 Cloud computing is a general term used to describe a new class of network-based computing that uses the internet, provided by a service provider. It supports on-demand network access and integrates a shared pool of configurable computing resources. It integrates a collective/group of networked hardware/software and internet infrastructure, known as a platform. It uses the internet for communication and information transport, providing hardware, software, and network services to clients. These platforms hide the complexity and details of the underlying infrastructure from users and applications by providing a simple graphical interface or API (Application Programming Interface). The platform provides on-demand services that are always available, regardless of location, date, or time. Users pay for services as needed, and the services are elastic, allowing for both upscaling and down in capacity and functionality. Hardware and software services are available to businesses, large corporations, business markets, and the general public.
Cloud computing is a general term used to describe a new class of network-based computing that uses the internet, provided by a service provider. It supports on-demand network access and integrates a shared pool of configurable computing resources. It integrates a collective/group of networked hardware/software and internet infrastructure, known as a platform. It uses the internet for communication and information transport, providing hardware, software, and network services to clients. These platforms hide the complexity and details of the underlying infrastructure from users and applications by providing a simple graphical interface or API (Application Programming Interface). The platform provides on-demand services that are always available, regardless of location, date, or time. Users pay for services as needed, and the services are elastic, allowing for both upscaling and down in capacity and functionality. Hardware and software services are available to businesses, large corporations, business markets, and the general public.
Key characteristics. Values and risks.
The key characteristics that define cloud data, application services, and infrastructure are:
(i) Services or data are hosted on remote infrastructures.
(ii) Ubiquitous. Services or data are available from anywhere with internet access (and what about jamming attacks, EM interference, and RF jamming?).
(iii) It presents a utility computing model similar to traditional services like gas, water, and electricity, where you pay for what you use. Cloud computing is currently experiencing some growth; however, this technology still presents several unresolved cybersecurity and cyberprivacy issues and is, in some ways, still immature.
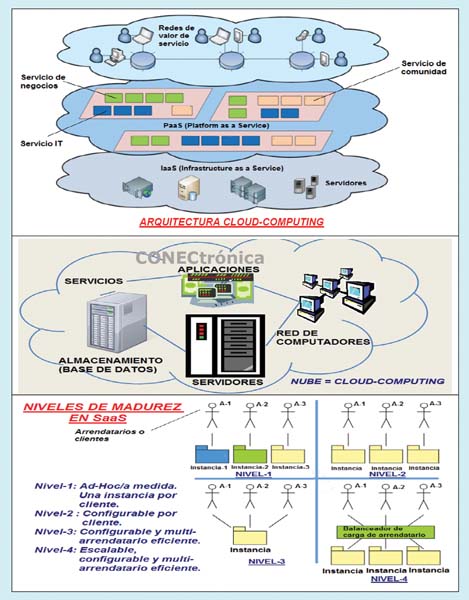
The main value of cloud computing lies in its ability to make resources (IaaS: computing infrastructure as a platform virtualization environment, PaaS: computing platform for developing applications, SaaS: software applications themselves, etc.) transparently available regardless of the consumer's location and on all types of hardware gadgets such as tablets, smartphones, gaming machines, PCs, augmented reality glasses, medical prostheses, etc. with an Internet connection.
VMware, a global leader in virtualization and cloud infrastructure, defines cloud computing as a new approach that reduces IT complexity by efficiently combining self-managed, on-demand virtual infrastructure consumed as a service. Some of the many key cloud developments include Google App Engine (PaaS), IBM's Blue Cloud (formerly Salesforce), Microsoft's Azure, and Amazon's AWS.
 Dell is working on a project called Ophelia, a virtual computer in the cloud that can be accessed from anywhere with an internet connection. The goal is to allow users to access their own computer and applications from any connected device. The service provider monitors performance to maintain consistency, allowing multiple users to utilize the provided resources and services. According to the Institute of Engineering and Technology (IHS), the trend in cloud storage will grow from approximately 625 million subscribers in 2013 to around 820 million in 2015, then to about 1 billion in 2016, and finally to around 1.3 billion in 2017. The Government Technology Research Alliance (GTRA) indicates that cybersecurity remains the biggest challenge in implementing cloud computing.
Dell is working on a project called Ophelia, a virtual computer in the cloud that can be accessed from anywhere with an internet connection. The goal is to allow users to access their own computer and applications from any connected device. The service provider monitors performance to maintain consistency, allowing multiple users to utilize the provided resources and services. According to the Institute of Engineering and Technology (IHS), the trend in cloud storage will grow from approximately 625 million subscribers in 2013 to around 820 million in 2015, then to about 1 billion in 2016, and finally to around 1.3 billion in 2017. The Government Technology Research Alliance (GTRA) indicates that cybersecurity remains the biggest challenge in implementing cloud computing.
Drawbacks and Problems of Cloud Computing:
Cloud computing deployments are becoming increasingly popular and include a growing number of user applications, from word processors like Word, antivirus software, photo and calendar applications, maps, video conferencing, CRM software, and data storage to social networks. Some services that utilize the cloud include Dropbox, WorldCat, Mendeley, ExLibris, LibraryThing, ResearchGate, etc., as well as Google Apps, YouTube, RemoteXS, Zimbara, Facebook, Cybrarian, Word 365, Liblime Koha, etc. Cloud services are attractive because they offer availability, reliability, global accessibility, etc., which is not so simple with desktop computer applications.
Unfortunately, these benefits come at the cost of having to trust the service provider with the confidentiality, integrity, and availability of customer data. Our private data stored with cloud providers can be copied, stolen, leaked, or exposed without any guarantees to malicious entities from outside (competitors), inside (dishonest staff), or governments (local or foreign). A compromised or malicious cloud provider can manipulate user data or even mistakenly show different users conflicting views of the system's status. Some countermeasures are being deployed based on the security of cryptographic key management, but even then, it's possible to bypass key secrecy and encryption using advanced techniques such as reverse engineering, cryptanalysis, side-channel attacks, and so on.
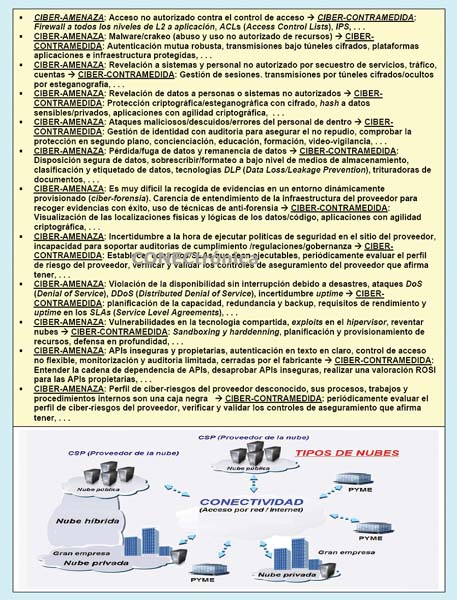
Areas of cyberattacks. Cyber-safeguards in cloud computing.
A thorough analysis of cybersecurity issues surrounding the cloud allows us to identify different areas of cyberattacks:
(1) Cyberattacks on availability. There are things that cannot be run in the cloud due to the risk of crashing it, related to the number of people involved or the processing power required, such as tools like SAPvX. How does the cloud provider ensure the integrity of the computations? For example, with their word, or by having the same task/application run by many processors until a consensus is reached on the correct result? There are many points of attack against availability: links, servers, operating systems, hypervisors, applications, drivers, data, etc.
(2) Traditional Cyberattacks. This section includes attacks on: (i) Virtual Machine Level. Vulnerabilities in the virtual machine/hypervisor technology used by cloud providers in their multi-tenant architectures. Mitigation components include firewalls, monitoring, and IDS/IPS/IAM. (ii) Cloud Provider Vulnerabilities. This includes SQL injection, XSS, etc. Mitigation components include vulnerability management and auditing tools. (iii) Professional cloud forensics, even against anti-forensic techniques. Currently, this is an impossible task. (iv) Phishing Attack Vectors. The cloud can serve as an attack vector for social engineering. (v) Authentication and Authorization Tasks. These cannot be extended to the cloud. (vi) Super-Extended Network Attack Surface. Cloud users must protect the infrastructure used to connect to and interact with the cloud, a very complex task.
(3) Cyberattacks on third-party data control. This section includes attacks on: (i) Cloud provider espionage. (ii) Enforcement of contractual obligations and SLAs (Service Level Agreements) with the cloud provider. (iii) Audits and compliance standards. Certain regulations require maintaining data and operations in specific geographic locations. Some providers have begun to include geo-targeted services.
(4) Cyberattacks on key management. Cryptographic encryption key management was designed for physical servers and does not operate properly in virtualization. It is not secure to store passwords or certificates in individual VMs.
 (5) Other cyberattacks. Attacks on process/VM isolation, data segregation, multi-tenancy, data localization, authentication, data sharing, data access, encryption/digital signature/nonce generation/pseudo-random PRNG, delegation of access authority, IAM/AAA, security architectures/models, etc. If the VM platform provides high availability, the applications do not, and vice versa. Attacks on data protection in three directions: personal data security, personal data location, and access to such personal data.
(5) Other cyberattacks. Attacks on process/VM isolation, data segregation, multi-tenancy, data localization, authentication, data sharing, data access, encryption/digital signature/nonce generation/pseudo-random PRNG, delegation of access authority, IAM/AAA, security architectures/models, etc. If the VM platform provides high availability, the applications do not, and vice versa. Attacks on data protection in three directions: personal data security, personal data location, and access to such personal data.
Virtualization and Cloud Computing Technologies. Xen.
Virtualization technology is a key technology in cloud computing. Some well-known virtualization products are: Xen (originally developed by Cambridge, now Citrix for Linux), VMware (for Linux and Windows), and Parallel Desktop (for Mac). Virtualization technology allows multiple operating systems to share a computing machine. An instance of a guest operating system running is called a VM (Virtual Machine). Virtualization technology can host hundreds of virtual machines. The main benefits of virtualization are resource consolidation, VM migration, workload balancing, and environment isolation.
The components of Xen are:
(i) The hypervisor. It sits between the hardware and any operating system. It is responsible for scheduling the CPU and memory partitioning of the VMs. It allows control over the execution of other domains and uses the "less is more" philosophy (a new version is less than the old version and does not re-implement functions provided by the operating system, such as networking and I/O).
(ii) Domain 0. It is a modified Linux kernel with domain management and control. It contains device drivers to access the hardware (e.g., ND-Network Driver and BBD-Block Backend Driver) and interacts with other VMs.
(iii) Domain U. It does not have direct access to the hardware; it shares resources with other domains (the resources are virtualized). In Xen 3.X, modified operating systems (Linux, Windows, Solar, UNIX) are required. From Xen 4 onward, it supports original operating systems. Writing to Xen is similar to writing to the Linux operating system; for example, system calls are hypercalls, signals are events, and filesystems are XenStores. Some typical hypervisors used in virtualization environments are: KVM, Xen/XCP, Hyper-V, VMware, Grizzly, etc.
Final Considerations:
The cloud computing paradigm is an active area of research. For example, cloud storage methods that are somewhat more private than Dropbox/Google Drive/iCloud, such as OwnCloud and Tahoe-lafs, have been proposed. Similarly, open-source solutions like Seafile (which allows building a private cloud for file sharing and network collaboration, functioning similarly to Dropbox with clients that synchronize transparently) and Duplicati (an encrypted file backup tool that connects to cloud storage systems such as Amazon S3, Google Drive, Windows OneDrive, and Rackspace, as well as personal servers with SSH/FTP access), have also been developed. Our research group has been evaluating, analyzing, synthesizing, and implementing protection systems for over fifteen years to improve cybersecurity and privacy, which are especially important in public and hybrid cloud environments.
This article is part of the activities developed within the LEFIS Network.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering, University of Deusto.
Director of the Networks and Systems Research Group.
Literature
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2013.
Areitio, J. “Identification, Analysis and Correlation between Physical Protection and Cybersecurity”. Conectrónica Magazine. No. 161. October 2012.
Areitio, J. “Risk Analysis in Cybersecurity and Cyberprivacy of Information Surrounding AmI Systems”. Conectrónica Magazine. No. 163. January 2013.
Areitio, J. “Evolution of Threats and Trends in Network Security in the Web Context”. Conectrónica Magazine. No. 142. November 2010.
Winkler, V. “Securing the Cloud: Cloud Computer Security Techniques and Tactics”. Syngress Publications. 2011.
Mather, T., Kumaraswamy, S. and Latif, S. “Cloud Security and Privacy: An Enterprise Perspective on Risk and Compliance.” O'Reilly Media. 2009.
Halpert, B. “Auditing Cloud Computing: A Security and Privacy Guide.” Wiley. 2011.
URL:
http://www.cloudsecurityalliance.org Krutz, RL and Vines, RD, “Cloud Security: A Comprehensive Guide to Secure Cloud Computing.” Wiley. 2010.
Murugesan, S. “Cloud Computing”. Chapman and Hall/CRC. 2012.
Smoot, SR and Tan, NK “Private Cloud Computing.” Morgan Kaufmann. 2012.
Bauer, E. and Adams, R. “Reliability and Availability of Cloud Computing.” Wiley-IEEE Press. 2012.
Buchanan, W.J. “Advanced Cloud Computing and Virtualization.” Auerbach Publishers. 2012.
Lim, I, Hourani, P. and Coolidge, E.C. “Securing Cloud and Mobility: A Practitioner's Guide.” Auerbach Publications. 2012.
McNab, C. “Secure Cloud Deployment.” McGraw-Hill Osborne Media. 2012.
Siepmann, F. “Managing Risk and Security in Outsourcing IT Services: Onshore and the Cloud.” Auerbach Publications. 2013.
Rountree, D. and Castrilllo, I. “The Basics of Cloud Computing: Understanding the Fundamentals of Cloud Computing in Theory and Practice.” Syngress. 2013.
Nepal, S. and Pathan, M. “Security, Privacy and Trust in Cloud Systems.” Springer. 2013.



