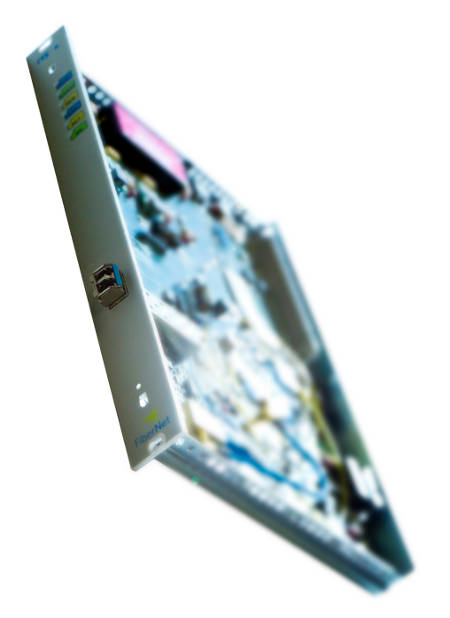
 Now, Fibernet customers can rely on an end-to-end encrypted SAN extension, offering maximum security and negligible processing time—a key factor in minimizing the impact on data backup time. The new FTX-C card is therefore designed for SAN environments, particularly for Disaster Recovery applications in Data Centers. Customers typically use dedicated connections between their sites for these types of applications, without sharing bandwidth with other customers. However, it is also essential to encrypt this data efficiently and without affecting the latency parameters inherent in the fiber optic distance between sites. This new product for SAN protocol encryption features:
Now, Fibernet customers can rely on an end-to-end encrypted SAN extension, offering maximum security and negligible processing time—a key factor in minimizing the impact on data backup time. The new FTX-C card is therefore designed for SAN environments, particularly for Disaster Recovery applications in Data Centers. Customers typically use dedicated connections between their sites for these types of applications, without sharing bandwidth with other customers. However, it is also essential to encrypt this data efficiently and without affecting the latency parameters inherent in the fiber optic distance between sites. This new product for SAN protocol encryption features:
- Encrypted Fiber Channel transport over Ethernet. The most widely recognized algorithm for this type of application is currently AES (Advanced Encryption Standard): FIPS-197, standardized in 2001 by the US agency NIST after being selected as the best among those submitted in a public tender. The standard considers three possible key lengths: 128, 192, or 256 bits, with Fibernet choosing the latter. Encryption uses a symmetric key, which is typically employed when higher speeds are required. The key exchange mechanism is Diffie-Hellman, also standardized by NIST. No key is transmitted over the exchange channel; only information is passed so that both ends can calculate the key.
Design: State-of-the-art components (FPGAs) with bitstream encryption and authentication have been used. Security is also provided by the card's control software. Furthermore, the microcontroller is integrated within the FPGA; there is no external memory and no visible connections on the card.
Meeting the requirements for this type of product, the new end-to-end encryption solution provides maximum transparency and minimal latency.
Load balancers with natively integrated Web Application Firewall
KEMP Technologies has announced that its LoadMaster load balancers will natively integrate Web Application Firewall (WAF) services. This will enable secure web application development, preventing Layer 7 attacks, while maintaining core load balancing services.



