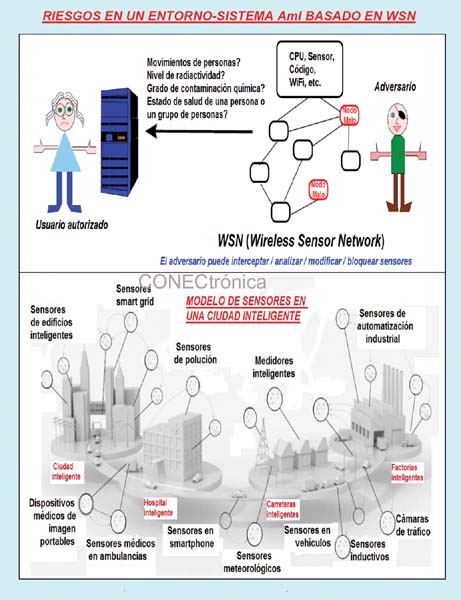
 Ubiquitous computing integrates sensors and other miniature computing devices (RFID/NFC tags, ZigBee micronodes, embedded electronics in artificial prostheses for people and animals, etc.) into everyday objects. Ubiquitous communication enables mobile communication as well as the interaction of clusters of devices. User-friendly interfaces allow for human-like interaction with these devices. Applications in AmI environments are evolving into AmI ecosystems without fixed architectures, controlled boundaries, or ownership, thus becoming complex, self-organizing systems. Ubiquitous computing and AmI systems enable a technological world that is present everywhere, at all times, in the form of intelligent and responsive devices (with sensors) that communicate with each other and provide personalized services with increasingly sophisticated interfaces. The openness of these ubiquitous and AmI systems makes them especially vulnerable to all kinds of attacks, as well as unauthorized access to data. This situation underscores the urgent need to professionally address cybersecurity and cyberprivacy, the subject of this article.
Ubiquitous computing integrates sensors and other miniature computing devices (RFID/NFC tags, ZigBee micronodes, embedded electronics in artificial prostheses for people and animals, etc.) into everyday objects. Ubiquitous communication enables mobile communication as well as the interaction of clusters of devices. User-friendly interfaces allow for human-like interaction with these devices. Applications in AmI environments are evolving into AmI ecosystems without fixed architectures, controlled boundaries, or ownership, thus becoming complex, self-organizing systems. Ubiquitous computing and AmI systems enable a technological world that is present everywhere, at all times, in the form of intelligent and responsive devices (with sensors) that communicate with each other and provide personalized services with increasingly sophisticated interfaces. The openness of these ubiquitous and AmI systems makes them especially vulnerable to all kinds of attacks, as well as unauthorized access to data. This situation underscores the urgent need to professionally address cybersecurity and cyberprivacy, the subject of this article.
Technical Considerations:
One of the key considerations when thinking about the present and future of our lives, increasingly immersed in ambient intelligence systems, is cybersecurity and cyberprivacy. No matter how fascinating, beneficial, and useful AMI systems may seem, the lack of adequate cybersecurity and privacy mechanisms can have consequences that overshadow the rational adoption of these systems. Risk analysis must be conducted not only on the three pillars of AMI (pervasive networking, interfaces, and ubiquitous computing) but also at a global level, considering the unimaginable combination and enrichment resulting from their interaction.
Consequently, the urgent prerequisite for the development of ambient intelligence is the secure and reliable interaction of the different components and devices of ambient intelligence systems in all contexts where they may occur (business, hospitals, factories/industries, research/D&I, homes, transportation, and society in general).
 Security and privacy countermeasures for AmI environments must address a combination of heterogeneity, mobility, scalability, dynamic reaction, adaptation to context, a huge number of devices, and a lack of control over some pieces of software, communications infrastructure, and hardware devices, so that security must be more than predefined trust relationships about control of the system or its components.
Security and privacy countermeasures for AmI environments must address a combination of heterogeneity, mobility, scalability, dynamic reaction, adaptation to context, a huge number of devices, and a lack of control over some pieces of software, communications infrastructure, and hardware devices, so that security must be more than predefined trust relationships about control of the system or its components.
Ambient Intelligence (AmI) should be a human-centered approach that combines ubiquitous/pervasive, proactive, and ambient computing and communications with social interfaces. It should operate from any location at any time and be embedded in all types of objects. It utilizes smart materials (artificial skins, nanotechnology-based walls and floors), is aware of people's presence and personalities, engages in intelligent dialogues, and is unobtrusive—ideally invisible. Interaction should be stress-free and even relaxing, ensuring the user feels comfortable with the interface and avoiding complex learning curves.
Intelligent User Interfaces (IUIs) utilize ICTs to create a user-friendly, intelligent interface that supports human interaction. By using technology embedded in various objects and electronic devices, a wide range of possibilities can be created. IUI technology represents a system implemented within an environment that is aware of its different components as well as its user. The goal is to facilitate natural user interaction with the system, enabling people to engage with a context-aware environment that is sensitive, adaptive, and responsive to their needs, habits, gestures, and emotions, thus creating intelligent environments.
 Five levels that allow us to distinguish whether an environment is intelligent are: (1) Social Embedding Level. The device is integrated into the environment in such a way that the person is hardly aware of it and can communicate with it naturally. (2) Context Awareness Level. Here, the technology links the user's characteristics with the characteristics of the environment. (3) Personalized Level. At this stage, there is a personal profile that allows the device to adjust to the user's needs. (4) Adaptive Level. The technology reacts automatically to changing circumstances. (5) Anticipation Level. The technology reacts to environmental factors to prevent any kind of problem.
Five levels that allow us to distinguish whether an environment is intelligent are: (1) Social Embedding Level. The device is integrated into the environment in such a way that the person is hardly aware of it and can communicate with it naturally. (2) Context Awareness Level. Here, the technology links the user's characteristics with the characteristics of the environment. (3) Personalized Level. At this stage, there is a personal profile that allows the device to adjust to the user's needs. (4) Adaptive Level. The technology reacts automatically to changing circumstances. (5) Anticipation Level. The technology reacts to environmental factors to prevent any kind of problem.
Eight dimensions of obstruction experienced by users are: (1) Physical dimension. Physical presence of sensors and equipment. (2) Usability dimension. Usability issues gradually decrease as technology becomes smarter and requires less operation. (3) Privacy dimension. Privacy becomes more important as applications collect more data about the environment and users. (4) Functional dimension. (5) Human dimension. (6) Self-concept dimension. (7) Routine dimension. (8) Sustainability dimension.
Surveillance of Individuals:
The availability of data on every citizen can lead to a desire among public and private entities to access this data to ensure well-being and assistance, as is the case with law enforcement and combating terrorism. Other institutions responsible for health may justify their actions similarly. Increased surveillance can have consequences for citizens. For example, disclosing details about one's health, political and sexual orientation, personal preferences, habits, and lifestyle to an insurance company or HR (Human Resources) can lead to significantly higher insurance premiums, insurance denials, job losses, discrimination in general, blackmail, and problems in interpersonal relationships. The positive aspect, which some only highlight, is that the AmI (Analog-Information Technology) uses computers as proactive tools to assist people in their daily activities, attempting to make their lives more comfortable. One of its concerns is human-computer interaction, where a growing number of interaction methods are offered, ranging from those based on natural language to those based on images, gestures, and so on.
Final Considerations.
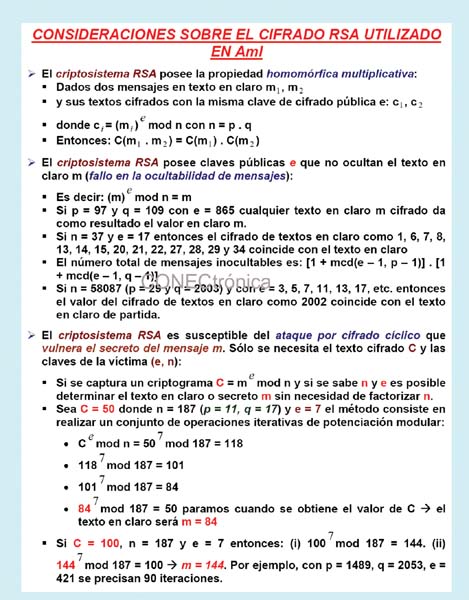
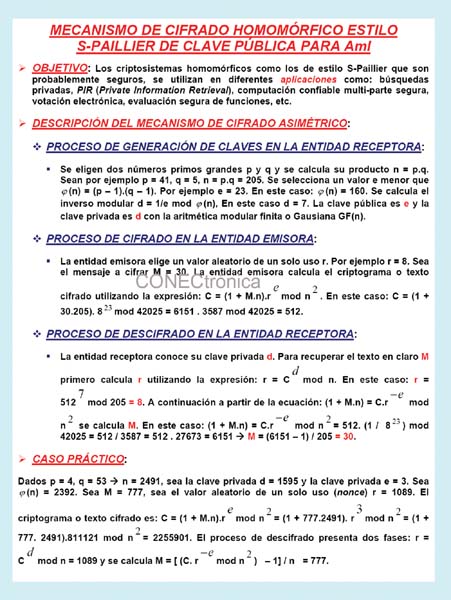
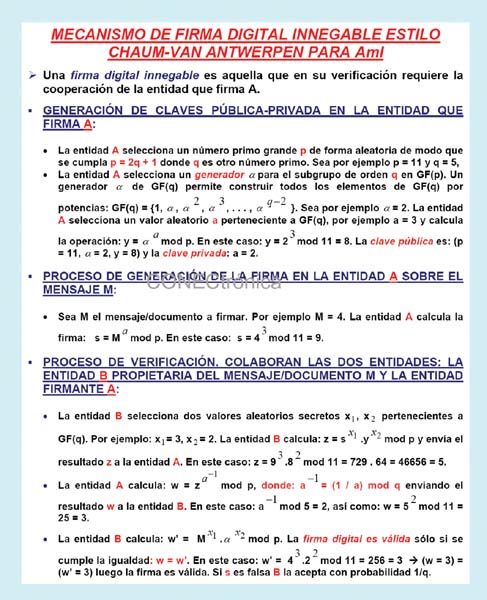
Cryptology, in its two facets of cryptography and steganography, represents the key to managing the escalating and unacceptable risks posed by AmI systems, as well as the ubiquitous computing and communications that support them. Our research group works on protecting AmI environments and deploying AmI networks based on communication through RF noise and interference.
This article is part of the activities developed within the LEFIS-Thematic Network.
Bibliography
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2012.
Areitio, J. “Technical Considerations for Bluetooth Protection in WPANs”. Conectrónica Magazine. No. 160. September 2012.
Areitio, J. “Identification and Analysis of Web Application Protection”. Conectrónica Magazine. No. 143. January 2011.
Weber, W., Rabaey, J. and Aarts, EHL “Ambient Intelligence”- Springer. 2010.
Wright, D., Gutwirth, S., Friedewald, M., Vildjiounaite, E. and Punie, Y. “Safeguards in a World of Ambient Intelligence”. Springer. 2010.
Petkovic, M. and Jonker, W. “Security, Privacy and Trust in Modern Data Management: Data-Centric Systems and Applications.” Springer. 2010.
Eldar, YC and Kutyniok, G. “Compressed Sensing: Theory and Applications.” Cambridge University Press. 2012.
Schneier, B. “Economics of Information Security and Privacy.” Springer. 2011.
Nicastro, FM “Security Patch Management”. CRC Press. 2011.
Norman, TL “Risk Analysis and Security Countermeasure Selection.” CRC Press. 2009.
Wright, D. and Hert, P. “Privacy Impact Assessment.” Springer. 2012.
Fuller, R. and Koutsoukos, XD “Mobile Entity Localization and Tracking in GPS-less Environments. Second International Workshop”. Proceedings. Orlando. USA. September. 2009.
Craig, T and Ludloff, ME “Privacy and Big Data.” O'Reilly Media. 2011.
Bettini, C., Jajodia, S., Samarati, P. and Wang, XS “Privacy in Location-Based Applications: Research Issues and Emergency Trends”. Springer. 2009.
Tinm, C. and Perez, R. “Seven Deadliest Social Networks Attacks.” Syngress. 2010.
Axelrod, WW, Bayuk, JL and Schutzer, D. “Enterprise Information Security and Privacy.” Artech House Publishers. 2009.
Kostopoulos, G. “Cyberspace and cybersecurity.” Auerbach Publications. 2012.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto



