Web Application Security:
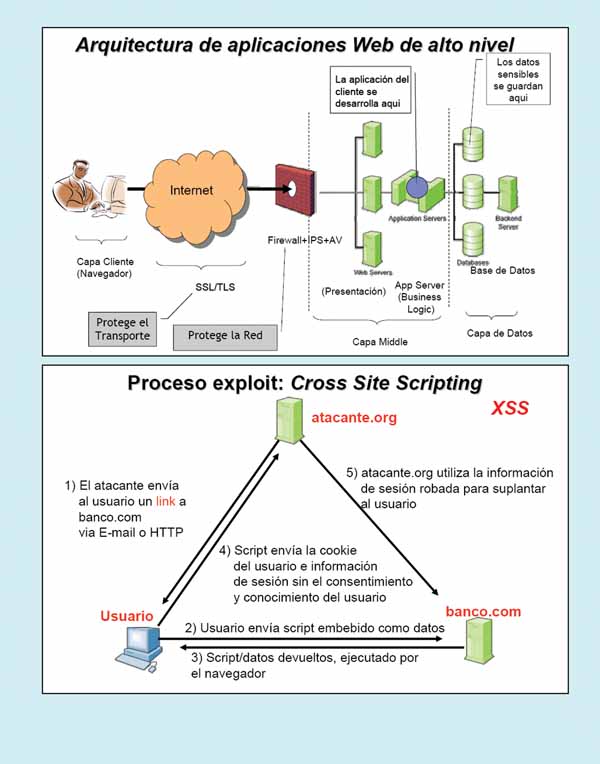
There is a growing trend towards software becoming a web-based service. The number of real-world examples in our society is increasing daily: online banking, e-commerce, e-government, e-democracy, e-healthcare, customer relationship management, social networks, content companies, etc., and even cloud computing (XaaS, where X can be (I) Infrastructure, (P) Platform, (S) Software, etc.). Applications hosted on web servers are becoming more numerous and are written in a mix of languages, including PHP, Java, Perl, Python, C, and ASP. Web security is rarely the primary concern of software architects and designers. The following deficiencies can be identified: (i) Poorly written scripts (a script is a set of instructions that automate tasks, creating utilities) with inadequate input validation. (ii) Sensitive data stored in plain text in files readable by anyone. (iii) Sending passwords unencrypted, and using HTTP instead of HTTPS (SSL/TLS), etc. Visa and Mastercard have made a significant effort to improve data management security with the PCI-DSS standard; however, it's important to note that meticulous IT (Information Technology) compliance is not always synonymous with good security management within an organization. Web applications run either on a web server (real, virtual, standalone, or a server farm) or on an application server. They collect input from web users via the web server and interact with back-end and third-party databases. Web applications prepare and deliver results to users via the web server, and two key aspects can be identified: (i) They dynamically generate HTML pages. (ii) They contain content from many different sources, often from regular users: blogs, social networks, websites for sharing photos, music, etc. Web security can be divided into two main areas: (1) Web Browsers (such as Microsoft Internet Explorer 8, Mozilla Firefox 3.5.13, Safari 5 (for PC/MacOS), Netscape 9.0, Opera 9.10, Google Chrome 4.0, micro-browsers for PDAs, etc.). These can be attacked by any website you visit. Attacks can lead to malware installation (in the form of keyloggers, which capture keystrokes; this can be mitigated with on-screen virtual keyboards), botnets, spyware, etc. For example, users might be tricked into downloading and running codec software to view an interesting video), document and identity theft, loss of private data, and so on. (2) Web Applications. These run on the website (such as online banks, blogs, online stores, Google Apps, etc.) and are written in PHP, ASP, JSP, Ruby, etc. They have many potential flaws (or bugs) such as XSS, SQL injection (SQL-I), etc. Furthermore, the attacks allow for credit card theft, defacing websites (as in the case of the website www.eu-2010.es where the image of ZP was replaced with that of the comedian Mr. Bean. This could have been avoided if a proper code audit had been carried out to prevent XSS), etc.
Web Threat/Attacker Models.
Web attackers can be very diverse: (i) They control malicious websites and may even obtain SSL/TLS certificates for their sites. The reasons why a user might visit these malicious websites are varied: receiving a phishing email, encountering highly attractive content (from a recreational or professional perspective), due to search results from a web search engine, placement by an advertising network, bad luck, etc. (ii) The attacker has no other access to the user's machine. (iii) Gadget attacker. For example, a malicious gadget included in a legitimate mashup. A gadget is a program object/mini-application that provides dynamic services; gadgets in Windows 7/Vista are located in the sidebar. (iv) Network attacker. They can be passive (performing clandestine wireless or wired eavesdropping using sniffers), active using a malicious router, performing DNS poisoning (or pharming), using ARP poisoning to perform man-in-the-middle attacks, etc. (v) Malware attacker. The attacker gains control of the user's machine in a variety of ways: (a) Exploiting application or operating system bugs (e.g., buffer overflow) due to a lack of code auditing and operating system patches. (b) Convincing the user to install malicious content in various ways, for example: tricking them into running a free antivirus program, or into installing a special codec to play a video in a new format, etc. (vi) XSS/CSS (Cross-Site Scripting) risks. XSS is a type of reflexive attack; the user is tricked into visiting a poorly written website, a bug in the website's code causes it to display, and the user's browser executes an arbitrary attack script. It can: (a) Change the content of the affected website by manipulating DOM (Document Object Model) components (the HTML page is structured data, and the DOM provides the representation of this hierarchy), displaying false information, requesting sensitive data, and controlling form fields on this page and linked pages. For example, a MySpace.com phishing attack injects the password field, allowing the password to be sent to a malicious friend. (b) It can cause the user's browser to attack other websites.
 The Essence of Information Security. Mistakes. Generations of Threats.
The Essence of Information Security. Mistakes. Generations of Threats.
The essence of information security can be defined as a continuous process; it is a business matter (not merely a compliance issue and the responsibility of the IT/ICT department); it improves the organization's image and reputation; it increases trust and credibility; it boosts organizational productivity; it is a justifiable and useful invisible necessity; it is an investment; it is a competitive business advantage; it is a priority; it is the focus of generating business resilience; it prevents corporate risks and financial losses; it is a true support for business objectives; it is the key pillar for the management of any company; security supports and protects business objectives; it is a business problem for which the organization's management is responsible. Over the years, numerous significant misconceptions about information security have been identified: (i) If our company has antivirus software and/or a firewall, we are safe. (ii) Most serious threats come from outside. (iii) Our company doesn't need to worry about security because we back up data daily. (iv) The responsibility for security lies with the IT security staff. If anyone in the company has any problems (they can report them by submitting a request via the web through GP or by phone for faster response), they will resolve them. (v) Some ignorant CEOs claim that their company has budget constraints, so they absurdly question whether the security budget is necessary if the work is being done. Furthermore, it is a serious mistake to assert: (a) Company security is just a product to buy, or just technology to use, or just a policy to agree upon, or just a specific time investment. Keep in mind that the weakest link is the human factor. Remember that security covers all aspects of the company, permeates everything, investigates which assets and risks are at risk, and determines how to address those risks. The conclusion is that security is an ongoing process that integrates technology, policies, best practices, training, and awareness, establishing a modern security and privacy culture. A threat is the probability of an attack, for example, an IP packet causing a buffer overflow. A vulnerability is the probability of an exploitable vulnerability, for example, a buffer overflow. The consequences are the total cost of a successful attack. Risk is the product of threats, vulnerabilities, and consequences, for example, crashing a system.
Over the years, the following generations of threats can be identified: (1) First generation: Subversion of infrastructure elements. This affects IT elements, email, servers, databases, data, programs, etc. (2) Second generation: Subversion of business processes. This affects processes, people, etc. (3) Third generation: Subversion of critical infrastructure. This affects transportation and traffic infrastructure, water infrastructure, communications infrastructure, public health infrastructure, banking and finance infrastructure, energy and utilities infrastructure, vital data centers, nuclear power plants, electricity generation and distribution infrastructure, etc.
Main Website Vulnerabilities
The main website vulnerabilities, which can also be considered web attacks, are: (i) SQL Injection. The browser sends malicious input to the server. Improper input validation leads to a malicious SQL query. The attacker's malicious code is executed on the victim's server. It uses SQL to change the meaning of the database command. Several well-known defenses exist to efficiently address this issue, such as web application firewalls (Fortinet's FortiWeb-400B, Citrix's NetScaler, F5's TrafficShield, etc.). General code injection attacks aim to execute arbitrary code on the server; in the context of SQL injection, PHP database queries are dangerous because a malicious string can change the query's meaning. Possible SQL injection preventions include: never constructing SQL commands yourself, using parameterized SQL, or employing an ORM framework. (ii) CSRF (Cross-Site Request Forgery) or XSRF. A malicious website sends a browser request to a legitimate website using the credentials of an unsuspecting victim. The attacker's website forges the victim's browser request to the victim's server. The user's session on the victim's server is compromised. This is a forged request that affects the ongoing session. It can be partially prevented.
Possible defenses include: (1) Secret token validation. This requires using a difficult-to-guess secret token. (2) Referrer validation. For your security, never type your password, for example, for Facebook, on sites not hosted on Facebook.com. (3) Custom HTTP headers. This does not work across domains. (4) Cross-Site Scripting (XSS). The malicious website sends an unsuspecting victim a script that steals information from a legitimate website. The attacker's malicious code is executed in the victim's browser. The malicious script is injected into the trusted context. The problem originates from the echo of the untrusted input. This is difficult to prevent: it requires careful monitoring, testing, tools, etc. An XSS vulnerability occurs when an attacker can inject scripting code into pages generated by a web application.
 Some methods for injecting malicious code include: (a) Reflected XSS (Type 1). The attacker's script is reflected back to the user as part of a page on the victim's website. (b) Stored XSS (Type 2). The attacker stores the malicious code in a resource managed by the web application, such as a database. (c) DOM (Document Object Model)-based attacks that do not use the server.
Some methods for injecting malicious code include: (a) Reflected XSS (Type 1). The attacker's script is reflected back to the user as part of a page on the victim's website. (b) Stored XSS (Type 2). The attacker stores the malicious code in a resource managed by the web application, such as a database. (c) DOM (Document Object Model)-based attacks that do not use the server.
Some client-side defenses against XSS attacks include: (i) Proxy-based protection. This analyzes the HTTP traffic exchanged between the user's web browser and the destination web server, scanning for special HTML characters and encoding them before the page is executed in the user's web browser. (ii) Protection using an application-level firewall. This analyzes the HTML pages being browsed for hyperlinks that could lead to the leakage of sensitive information and blocks malicious requests using a set of connection rules. (iii) Protection using an auditing system. It monitors the execution of JavaScript code and compares operations against high-level policies to detect potential malicious behavior.
According to OWASP (Open Web Application Security Project), some strategies to protect against XSS attacks are:
1) Ensure your applications validate all headers, cookies, query strings, form fields, and hidden fields (all parameters) against a rigorous specification of what should be allowed. Never trust client-side data; the best strategy is to allow only what is expected. Also, remove/encode special characters, such as long characters and UFT-8 encodings. Automated black-box testing tools like Hailstorm, WebInspect, Retina, eEye, Cenzic, and Spidynamic exist, as well as web application hardening tools like WebSSARI, which is based on information flow, and black-box security testing services like whitehatsec.com.
2) Do not attempt to identify, remove, filter, or sanitize active content. Because there are too many types of active content and countless ways to encode it to bypass content filters,
3) Use a positive security policy that specifies what is allowed. “Negative” attack signature-based policies are difficult to maintain and are likely incomplete.
Sans Top 10 ICT Security Trends. Sans Top 20 Critical Controls.
The Sans Top 10 ranking of ICT (Information and Communication Technologies) security trends is as follows: (1) Mobile Devices: Laptops. For example, with hard drive encryption. (2) Mobile Devices: PDAs/Smartphones. (3) Government Actions: Regulatory Compliance. (4) Targeted Attacks: Government and Businesses. (5) Targeted Attacks: Cell Phones: GSM/GPRS/
UMTS/HSDPA/Bluetooth. (6) Targeted Attacks: VoIP (Voice over IP). (7) Attack Techniques: Spyware. (8) Attack Techniques: Zero-day Vulnerabilities. (9) Attack Techniques: Rootkits. (10) Defense Strategies: Sophistication of NAC (Network Access Controls). The Sans Top 20 ranking of critical controls is: (1) Inventory of authorized and unauthorized devices. Using an automated, real-time soft/hard asset inventory discovery tool. (2) Inventory of authorized and unauthorized software. (3) Securely configuring hardware and software on laptops, workstations, and servers. (4) Securely configuring network devices such as routers, switches, firewalls, IPS/IDS, and UTMs. (5) Border defense. (6) Maintenance, monitoring, and analysis of security audit logs. (7) Application software security. (8) Controlled use of administrative privileges. Controlled access based only on what needs to be known. (10) Continuous vulnerability assessment and remediation. (11) Account monitoring and control. (12) Malware defenses. With appliance-type antivirus hardware deployed on the network and software on workstations. (13) Limiting and controlling network ports, protocols, and services. Using hardware NAC. (14) Wireless device control. WiFi, Bluetooth, GSM/GPRS/UMTS/HSPD, etc. (15) Data Loss Prevention (DLP). (16) Secure network engineering. (17) Penetration testing and Read Team exercises and ethical hacking. (18) Incident response capabilities. (19) Data recovery capabilities. (20) Security skills assessment and appropriate training to fill gaps.
Correlation between Security Levels and Threats.
Currently, there are various threat areas such as malware distribution, phishing/pharming, spam, rootkits, DoS/DDoS attacks, and botnets. If we consider a user outside an organization who wants to interact with a database within the organization, it is possible to identify the following levels of protection from the outside in, along with their associated threats: (i) HTTP Client/User Level. Threats such as CSS and spoofing/trickery can be detected. (ii) HTTP(S) Transport Level. Passive monitoring, MITM (Man-In-The-Middle) attacks, and session hijacking. (iii) Firewall Level. Allowing HTTP(S). (iv) Web Server. Buffer overflow, format strings, directory traversal, default accounts, and sample applications. (v) Web Applications and CGIs. Filter-bypass manipulation, metacharacters, null characters, and buffer overflow. (vi) Firewalls. Be aware of threats within the internal network. (vii) Databases. Direct SQL commands, restricted database query, database exploits.
Final Considerations
Our research group has been working for over fifteen years in the field of web security for servers, applications, services, infrastructure, etc. We have focused on the evaluation and development of improvement projects in the web context, security and privacy by design in the web world, and the synthesis of appropriate protection mechanisms, both software and hardware, as well as embedded logic in micro- and nanosystems.
This article is part of the activities carried out within the LEFIS-APTICE project (funded by Socrates, European Commission).
Bibliography
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2010.
- Areitio, J. “Security Test to Evaluate and Improve the Level of Security Risks”. Conectrónica Magazine. No. 134. February 2010.
- Zittrain, J. “The Future of the Internet and How to Stop It”. Yale University Press. 2009.
- Web Application Tools: http://www.owasp.org: (i) Web Scarab: Powerful HTTP interceptor (modifies data in transit). (ii) Web Goat: Deliberately insecure applications for exploit training.
- Nikto Web Application Security Scanner: http://www.cirt.net/nikto2
- Web Dev Toolbar: https://addons.mozilla.org/firefox/addon/60
- Firefox XSS and SQL-I Add-ons: http://securitycompass.com
- N-Stalker: http://www.nstalker.com/products/free
- Wapiti Free Web Application Security Scanner: http://wapiti.sourceforge.net
- Spider Sensitive Information Scanner: http://www.cit.cornell.edu/security/tools
- Absinthe SQL-I (SQL Injection) Tool: http://www.0x90.org/releases/absinthe
- Other free tools: https://infosec.uga.edu/sate/tools.php
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto.