Characterization and Considerations Regarding Phishing:
Phishing can be defined as a form of criminal activity that uses social engineering techniques and is characterized by attempting to fraudulently acquire sensitive information, such as passwords, credit card numbers or details, private personal information, etc., by impersonating a trusted person or business/institution in an apparently official electronic communication such as email (SMTP/POP3/IMAP4), instant messaging (IM/MSN/ICQ), the Web (HTTP/HTTPS), telephony (landline, mobile, VoIP/SIP-based, SMS, MMS), etc. Phishing has become a rapidly growing security problem, and attacks are becoming increasingly sophisticated. In a basic attack, the victim receives an email that appears to be from a trusted institution. This email often informs the victim of some kind of problem with their account (imminent saturation of email storage, password expiration, possible account or credit card breach, intruder detection at their home protected by an anti-theft service provider, alert at their healthcare facility, etc.) and demands immediate action. The victim, using a malicious link, is directed to a website that perfectly mimics the official website of the trusted institution being impersonated. This website then displays a screen prompting the victim to enter their username, password, personal information, and so on.
There are two variants: (1) Passive. The attacker collects the victim's information for later exploitation or to sell it to third parties. (2) Active. The attacker relays the victim's information to the legitimate institution and drains the victim's account in real time. Phishing can be based on email (SMTP/POP3/IMAP4, VoIP), the web (HTTP/HTTPS, webmail, social media), landline/mobile telephony, SMS/MMS, etc. Phishing can be used for identity theft (personal or institutional), where digital identity can refer to a natural person, a legal entity (company, institution, etc.), or a computer/programmable logic controller in an industrial environment or critical infrastructure. Digital identity is a set of attributes, some of which can change over time and others can be certified by third parties; for example, name and surname, age, national identity document number, user identifiers, medical information, authentication methods (traditional or federated), etc. Since it is very difficult, if not impossible, to erase the digital data used, digital identities tend to grow and never shrink.
Phishing Approaches
: Phishers use various techniques such as: (i) Using visual elements from the impersonated trusted destination site. (ii) Using DNS-based tricks such as trap URLs: www.ebay.com.kr, www.ebay.com@191.175.114.32
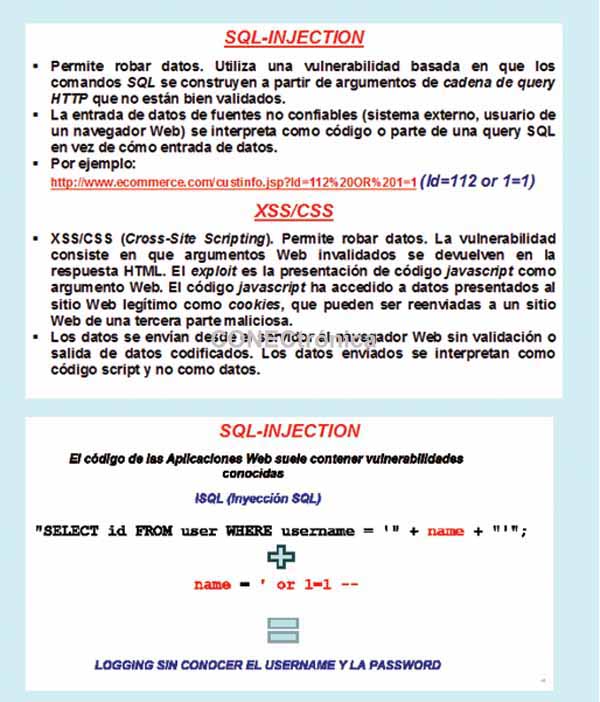
(URLs containing @, in this case the browser redirects to the address 191.175.114.32 using www.ebay.com as the name, which opens even though the page doesn't exist), www.gooogle.com (misspelled URLs), www.ebay-members-security.com (not belonging to www.ebay.com), using Unicode attacks, using international domain names. (iii) Using JavaScript attacks. For example, falsifying and creating a fake padlock that appears at the bottom of the browser to give the impression of using SSL/TLS, or falsifying the URL in the web address bar. (iv) Use of digital certificates. Phishers can acquire certificates for domains they own. Certificate authorities sometimes make mistakes. (v) Use of CSS/XSS. This redirects the user. Some more advanced phishing techniques rely on: (a) Using better victim selection. (b) Using socially conscious attacks, for example, the email address appears to be from someone the victim knows. (c) Using context-aware attacks, for example, receiving a message that says "your eBay bid has won" or that "the books on your Amazon shopping list are on sale." From the user's perspective, we encounter the following problems: (1) Security is a secondary objective for many users. (2) Users choose weak passwords that are easily compromised. (3) Users are unable to analyze URLs, domain names (especially international ones with Cyrillic, Chinese, Arabic, etc. characters), or PKI (Public Key Infrastructure) digital certificates. (4) Users are inundated with warnings and pop-ups, and either ignore them (allowing man-in-the-middle attacks) or are tricked (if a pop-up appears with a warning saying "your computer may be infected," quickly click "yes" to scan it; what you are actually doing is downloading a Trojan).
Anti-phishing Approaches
. Some anti-phishing approaches are: (1) Heuristics. For example, using tools such as Spoofguard, Trustbar, eBay Toolbar, Spoofstick, etc. Some recent studies indicate that users ignore toolbar warnings. (2) Modified Passwords. For example: (i) SSO (Single Sign-On). Requires users to trust one institution for all their passwords. An authentication problem still exists. It is reckless that mutual authentication is not currently used in all communication interactions. (ii) PwdHash. An acceptable approach but vulnerable to pharming, DNS spoofing, and dictionary attacks. (iii) OTP (One-Time Passwords). For example, scratch cards, RSA SecurID, but these are vulnerable to active MITM attacks. (3) Origin Authentication. For example: Dynamic Security Skins, Passmark, Petname, etc. All these approaches rely on user diligence; a single mistake can lead to account compromise. It is crucial to emphasize that security should not depend entirely on fallible users; that the system must be secure by default; and that the design must be robust against potential user errors (technology should be used to monitor the user's level of awareness, regardless of their role: manager, administrator, supervisor, employee, guest, etc.).
 Some phishing prevention goals are: (1) Ideally, to ensure that sensitive/confidential/personal user data only reaches the intended recipient. (2) Practically, to prevent phishers from viewing or modifying user accounts and to reduce the effectiveness of attacks. To achieve this: (a) Counteract errors by backing up user accounts even when mistakes are made. (b) Use mobile devices to establish an authenticator that the user cannot easily reveal. (c) Protect against man-in-the-middle (MITM) attacks. (d) Defend against keyloggers (software and hardware), for example, by using virtual keyboards/mice and detection and removal tools such as antispyware/anti-Trojan software. (e) Provide mutual authentication both server-to-user and user-to-server. (f) Avoid browser interface dependencies, as these are easily vulnerable. Intrusion-based Enterprise (IBE) can be used. Identity-based encryption (IBE) is a more agile variant of public-key or asymmetric encryption (PKI) where a user's identity (e.g., their email address, national identity card/social security number, a photograph contaminated with a steganogram that personalizes them, their real-time video chat, a biometric sample, etc.) is used instead of the user's public key (or digital certificate signed by a Certification Authority). In this case, a trusted third party must be responsible for converting the user's identity into their private key in real time.
Some phishing prevention goals are: (1) Ideally, to ensure that sensitive/confidential/personal user data only reaches the intended recipient. (2) Practically, to prevent phishers from viewing or modifying user accounts and to reduce the effectiveness of attacks. To achieve this: (a) Counteract errors by backing up user accounts even when mistakes are made. (b) Use mobile devices to establish an authenticator that the user cannot easily reveal. (c) Protect against man-in-the-middle (MITM) attacks. (d) Defend against keyloggers (software and hardware), for example, by using virtual keyboards/mice and detection and removal tools such as antispyware/anti-Trojan software. (e) Provide mutual authentication both server-to-user and user-to-server. (f) Avoid browser interface dependencies, as these are easily vulnerable. Intrusion-based Enterprise (IBE) can be used. Identity-based encryption (IBE) is a more agile variant of public-key or asymmetric encryption (PKI) where a user's identity (e.g., their email address, national identity card/social security number, a photograph contaminated with a steganogram that personalizes them, their real-time video chat, a biometric sample, etc.) is used instead of the user's public key (or digital certificate signed by a Certification Authority). In this case, a trusted third party must be responsible for converting the user's identity into their private key in real time.
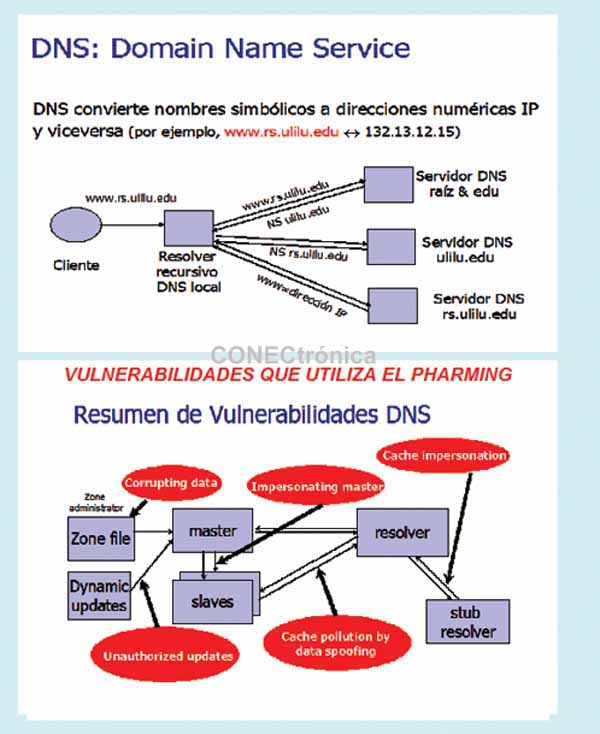
Approaches to Pharming:
Many anti-phishing defenses rely on DNS. Pharming can bypass these defenses by poisoning the DNS cache and/or spoofing DNS responses. This means that when our browser requests, for example, the address www.paypal.com, the attacker will have tricked it into responding with an IP address from the website they control, such as 138.6.6.6. Dynamic pharming provides fake DNS mappings for a trusted server, deceiving the user into downloading a malicious script. It also forces the user to download content from the real server by temporarily providing the correct DNS mapping. The malicious script and the content have the same origin.
There are basically two techniques through which pharming can be carried out: (1) Using viruses/malware/malicious code in emails. An innocent (albeit somewhat suspicious) email may contain an image that, when opened/viewed in your email program, actually downloads a virus to your computer. The virus rewrites the "hosts" file (static name resolution) that normally translates standard URLs (like www.google.com) into IP addresses understood by your computer (like 132.45.13.7). A computer with a forged hosts file will go to the wrong website even if the user types the correct URL. (2) Using DNS poisoning (dynamic name resolution). This is the most malicious threat because it works even with the best antivirus software. It alters the mapping between web URLs/email addresses and IP addresses.

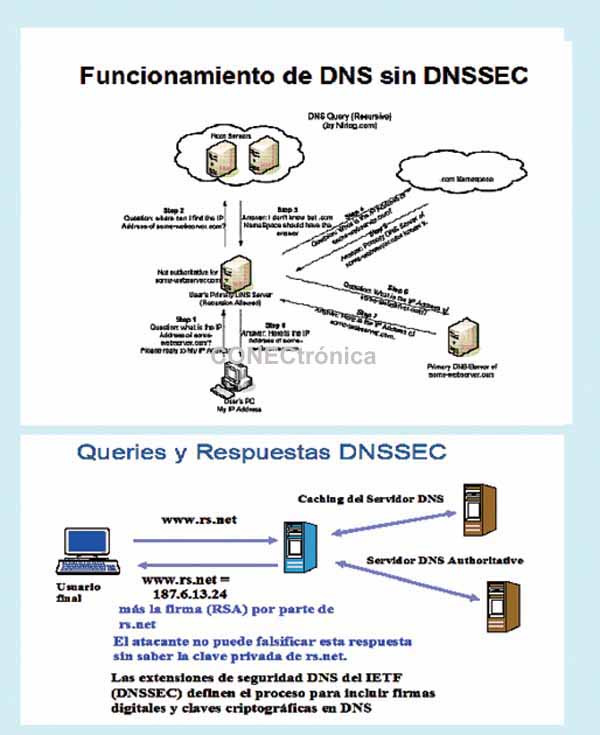
Pharming Prevention:
Some techniques used are: (i) Servers should add another layer of authentication, proving their identity and establishing a link of trust between the user and the server. This would require the website to obtain a digital certificate from a reputable certificate authority such as VeriSign/Izenpe. Most web browsers already have the ability to verify the presence of valid server certificates. The problem lies on the server side. Some sites already offer certificates; when visiting these sites, the user sees a dialog box asking if they wish to trust the certificate. If the certificate name does not match the intended site, a problem is detected, and the user should leave. Perhaps your destination website (your bank URL) has been hijacked. If the certificate is valid, it is saved so that the next time the browser navigates to the correct address, the user can log in to the site. (ii) Widespread use of DNSSEC, which can cryptographically authenticate the URL/email address to IP address correspondence. However, it is unable to defend against DoS/DDoS attacks. There are three versions: (a) PK-DNSSEC. Based on asymmetric public-key cryptography. (b) SK-DNSSEC. Based on symmetric secret-key cryptography, it uses a nonce (a one-time, ephemeral value) in each message to prevent replay attacks. (c) Hybrid approach. Combines both technologies, and the DNS root zone server has a public key.
Final Considerations
Our research group has been working for over twenty years in the area of synthesis, analysis, and evaluation of protection mechanisms against the theft of confidential/sensitive data through various wired and wireless network-based approaches.
This article is part of the activities developed within the LEFIS-Thematic Network.
Bibliography
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2010.
- Areitio, J. and Areitio, A. “New approaches in the analysis of firewall technology, an essential component for network security”. Conectrónica Magazine. No. 122. November 2008.
- Aycock, J. “Spyware and Adware”. Springer, 2010.
- Corby, MJ “Complete Guide to Preventing Data Loss”. CRC Press. 2011.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto.
Prof. Dr. Ana Areitio Bertolín – E.Mail:
Applied Computing Laboratory. University of the Basque Country (UPV/EHU)