(2) Technologies. Barriers to adequate cybersecurity/privacy hygiene for IT/OT/IoT infrastructures are evident, such as a lack of asset identification and inventory, and the blurred boundaries between OT/IT/IoT/cloud/edge networks. It is essential to begin with basic hygiene, considering, for example, Critical Controls as a foundation that provides a solid basis for improving cybersecurity/privacy and supports an important first step: "improving visibility of assets and infrastructure." Factors affecting current infrastructures should be assessed, including the use of mobile/wireless devices, changes in operational procedures in light of the move to cloud services, and the completeness of information, documentation, and intelligence. An inventory of OT/IT/IoT assets should be established before expanding the use or expansion of industrial automation and control technologies to support operational processes or production, establishing a process to maintain a fault-tolerant/cyber-attack-resistant IT/OT/IoT asset inventory over time and also an operational baseline of well-known states for continued comparison.
(3) Processes, Management, and Governance. Processes must lead without delay to well-established technologies as a factor in strategy development, since automating a flawed process can increase the risk to the organization's cybersecurity and privacy. Investment should be made in a formal management and assessment of current processes to identify weaknesses (vulnerabilities) before creating a desired environment, including the technologies that support them. This management and assessment should utilize all types of internal and external resources, including formal audits. A highly mature, proactive, redundant, and self-evaluative management and governance environment is essential to minimize failures and cyberattacks, while also being effective and extremely fast.
Cybersecurity/privacy integrates a set of technologies, processes, techniques, management/governance mechanisms, practices, etc., designed to proactively protect networks, computers, programs, data, and people from cyberattacks, damage, or unauthorized access. The repertoire of cybersecurity/privacy objectives grows daily, and includes the following:
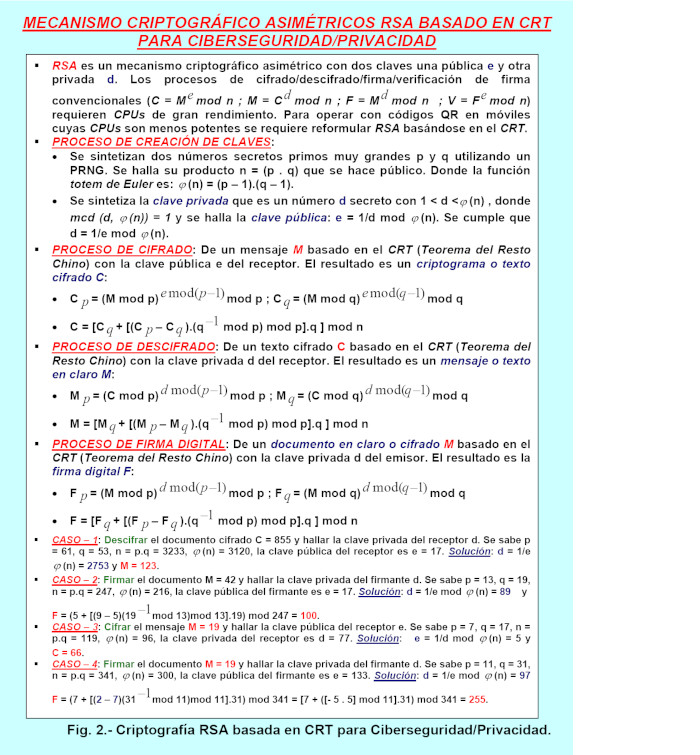
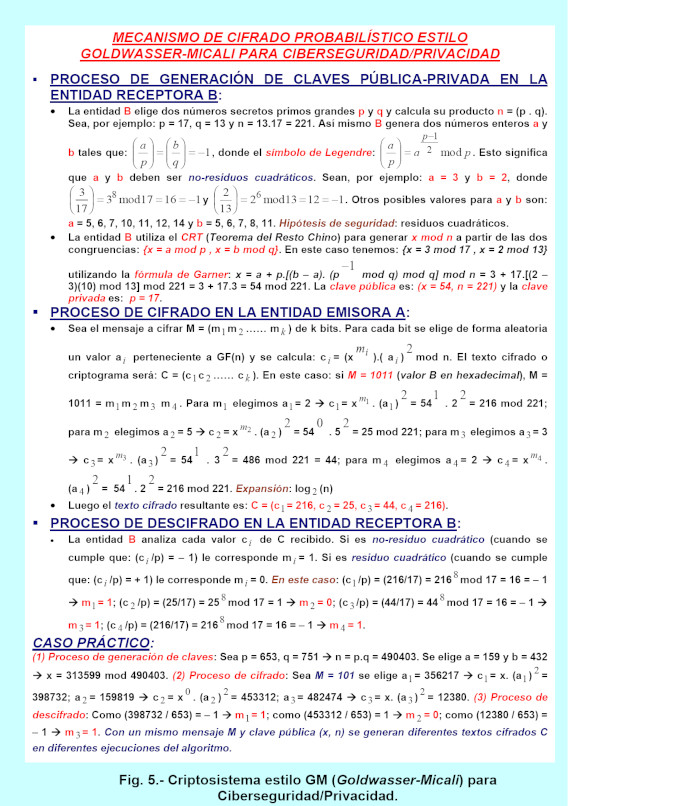
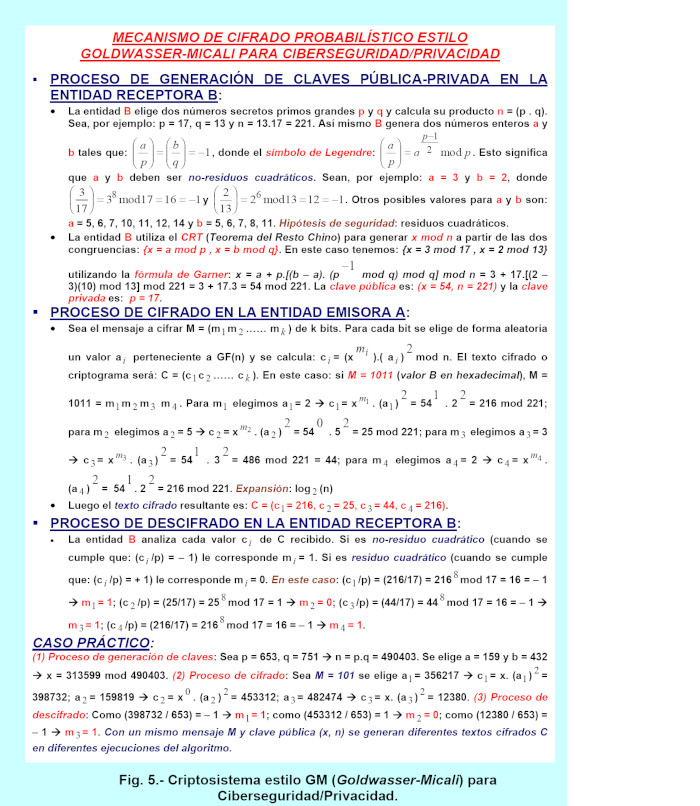
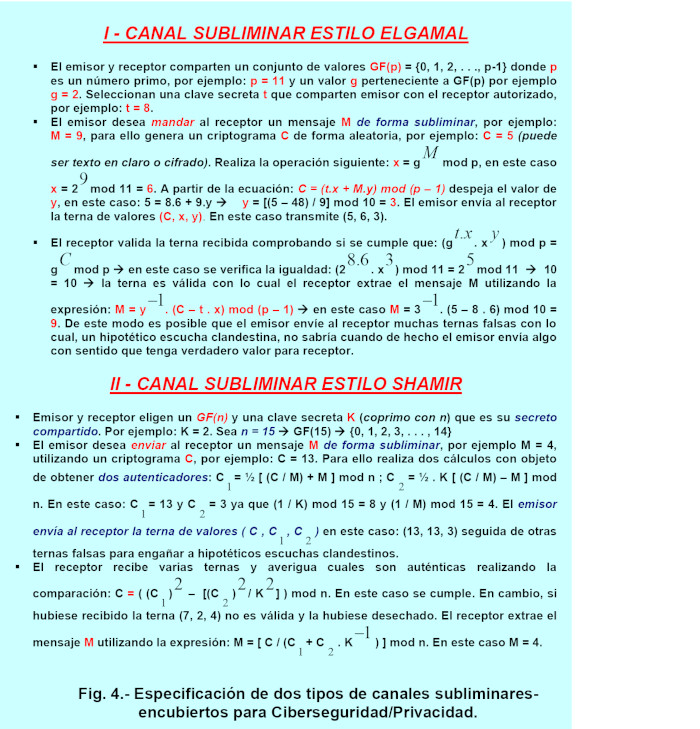
1) Confidentiality of data/information/intelligence. Cyber attackers use data mining, computer matching, computer profiling, sniffers, keyloggers, Trojans, cookies, botnets, etc., to compromise privacy. Protection includes encryption, steganography, subliminal channels, anonymity, ZK, Shamir fragmentation, KeyEscrow, OT, deception, etc.
2) System availability. Protection includes backups, redundancies, UPS/SAIs, etc.
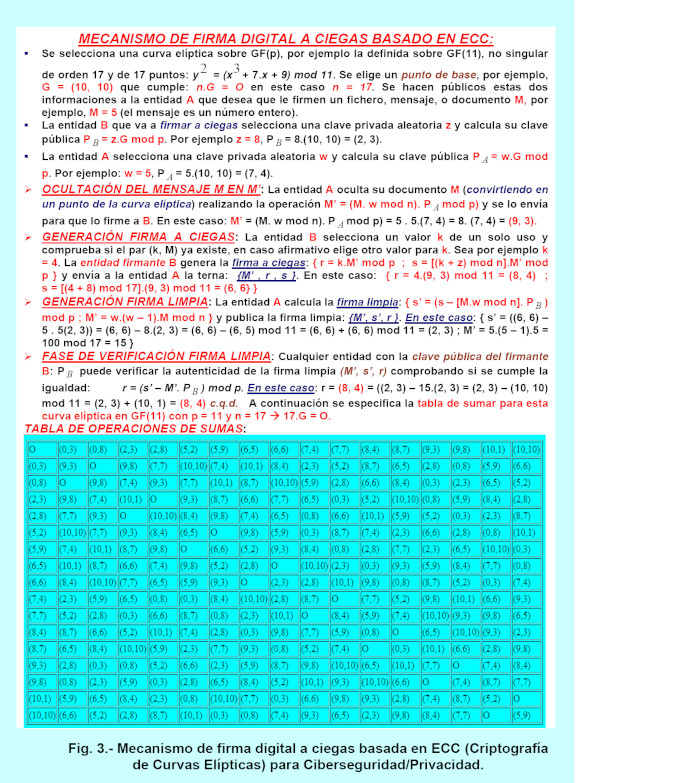
3) Data integrity. Protection includes conventional digital signatures, blind signatures, MAC addresses, hashes, backups, etc.
4) Hardware integrity. Protected with PUF, DAIM, and other technologies.
5) Authorization. Grants privileges and permissions enabling an entity to perform certain operations (read, write, execute, delete, create, etc.) on a specific object/resource (file, directories, printer, etc.).
6) Data authenticity. Protected with digital signatures, MAC addresses, hashes, backups, and other methods.
7) Action traceability. Protected with logs, audit trails, roaming malware, redundant backups, and other methods.
8) Data freshness. Protected with signed NTP timestamps and robust PRNG-based sequence numbers such as LCG, LFSR/NLFSR, subliminal channels, watermarks/steganography, anonymization, ZK, OT, ZT, and other methods.
9) Non-repudiation of actions. Protected with digital signatures plus TTPs and electronic notaries.
10) Identity privacy. Protected with anonymity (TOR, k-anonymity, Onion routing, subliminal channels, etc.).
11) Entity authentication. Protected with robust multi-factor authentication (simple or mutual) between user and server using passwords/PINs with extremely high entropy, biometrics (physiological and behavioral), proximity smartcards, ZK technology, hardware tokens, software tokens (authenticator-token software such as RSA Secur-ID for Windows MS), indoor and outdoor geolocation, NTP date/time stamp, etc.
 CONTROLS, CYBER THREATS AND STRUCTURES OF CYBERATTACKS.
CONTROLS, CYBER THREATS AND STRUCTURES OF CYBERATTACKS.
A wide variety of critical cybersecurity/privacy controls can be identified, such as: Inventory of authorized/unauthorized, known/unknown devices; Inventory of authorized and unauthorized software; Secure configurations for hardware/software/firmware; Ongoing vulnerability management (prevention/detection, assessment, and proactive remediation); Controlled use of administrative privileges; Maintenance, monitoring, and analysis of audit logs; Protection of web browsers and email; Proactive cyber defenses against malware/viruses; Limitation and control of network ports; Proactive/preventive data recovery capabilities; Secure configurations for network devices; Proactive cyber defenses of visible and invisible borders/perimeters; Protection of data/information/intelligence; Need-to-know (KNOW) controlled access; Wireless access control (WiFi 6-7, Bluetooth, Threads, LoRaWAN, 2G/3G/4G/5G/6G, etc.). Account monitoring and control; Management/assessment of cybersecurity skills and appropriate certified training; Software/firmware security (OS, applications/APPs/APIs/etc.); Management and proactive response to cyber incidents; Penetration testing (PenTest), comprehensive audits (of all types, including exploring certifications by accredited entities on national and international standards such as ISO, NIST, ENS, etc.), ongoing "Red Team" exercises, etc. According to ISO-7498-2, there are four generic types of basic cyber threats:
1) Interruption. A strategic system resource becomes inaccessible. This falls under the CIA domain of availability. One tool for creating this is an RF jammer or a DoS/DDoS attack. Countermeasures include: to enable fault tolerance, high availability (HA), and high performance in disk drives, high-level RAID (Redundant Array of Independent Disks) technology; backup and redundant channels, UPSs, etc.
2) Interception. An unauthorized party gains access to a strategic factor. This falls under the CIA's confidentiality/privacy domain. Tools used to create this include sniffers, botnets, software/hardware keyloggers, Trojans, traceability cookies, password crackers, malware, spyware, creepware, psychic espionage, etc. Countermeasures include encryption, traffic stuffing, steganography, anti-malware, virtual keyboards, Battleship, subliminal channels, etc. Mimikatz is an open-source tool that allows password extraction from Windows systems.
3) Modification. An unauthorized party modifies a strategic factor. This falls under the CIA's integrity domain. Tools used to create malware/viruses include YARA, a tool that detects patterns for writing and identifying malware signatures. Countermeasures include backups, advanced digital signatures, etc.
4) Fabrication. An unauthorized party introduces a pathogen into the system. It falls under the CIA's domain of integrity. Tools for creating it include message repetition (countermeasure: use of timestamps), unauthorized writing, and inserting a clandestine surveillance camera (solution: use of PUF technology). To counter cyberattacks, their structure must be understood. We can summarize five phases of a cyberattack: (a) Reconnaissance. Information is illegally gathered from the system, either actively or passively. (b) Scanning. Vulnerabilities that can be exploited are tested and probed. (c) Gaining access. One or more vulnerabilities are exploited to maliciously access the system. (d) Maintaining access. The attacker remains in the system to achieve the objective of the cyberattack, moving laterally. They remain hidden in a latent state. (e) Covering up/erasing traces. The cyberattacker hides and attempts to erase evidence (logs, records, etc.) of the cyberattack. In a more complete and detailed way, a cyberattack is defined as the Cyber Kill Chain (CKC), which consists of the following phases (the more phases involved, the higher the cost of defending): (1) Pre-compromise. This is divided into three stages: (a) Reconnaissance. This involves identifying which computers or employees are chosen as targets of the cyberattack. Social networks, detectives, sensors, etc., are used for this purpose. (b) Arming. This involves determining which cyberattack vectors were used. (c) Delivery. How was the malicious payload delivered? (2) Compromise. This is divided into two stages: (a) Exploitation. Which vulnerabilities were exploited? (b) Installation. Which modules and filenames contain the malware? (3) Post-compromise. This is divided into two stages: (a) Command and Control (C&C). Which rogue C&C servers does the malware connect to? (b) Actions. Malicious actions to be carried out with lateral movements, currently or in the future (waiting in latent life). Different types of cyber-threat information can be identified, such as: (i) Indicators of Compromise (IOCs), which are technical elements of malware or malware communications that can indicate a cybersecurity compromise. These are observable (benign or malicious events on a network or system) or technical artifacts that suggest an imminent cyber-attack, one that is currently underway, or a compromise that may have already occurred but is hidden and clandestine. Examples of indicators of compromise include the MAC/IPv4/IPv6 address of a suspicious C&C or C2 (Command and Control, the mechanism used by malware to communicate with controllers) server or a suspicious DNS (Domain Name System) domain name, a URL (Uniform Resource Locator) referencing malicious content, a file hash for a malicious executable, the text of the "subject" line of a malicious email message, email addresses of spammers or phishers, FQDNs, PDU payloads, hardware device information, phone/instant-messaging numbers, forum posts, the cyber-attacker's city, file hash, PUF-based device fingerprint, etc. (ii) TTPs (Tactics, Techniques, and Procedures). Describes the behavior of the cyber-threat agent. Tactics are high-level descriptions of behavior, techniques are detailed descriptions of behavior in the context of a tactic, and procedures are even more detailed, lower-level descriptions in the context of a technique. TTPs can describe a cyber threat actor's tendency to use a specific malware variant, order of operations, cyberattack tool (e.g., cyberweapon), delivery mechanism (e.g., phishing or a Watering Hole attack), or exploit. (iii) Cybersecurity alerts. Also known as advisories, bulletins, and vulnerability notes, these are brief, technical notifications regarding current vulnerabilities (CVE: Common Vulnerabilities and Exposures from http://cve.mitre.org ), exploits, and other cybersecurity issues. Cybersecurity alerts originate from sources such as US-CERT (United States Computer Emergency Readiness Team), ISACs (Information Sharing Analysis Centers), NVD (National Vulnerability Database, which provides CVSS (Common Vulnerability Scoring System) values for vulnerabilities), PSIRTs (Product Security Incident Response Teams), commercial cybersecurity service providers, and cybersecurity researchers. etc. (iv) Cyber threat intelligence reports. These are generally documents that describe TTPs, cyber threat actors, types of systems and information targeted, and other cyber threat-related information that provides an organization with greater situational awareness. Cyber threat intelligence is highly processed cyber threat information that has been aggregated, transformed, analyzed, interpreted, or enriched to provide the necessary context for cybersecurity decision-making processes. (v) Tool configurations. These are guidelines for configuring and using tools/mechanisms that support the automated collection, sharing, processing, analysis, and use of cyber threat information/intelligence. For example, tool configuration information may consist of instructions on how to install and use a utility to detect and remove a rootkit, or how to create and customize custom intrusion detection signatures (e.g., Snort), access control lists (ACLs) for routers, or Firewall rules or web filtering configuration files, or capability lists for access control and authorizations, etc. (vi) Data mining/Big-Data/Analytics for cyber threat intelligence. ThreatMiner shows examples of malware, domains, hosts, email addresses for data mining for cyber threat intelligence, CRITS (Collective Research Into Threats).
 CYBER DEFENSES USED IN CYBERSECURITY/PRIVACY PROCESSES.
CYBER DEFENSES USED IN CYBERSECURITY/PRIVACY PROCESSES.
Cybersecurity/privacy integrates processes that include a growing array of cyber defenses, such as:
1) Prevention. This involves hardening and building resilience into systems, isolating systems with VLANs/DMZs/VPNs, and preventing cyberattacks (using tools like IPS, DLP, AV, etc.).
2) Control, regulation, and management. This utilizes various tools such as IAM, ACL, NGFW (Next Generation Firewall), UTM (Unified Threat Management), SIEM (Security Incident and Event Management), DLP (Data Leak Prevention), IPS (Intrusion Prevention System), etc.
3) Early detection. This includes detecting all types of cyber incidents, events, cyberattacks, and intrusions, containing cyber incidents, and confirming and prioritizing them with tools like IDS/HIDS/NIDS/AIDS, etc.
4) Real-time visibility. The goal is to identify the moment of infection in advance and alert automated tools and administrators. This minimizes the window of vulnerability between launching a cyberattack and preventing/detecting it.
5) Prediction. Based on indications of possible extreme behavior. Managing/assessing vulnerabilities/exposures, predicting cyberattacks using behavioral analytics (e.g., NBA, UEBA, EDR), SIEM/log management, NGSOC (Next Generation Security Operations Center), network and endpoint monitoring and forensics, etc., neural networks, AI and all its derivatives: expert systems, federated learning/FL, deep learning/DL, machine learning/ML (involved in every stage of the classification cycle from an object's origins to its numerous relationships and more). Three machine learning technologies are:
a. SVM (Support Vector Machine). Analyzes data, features, and content patterns to make predictions with a higher degree of accuracy than Bayesian networks; It requires the analysis of redundant AI engines and, where applicable, human input to achieve an acceptable level of confidence.
b. Bayesian Networks. These analyze site characteristics to make predictive determinations and provide a model for distinguishing known good sites from bad ones.
c. MED (Maximum Entropy Discrimination). This is an extension of SVM that performs better in classifying noisy and confusing data, but it also requires significant computing power. MED can be integrated with active learning (the process in which other AI units and human experts provide feedback to the machine-learning algorithm when it struggles to classify certain objects during training), active feedback (the process of incorporating human feedback into the machine-learning algorithm while it is actively classifying in the real world, not just during training), and deep learning (which uses a layered approach to improve classification efficiency).
6) Inference. This involves inferring all types of information using tools such as Big Data, Analytics, Artificial Intelligence (LLM/DL/ML), etc. Signatures, traces, and other traces are used.
7) Anticipation. Anticipate cyber threats, malicious events, etc. (using sensors) and be prepared with sufficient resources.
8) Analysis. Use tools such as sandboxing with antivirus, honeypots/honeynets, DMZs, deception mechanisms, etc.
9) Proactive Response. Use investigation/forensics, modify the model or design, make changes, reconfigure, counter-attack, and remediate errors.
10) Proactive Reporting. Generate customized compliance reports.
11) Deception/Misinformation/Disorientation. Use tools such as honeypots/honeynets, Distributed Deception Platforms (DDP), etc.
12) Containment. Contain cyber threats, infections, etc., and then remediate them appropriately, for example, with restores from redundant backups.
13) Remediation. Use backups, resource redundancies, etc.
14) Perimeter and compartmentalization of infections and networks. With VLANs, NGFW, sandboxing, DMZs, etc.
15) Reactive cyber defenses. They act against past or current cybersecurity breaches.
cybersecurity breaches that are likely to occur and are currently occurring.
17) Predictive cyber defenses. They act against potential future cybersecurity breaches that are unexpected or latent.
Currently, unconditional monitoring of cybersecurity and privacy is of paramount importance in IT, OT, IoT, and heterogeneous ecosystems, despite all kinds of trends such as digitization and the exponential use of new technologies, new marketing, blockchain, augmented/virtual/dimmed reality, big data, artificial intelligence/LLMs, etc. From cybersecurity and privacy needs to best practice protocols with the highest level of maturity, the goal is to create capabilities, knowledge, intelligence, services, tactics, strategies, components, and so on. In cybersecurity and privacy, it is useful to employ various approaches; one of them is called OODA (Observe, Orient, Decide, and Act). Some of the methods used to spread cyber threats are: social engineering (the art and science of deception using all human vulnerabilities such as greed, lust, laziness, negligence, cowardice, ignorance, incapacity, etc.), distraction events (using fake news, social media, smokescreens with denial-of-service attacks to avoid suspicion and gain persistence), BYOD (Bring Your Own Device) (the organization allows employees to use their own devices and mobile phones, which may be infected), and infrastructure vulnerabilities (which can be computational, network, cybersecurity, organizational, human, AI, governance/management, etc.).
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2023.
- Areitio, J. “Early Cancellation by DAIM/MIAD of Singularities and Techniques Generating Insidious Cyberattacks”. Conectronica Magazine. No. 256. May 2023.
- Gupta, I. “Operationalizing Expectations and Mapping Challenges of Information-Privacy and Data-Protection Measures: A Machine-Generated Literature Overview”. Springer 2024.
- Hubbard, D.W. and Seiersen, R. “How to Measure Anything in Cybersecurity Risk”. Wiley John and Sons 2023.
- Wilson, D.C. “Cybersecurity”. The MIT Press Essential Knowledge Series. The MIT Press. 2022.
- Stewart, A.J. “A Vulnerable System: The History of Information Security in the Computer Age”. Cornell University Press. 2023.
- Xu, Z., Choo, K.-KR, Dehghantanha, A., Parizi, R. and Hammoudeh, M. “Cyber Security Intelligence and Analytics”. Springer. 2020.
- Di Pietro R. “New Dimensions of Information Warfare”. Springer. 2021.
- Smith: JEH “The Internet Is Not What You Think It Is: A History, a Philosophy, a Warning”. Ed.-Princeton University Press-2023.
- Gupta, I. “Expectations vs Realities of Information Privacy and Data Protection Measures: A Machine-generated Literature Overview.” Springer-2023.
- Yu, S. and Cui, L. “Security and Privacy in Federated Learning”. Springer-2023.
- Knijnenburg, BP, Page, X., Wisniewski, P. (Editor), Lipford, HR et al. “Modern Socio-Technical Perspectives on Privacy.” Springer-2022.
Author: Prof. Dr. Javier Areitio Bertolín – Director of the Networks and Systems Research Group.