from a reader, it becomes permanently inoperative. The kill command is protected with a PIN (Personal Identifier Number) or password; in Class 0 EPCs it is 24 bits, in Class 1 EPCs it is 8 bits, and in HF type EPCs it is 24 bits.
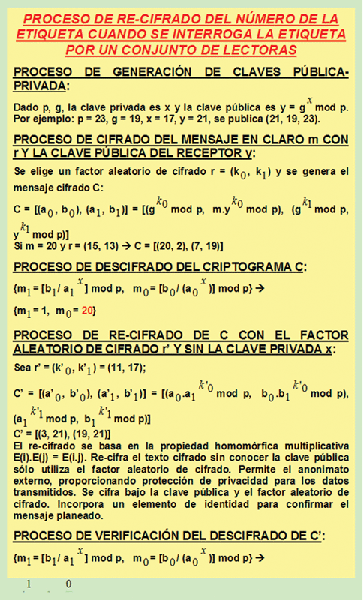
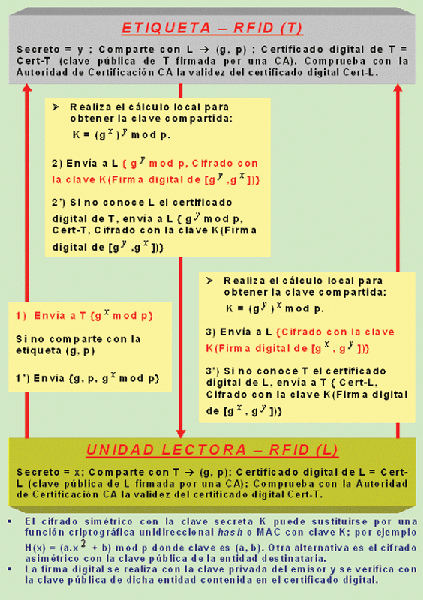
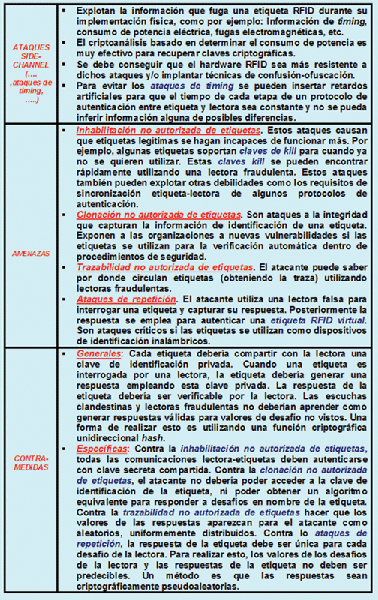 This method eliminates all the potential benefits that could be obtained from RFID technology after the purchase of the item carrying the tag. For example, if we approach a store window with a live tag on a purchased garment, we could see personalized recommendations on a screen to complement that garment. (2) Renaming approach. RFID tags contain a set of pseudonyms, so they emit a different one each time they are interrogated by a reading unit. To control a tag's response and prevent malicious readers from quickly extracting all available pseudonyms in a single scan, the tag progressively slows its response in the case of a rapid sequence of interrogations. (3) Re-encryption approach. See Figure 4. (4) Proxy approach. Customers carry their own privacy enforcement devices called proxies. These can be of two types: (a) Watchdog tags. These are RFID privacy auditing systems that monitor the tag scanning environment and collect information about the reading units. (b) RFID Guardian or REP (RFID Enhancer Proxy). This is a battery-powered personal RFID firewall. It acts as an intermediary between the reader's request and the tag's response, selectively simulating the tags under its control; for example, it may not respond to a reader because it is unauthorized. It can implement sophisticated privacy policies. The Guardian or REP acquires and releases control of the tags, PINs, and associated keys. (5) Partial antenna clipping approach. This involves physically cutting off part of the antenna, for example, with scissors, to reduce the range from several meters to a few centimeters. This technique can help protect data access since an eavesdropper would have to get very close to the tag and the person carrying it to steal information. (6) Approach based on enclosing the tag in a metallic or plastic sleeve, which acts as a Faraday cage for electromagnetic shielding. Transparent EMI-suppressing plastic can be used to cover RFID tags, achieving attenuation of up to 30 dB and an EMI shielding effectiveness of 35 dB in the 30 MHz to 1.5 GHz range, and 25 dB and an EMI shielding effectiveness of 30 dB in the 1.5 GHz to 4 GHz range. (7) Watchdog tag approach. This type of RFID tag displays reads and writes that would otherwise be invisible. It recognizes the start and stop pulses sent by the reading units and even displays the agreed-upon downloaded data sizes. This approach increases the visibility of access to personal data. (8) RFDump (http://www.rf-dump.org). This is an open-source software tool for ISO-15693 and ISO-14443 (13.56 MHz) RFID reading units. It reads/writes data to RFID tags. It integrates a cookie feature that adds a cookie to the tag and automatically increments a counter when the RFID tag is within a reader's range. It tracks the number of times a shopper enters a reader's range or picks up a product. (9) An approach based on preventing them from being read. Using some type of EMI shielding. Another method is to generate interference (jamming) to inhibit communications, for example, by broadcasting "0" and "1" in response to any reader request. This latter method disables all RFID tags, even those in legitimate applications. (10) Enacting laws that govern the use of RFID. With policy and legislation. (11) Preventing unauthorized parties from understanding the tag-reader communication.
This method eliminates all the potential benefits that could be obtained from RFID technology after the purchase of the item carrying the tag. For example, if we approach a store window with a live tag on a purchased garment, we could see personalized recommendations on a screen to complement that garment. (2) Renaming approach. RFID tags contain a set of pseudonyms, so they emit a different one each time they are interrogated by a reading unit. To control a tag's response and prevent malicious readers from quickly extracting all available pseudonyms in a single scan, the tag progressively slows its response in the case of a rapid sequence of interrogations. (3) Re-encryption approach. See Figure 4. (4) Proxy approach. Customers carry their own privacy enforcement devices called proxies. These can be of two types: (a) Watchdog tags. These are RFID privacy auditing systems that monitor the tag scanning environment and collect information about the reading units. (b) RFID Guardian or REP (RFID Enhancer Proxy). This is a battery-powered personal RFID firewall. It acts as an intermediary between the reader's request and the tag's response, selectively simulating the tags under its control; for example, it may not respond to a reader because it is unauthorized. It can implement sophisticated privacy policies. The Guardian or REP acquires and releases control of the tags, PINs, and associated keys. (5) Partial antenna clipping approach. This involves physically cutting off part of the antenna, for example, with scissors, to reduce the range from several meters to a few centimeters. This technique can help protect data access since an eavesdropper would have to get very close to the tag and the person carrying it to steal information. (6) Approach based on enclosing the tag in a metallic or plastic sleeve, which acts as a Faraday cage for electromagnetic shielding. Transparent EMI-suppressing plastic can be used to cover RFID tags, achieving attenuation of up to 30 dB and an EMI shielding effectiveness of 35 dB in the 30 MHz to 1.5 GHz range, and 25 dB and an EMI shielding effectiveness of 30 dB in the 1.5 GHz to 4 GHz range. (7) Watchdog tag approach. This type of RFID tag displays reads and writes that would otherwise be invisible. It recognizes the start and stop pulses sent by the reading units and even displays the agreed-upon downloaded data sizes. This approach increases the visibility of access to personal data. (8) RFDump (http://www.rf-dump.org). This is an open-source software tool for ISO-15693 and ISO-14443 (13.56 MHz) RFID reading units. It reads/writes data to RFID tags. It integrates a cookie feature that adds a cookie to the tag and automatically increments a counter when the RFID tag is within a reader's range. It tracks the number of times a shopper enters a reader's range or picks up a product. (9) An approach based on preventing them from being read. Using some type of EMI shielding. Another method is to generate interference (jamming) to inhibit communications, for example, by broadcasting "0" and "1" in response to any reader request. This latter method disables all RFID tags, even those in legitimate applications. (10) Enacting laws that govern the use of RFID. With policy and legislation. (11) Preventing unauthorized parties from understanding the tag-reader communication.
 Using cryptographic techniques and/or concealing the communication itself via subliminal channels, both of which require hardware not feasible in very low-cost tags, other methods use unidirectional cryptographic hash functions and pseudorandom number generators. Another method employed is based on measuring signal strength over distance. It is known that most hostile reads occur when the attacker is physically distant. By measuring signal strength and performing noise analysis, the distance to the reader can be estimated. Another method is physical protection with security cameras, sensors, etc.
Using cryptographic techniques and/or concealing the communication itself via subliminal channels, both of which require hardware not feasible in very low-cost tags, other methods use unidirectional cryptographic hash functions and pseudorandom number generators. Another method employed is based on measuring signal strength over distance. It is known that most hostile reads occur when the attacker is physically distant. By measuring signal strength and performing noise analysis, the distance to the reader can be estimated. Another method is physical protection with security cameras, sensors, etc.
This article is part of the activities developed within the LEFIS-APTICE (funded by Socrates 2005-2007. European Commission).
LITERATURE.
- Areitio, J. “Privacy and protection, key elements for RFID technology”. Gigatronic Magazine. No. 44. March 2007.
- Areitio, J. “Need to complement firewalls: intrusion detection and prevention systems and vulnerability assessment”. Conectrónica Magazine. No. 101. October 2006.
- Areitio, J. “Analysis, synthesis and applications of cryptographic hash function technology”. Conectrónica Magazine. No. 108. June 2007.
- Areitio, J. “Security considerations regarding RFID technology”. Conectrónica Magazine. No. 105. March 2007.
- Areitio, J. “Information Security”. Cengage Learning. 2008.
- Thornton, F. and Lathem, C. “RFID Security”. Syngress. 2006.
- Cole, PH and Ranasinghe, DC “Networked RFID Systems and Lightweight Cryptography: Raising Barriers to Product Counterfeiting”. Springer. 2007.
- Reese, R. “Network Security”. John Wiley & Sons, Inc. 2007.
- Minoli, D. “Information Security Risk Management.” John Wiley & Sons, Inc. 2006.
- Kadrich, M. “Endpoint Security”. Addison-Wesley. 2007.
Prof. Dr. Javier Areitio Bertolín. Professor at the Faculty of Engineering. ESIDE. Director of the Networks and Systems Research Group. University of Deusto.