 In recent years, near-field communication (NFC) technology has been refined and simplified, resulting in the increasing number of gadgets and mobile devices (smartphones, tablet PCs, PDAs, PCs, iPods/iPads, smartcards, digital cameras, kiosks, etc.) that incorporate NFC functionality and can read conventional passive RFID tags or RFID tags with battery assist (BAP), capable of reading at greater distances. According to the CEO of Gamma Solutions, 2012 could be the year NFC technology takes off, with the diversification of these services becoming significant, even in Spain. Social media managers know their future lies in mobility. According to market research by ABI Research (http://www.abiresearch.com), 30% of all mobile phones in 2011 were expected to have NFC functionality, and it was estimated that there would be approximately 450 million NFC-enabled mobile phones in use.
In recent years, near-field communication (NFC) technology has been refined and simplified, resulting in the increasing number of gadgets and mobile devices (smartphones, tablet PCs, PDAs, PCs, iPods/iPads, smartcards, digital cameras, kiosks, etc.) that incorporate NFC functionality and can read conventional passive RFID tags or RFID tags with battery assist (BAP), capable of reading at greater distances. According to the CEO of Gamma Solutions, 2012 could be the year NFC technology takes off, with the diversification of these services becoming significant, even in Spain. Social media managers know their future lies in mobility. According to market research by ABI Research (http://www.abiresearch.com), 30% of all mobile phones in 2011 were expected to have NFC functionality, and it was estimated that there would be approximately 450 million NFC-enabled mobile phones in use.
According to the research firm Frost & Sullivan, speaking at the 2010 NFC Forum, one-third of all mobile phones will be equipped with NFC. Companies like Amazon and Google (with its "Google Wallet," its mobile payment system using NFC) have adopted NFC. NFC technology, increasingly important for ubiquitous computing, is an extension of the ISO 14443 proximity card standard (contactless card, RFID) that combines the interface of a smart card and a reader into a single device with countless practical implications. A Privacy Survey conducted by Nokia Siemens Networks between August and September 2009 revealed that the two biggest concerns for people using mobile phones and the internet are, first, identity theft, followed by unauthorized access to bank accounts. Some manufacturers involved in integrating or that have already incorporated NFC functionality into their mobile phones include: Google Nexus S, Samsung with Android 4.0, Nokia (C7 / Galaxy SII with Android 4.0 / S5230NFC / 6212Classic / 6131NFC), Motorola (L7-SLVR, MC75AHF), Casio IT-800RGC-35, RIM (Research In Motion) Bold 9900 and 9930 (the manufacturer of BlackBerry phones), Apple's upcoming iPhone 5, etc. Some operating systems that will incorporate or will incorporate NFC functionality include Android, Microsoft Windows Phone 7, Symbian, BlackBerry RIM 7.0, Windows Mobile 6 Professional, Apple iOS, etc.
NFC Interface Modes. Communication Configurations.
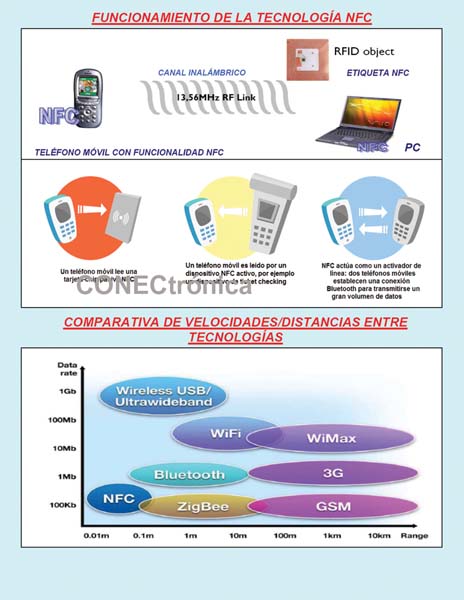
The NFC interface can operate in several modes. The modes are distinguished based on whether the device generates its own RF field or recovers energy from the RF field generated by another device. Based on this, NFC devices can be classified into two types: (1) Active Device. If the device generates its own electromagnetic field, it is called an active device. Active devices typically have a power source. (2) Passive Device. If the device does not generate its own electromagnetic field, it is called a passive device. Passive devices generally do not have a power source (e.g., a smart card without a galvanic connection).
In active mode, data is sent using ASK modulation, meaning the base RF signal (13.56 MHz) is modulated with the data. If the modulation rate is 106 kbaud, the encoding scheme is modified Miller with a 100% modulation rate; if the modulation rate is higher, Manchester encoding is applied with a 10% modulation rate.
When two devices A and B communicate, three different communication configurations are possible:
(1) Active-active. When a device sends data, it generates an RF field. When a device is waiting for data, it does not generate an RF field. Therefore, the RF field is generated alternately by each communicating device A and B.
(2) Active-passive. The RF field is generated only by device A.
(3) Passive-active. The RF field is generated only by device B.
NFC Device Roles and Applications:
There are two roles an NFC device can play in communication. NFC is based on a message-response mechanism, meaning that device A sends a message to device B, and device B returns a response. It is not possible for B to send data to A without first receiving a message from A. The role of device A that initiates the data exchange is called the initiator, and the role of the other device is called the target.
The possible combinations of active/passive modes with initiator/target roles are: (1) Active-initiator. Possible. (2) Active-target. Possible. (3) Passive-initiator. Not possible. (4) Passive-target. Possible.
NFC technology is being incorporated into a growing number of sectors and application areas such as: mobile micropayments (which involves using a mobile phone to make payment transactions in which money or funds are transferred from a "payer" to a "receiver" through an intermediary such as a "financial institution," "private company," or directly without an intermediary), e-wallets, mobile ticketing, smart posters, WiFi/Bluetooth pairing (to easily initiate this type of broadband connectivity), check-in, mobile identification, service initiation, tourism applications, mobile voting, mobile marketing, mobile coupons, cultural applications (access to shows), commercial applications, peer-to-peer (P2P) information sharing, education, industry, leisure activities, automotive applications (access keys and vehicle ignition), general information access services, healthcare, access keys to data centers/homes, and mobile ticketing (in public transport as an extension of existing contactless infrastructure such as a mobile phone). Smart poster (mobile phone is used to read RFID tags on street billboards), m-payments (the device acts as a credit/debit card), Bluetooth pairing (the process of activating Bluetooth on both ends, searching, waiting, pairing and authorization is replaced simply by bringing the mobile phones close together), electronic ticketing (airline tickets, concert/event tickets, electronic money, travel cards, identity documents, mobile commerce), electronic keys (replaces physical keys for vehicles, home/office, hotel rooms, etc.), NFC can be used to set up and initiate other wireless network connections such as WiFi, Bluetooth, etc.
Among others, the following usage modes can be identified:
Card emulation. The NFC device behaves like an existing wireless card.
Reader mode. The NFC device is active and reads a passive RFID tag, for example, for interactive advertising.
P2P mode. Two NFC devices communicate with each other and exchange information.

NFC Characterization.
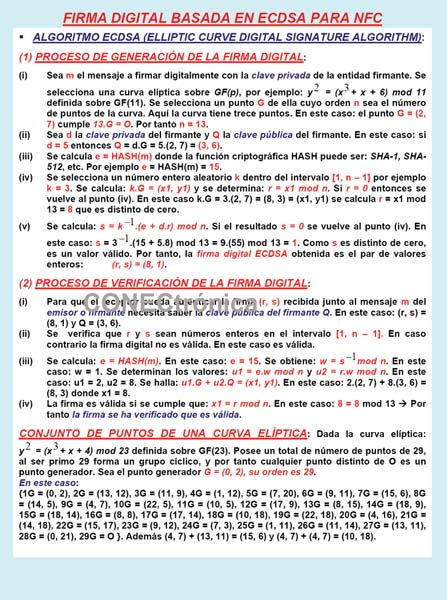
NFC standards were launched by Sony, Philips, and Nokia in March 2004 as an interconnection technology, with the NFC Forum established as the interoperability body. NFC is a bidirectional proximity coupling technology (ISO 18092) based on the ISO 14443 RFID standard. It supports the MIFARE standard used in Europe and the US and the FeliCa standard used in Asia and Japan. It operates within the globally available unlicensed ISM RF band at 13.56 MHz and supports data modulation rates of 106, 216, and 424 kbaud (narrowband). The typical communication distance is between 2 and 4 centimeters, but can reach up to 20 cm or more. Physically, a mobile phone with NFC functionality contains special hardware circuitry, firmware, and specific software. Eavesdropping attacks can be carried out from 10 meters or more, depending on the antenna and amplifier available to the attacker/adversary.
NFC operating modes
There are three operating modes for devices that support NFC functionality:
(1) R/W (Reader/Writer) or PCD mode. In this mode, an NFC device (mobile phone) acts as a PCD (Proximity Coupling Device) and can read and write data stored on NFC-compliant passive transponders (such as smart cards, external RF/NFC tags). It complies with the ISO 14443 standard. An example is the interaction between an NFC mobile phone and a battery-less RFID object. Currently deployed services primarily use the PCD reader/writer mode. Some applications include SmartPoster, configuring Wi-Fi, configuring ringtones, etc.
(2) Card-Tag Emulation or PICC mode. In this mode, an NFC device acts as a PICC (Proximity Inductive Coupling Card). The reading unit cannot distinguish between a smart card and an NFC card emulation. The mobile phone can contain multiple smart cards (smartcard chips). It complies with the ISO 14443 standard. In this case, the mobile phone behaves like a smart card.
(3) P2P (peer-to-peer) or NFC data exchange mode. In this mode, two NFC devices (e.g., a mobile phone and a PC) can communicate bidirectionally to transfer arbitrary data. It complies with the ISO 18092 standard. Some applications include P2P payments, vCards, contacts, etc.
NFC Assessment:
NFC represents the second generation of contactless proximity technology, going beyond RFID. It supports P2P communication for file sharing and allows users to access value-added services from anywhere, at any time, and on any NFC-enabled mobile device (obviously, for augmented reality applications, a tablet PC would be better than a smartphone due to screen size limitations). NFC is a narrowband wireless technology for short-range devices, designed to exchange data, initiate connections with other broadband networks (such as Wi-Fi and Bluetooth), and act as security keys for accessing vehicles and services such as cashless payments, ticket payments for public transport, cinemas, etc., online entertainment, mobile marketing, and access control. After identifying the lack of security and privacy mechanisms in NFC, the obvious conclusion is the existence of threats such as eavesdropping, data modification, unavailability, and various types of man-in-the-middle (MITM) attacks and session hijacking. This leads us to integrate cryptographic mechanisms appropriate to the assumed security-privacy risk.
Final Considerations
Our research group has been working in the world of RFID-NFC technology for over fifteen years. Applications have been developed for embedded electronics, smartphones, and related mobile devices. It is clear that NFC technology provides and will continue to provide countless benefits in a wide variety of sectors, but it should not be forgotten that NFC was born without security and privacy protection mechanisms; therefore, it is absolutely necessary to integrate it with professional mechanisms where asymmetric cryptography plays a prominent role.
This article is part of the activities developed within the LEFIS-Thematic Network.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto.
Bibliography
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2012.
- Areitio, J. “Analysis of economic feasibility in the area of information protection”. Conectronica Magazine. No. 154. February
- Areitio, J. “Information security and privacy risk management”. Conectronica Magazine. No. 155. March 2012.
- Ahson, SA and Ilyas, M. “Near Field Communications Handbook”. Auerbach Publications. 2011.
- Finkenzeller, K. “RFID Handbook: Fundamentals and Applications in Contactless Smart Cards. Radio Frequency Identification and Near-Field Communication”. Wiley. 2010.
- Lauger, J. “2009 First International Workshop on Near Field Communication”. IEEE. 2009.
- Kiayias, A. and Pehlivanoglu, S. “Encryption Mechanisms Digital Content Distribution”. Springer. 2010.
- NFC Forum: http://www.nfc-forum.org/
- Vacca, JR “Network and System Security”. Syngress. 2010.
- Fry, C. and Nystrom, M. “Security Monitoring”. O'Reilly Media, Inc. 2009.



