INTRODUCTION
 The concept of Industry 4.0 refers to cyber-physical production systems that integrate execution systems with analytical and planning capabilities. It represents a new way of organizing production resources based on the implementation of smart factories adapted to current production needs and processes, as well as the optimization of resources. Industry 4.0 offers numerous benefits, such as the interconnection and interoperability of elements through the IIoT (Industry Internet of Things), digital transformation, sensor monitoring and data aggregation, support for continuous improvement, decentralized decision-making, and increased productivity. However, this ideal scenario, coupled with the interconnectedness of Industry 4.0, also creates vulnerabilities that can lead to a wide range of cyberattacks. Preventing cyberattacks that compromise the security and privacy of production equipment and data is a top priority. It is clear that every Industry 4.0 ecosystem must be governed by cybersecurity and privacy, and within this ecosystem, several areas can be identified: (1) At the core are the factories of the future and factory clusters. At the most basic level are additive manufacturing with 3D printers (massive customization, rapid prototyping, etc.), advanced materials and nanotechnology (connectivity, added intelligent value to products, etc.), robotics (real-time autonomous productivity, total transparency), mechatronics (mechanics with cybernetics integration), and autonomous ground and air vehicles (lower costs, optimized workflow). At a higher level are sensors and actuators (traceability, predictive capabilities), and advanced manufacturing systems (cyber-physical systems, fully automated numerical control, M2M communication, and fully connected systems). At a higher level are cloud computing and Big Data/Analytics (enabling creativity, collaborative manufacturing, etc.). (2) Interacting with cloud computing would be the most external cybersecurity and privacy services (technological products with longer lifecycles, greater protection for IIoT-based manufacturing). (3) Interacting with the plants of the future would be supplier clusters, Logistics 4.0 (fully integrated supply chain, complete coordination, interconnected systems), customers with IIoT (real-time data capture, optimized stocks, object labeling, reduced waste, object-to-Internet communication using low-power radio-frequency RFID with and without chips, Bluetooth, ZigBee, UWB, etc.) and mass customization (flexibility, on-demand manufacturing, perfect alignment with customer needs, with efficient mass production, higher-level customer-marketing interaction, etc.). (4) Interacting with the plants of the future would reveal the resources of the future (wind turbines, solar panels, geothermal energy, tidal-wave energy, etc. are renewable and clean energies and are found everywhere.
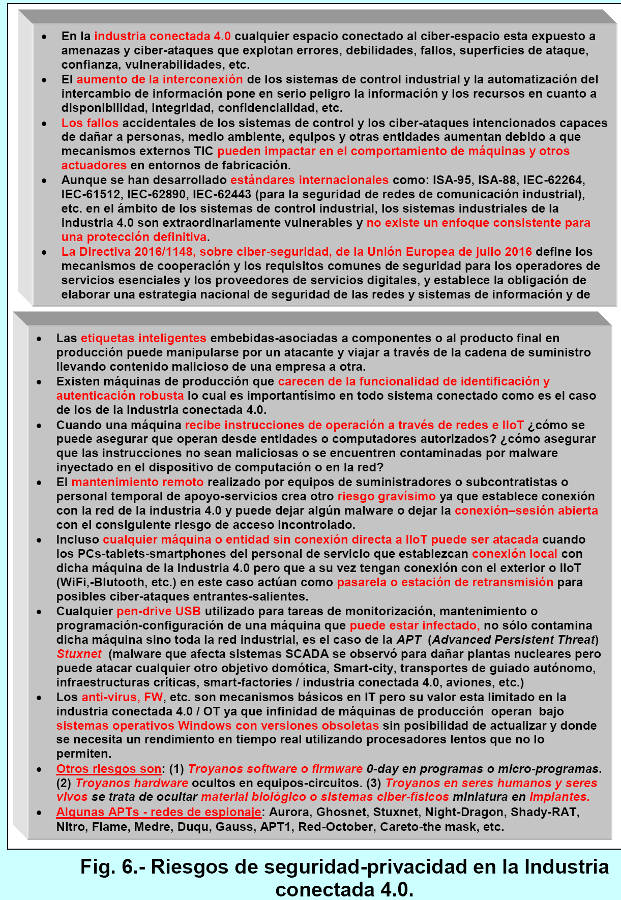
The concept of Industry 4.0 refers to cyber-physical production systems that integrate execution systems with analytical and planning capabilities. It represents a new way of organizing production resources based on the implementation of smart factories adapted to current production needs and processes, as well as the optimization of resources. Industry 4.0 offers numerous benefits, such as the interconnection and interoperability of elements through the IIoT (Industry Internet of Things), digital transformation, sensor monitoring and data aggregation, support for continuous improvement, decentralized decision-making, and increased productivity. However, this ideal scenario, coupled with the interconnectedness of Industry 4.0, also creates vulnerabilities that can lead to a wide range of cyberattacks. Preventing cyberattacks that compromise the security and privacy of production equipment and data is a top priority. It is clear that every Industry 4.0 ecosystem must be governed by cybersecurity and privacy, and within this ecosystem, several areas can be identified: (1) At the core are the factories of the future and factory clusters. At the most basic level are additive manufacturing with 3D printers (massive customization, rapid prototyping, etc.), advanced materials and nanotechnology (connectivity, added intelligent value to products, etc.), robotics (real-time autonomous productivity, total transparency), mechatronics (mechanics with cybernetics integration), and autonomous ground and air vehicles (lower costs, optimized workflow). At a higher level are sensors and actuators (traceability, predictive capabilities), and advanced manufacturing systems (cyber-physical systems, fully automated numerical control, M2M communication, and fully connected systems). At a higher level are cloud computing and Big Data/Analytics (enabling creativity, collaborative manufacturing, etc.). (2) Interacting with cloud computing would be the most external cybersecurity and privacy services (technological products with longer lifecycles, greater protection for IIoT-based manufacturing). (3) Interacting with the plants of the future would be supplier clusters, Logistics 4.0 (fully integrated supply chain, complete coordination, interconnected systems), customers with IIoT (real-time data capture, optimized stocks, object labeling, reduced waste, object-to-Internet communication using low-power radio-frequency RFID with and without chips, Bluetooth, ZigBee, UWB, etc.) and mass customization (flexibility, on-demand manufacturing, perfect alignment with customer needs, with efficient mass production, higher-level customer-marketing interaction, etc.). (4) Interacting with the plants of the future would reveal the resources of the future (wind turbines, solar panels, geothermal energy, tidal-wave energy, etc. are renewable and clean energies and are found everywhere.
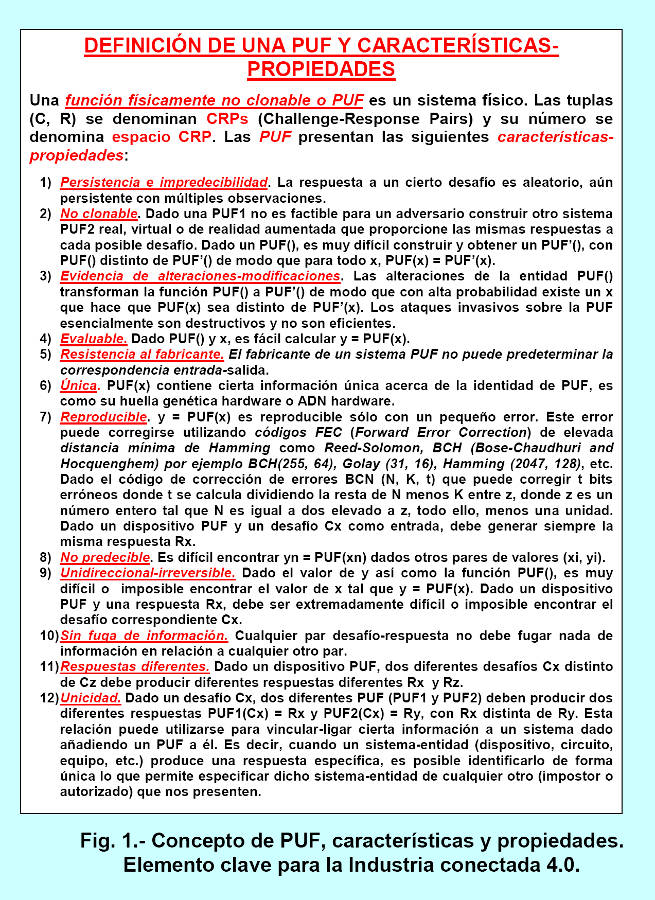
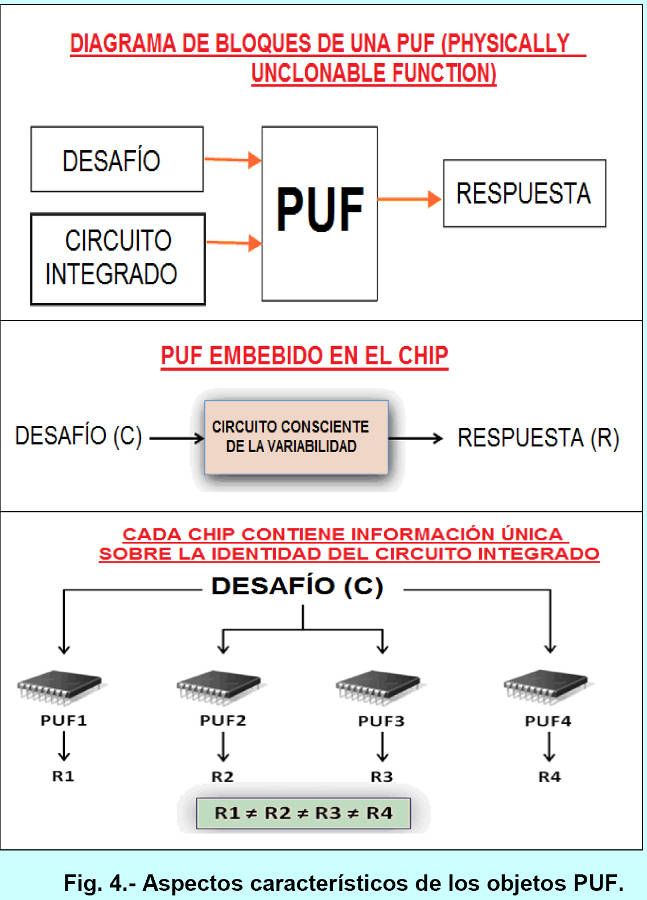
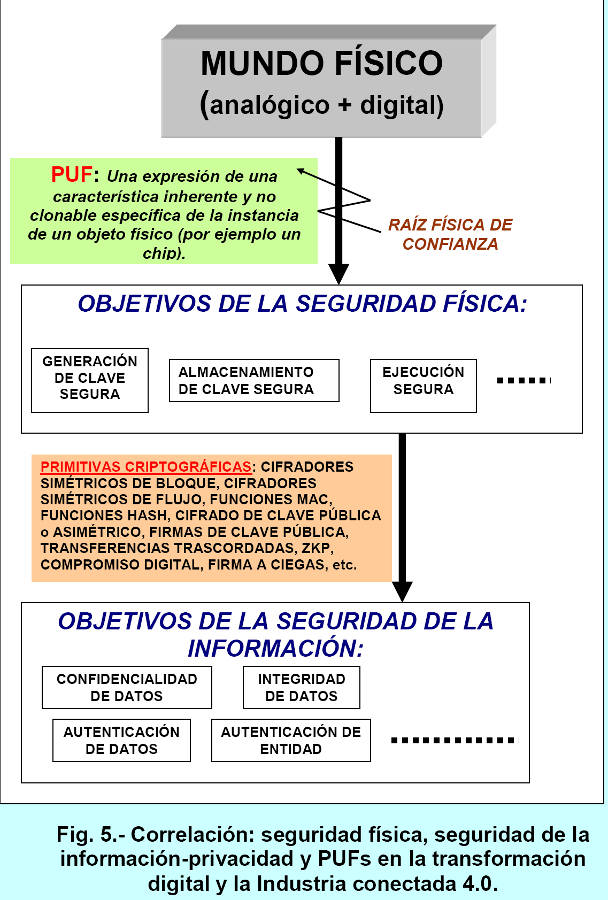
 It is possible to store such energy and is an alternative to conventional materials like coal, etc. A key component for the security and privacy of Industry 4.0 ecosystems is the PUF (Positive Function Unit). A PUF is a function embedded in a physical object, such as a chip or integrated circuit. When queried with a challenge z, the PUF generates a response w that depends on both the challenge z and the unique analog-digital physical properties of the device and the material containing the PUF (i.e., the unique internal structure of the PUF, which is caused by random manufacturing variations; these variations are typically not recreatable and are not under the control of the PUF manufacturer). Because PUFs are subject to noise introduced by environmental variations, they return slightly different responses when queried with the same challenge many times. However, this can be mitigated using FEC (Fire Error Correction) technology with a very high Hamming distance. PUF (Publicly Identified Facility) architectures are implemented on a wide variety of platforms, including FPGAs (Field-Programmable Gate Arrays), ASICs (Application-Specific Integrated Circuits), COTS (Commercial Off-The-Shelf) products, microcontrollers, DSPs (Digital Signal Processors), ASSPs (Application-Specific Standard Products), SoCs (System-On-Chip), GPUs (Graphics Processing Units), ARM (Advanced RISC Machines), microprocessors, and more. Within a single platform, different technologies can be used, such as CMOS nodes of varying scales. PUFs introduce the "e-fingerprint" approach, which means that identification becomes a function of the device's nature rather than a secret it possesses. Modern information security is progressively revealing its diverse facets, and consequently, an ever-expanding spectrum of tasks must be addressed. In addition to conventional cryptography, which provides security for data stored or communicated over a network, modern security must address a growing set of other needs such as trust, anonymity, privacy of actions, and so on. Early cryptographic mechanisms, protocols, and methods were designed to provide security for physically well-protected devices. However, today a large majority of devices (RFID/NFC tags with and without chips, smart nodes in Wireless Sensor Networks (WSNs), tablets, etc.) are easily accessible, physically unprotected, and may even reside in harsh environments. Therefore, modern security primitives (such as PUFs) must be resilient to all types of physical and side-channel attacks, and they must also be inexpensive, low-power, and meet the limitations of portable computing equipment and mobile communication devices based on finite batteries and low-power CPUs. Intrinsic hardware security is a recent area that deals with the secure storage of secret keys. Generating secret keys from the intrinsic properties of silicon, for example intrinsic PUFs, does not require permanently storing secret keys and the key is only present in the device for a minimal amount of time.
It is possible to store such energy and is an alternative to conventional materials like coal, etc. A key component for the security and privacy of Industry 4.0 ecosystems is the PUF (Positive Function Unit). A PUF is a function embedded in a physical object, such as a chip or integrated circuit. When queried with a challenge z, the PUF generates a response w that depends on both the challenge z and the unique analog-digital physical properties of the device and the material containing the PUF (i.e., the unique internal structure of the PUF, which is caused by random manufacturing variations; these variations are typically not recreatable and are not under the control of the PUF manufacturer). Because PUFs are subject to noise introduced by environmental variations, they return slightly different responses when queried with the same challenge many times. However, this can be mitigated using FEC (Fire Error Correction) technology with a very high Hamming distance. PUF (Publicly Identified Facility) architectures are implemented on a wide variety of platforms, including FPGAs (Field-Programmable Gate Arrays), ASICs (Application-Specific Integrated Circuits), COTS (Commercial Off-The-Shelf) products, microcontrollers, DSPs (Digital Signal Processors), ASSPs (Application-Specific Standard Products), SoCs (System-On-Chip), GPUs (Graphics Processing Units), ARM (Advanced RISC Machines), microprocessors, and more. Within a single platform, different technologies can be used, such as CMOS nodes of varying scales. PUFs introduce the "e-fingerprint" approach, which means that identification becomes a function of the device's nature rather than a secret it possesses. Modern information security is progressively revealing its diverse facets, and consequently, an ever-expanding spectrum of tasks must be addressed. In addition to conventional cryptography, which provides security for data stored or communicated over a network, modern security must address a growing set of other needs such as trust, anonymity, privacy of actions, and so on. Early cryptographic mechanisms, protocols, and methods were designed to provide security for physically well-protected devices. However, today a large majority of devices (RFID/NFC tags with and without chips, smart nodes in Wireless Sensor Networks (WSNs), tablets, etc.) are easily accessible, physically unprotected, and may even reside in harsh environments. Therefore, modern security primitives (such as PUFs) must be resilient to all types of physical and side-channel attacks, and they must also be inexpensive, low-power, and meet the limitations of portable computing equipment and mobile communication devices based on finite batteries and low-power CPUs. Intrinsic hardware security is a recent area that deals with the secure storage of secret keys. Generating secret keys from the intrinsic properties of silicon, for example intrinsic PUFs, does not require permanently storing secret keys and the key is only present in the device for a minimal amount of time.
 The field extends to hardware-based security primitives and protocols such as block ciphers (like AES, 3DES, and IDEA) and stream ciphers (like OTP/Vernam) embedded in hardware, thereby improving the security of integrated circuits. At the application level, there is growing interest in hardware security for RFID/NFC systems and their associated system architectures. Digital keys are traditionally stored in Non-Volatile Memory (NVM) for cryptographic applications. However, digital keys in NVMs have proven vulnerable to invasive physical attacks. Complex tamper-proofing and tamper-sensing mechanisms have been implemented in hardware to protect digital keys in NVMs, but this significantly increases the device's power consumption, which also limits the use of such anti-tampering methods for resource-constrained devices such as smartcards, RFID/NFC tags, and so on. Some of the characteristics of PUFs are uniqueness, reliability, and unpredictability. The PUF solution from Intrinsic-ID is available for DesigWare ARC EM processors (http://www.synopsys.com/desigware). It allows designers to extract a unique "device fingerprint" from the standard embedded SRAM. This "hardware fingerprint" can be used as a device identifier or as a secret/private cryptographic key. In the latter case, it creates a secure key protection enclosure without the need to add NVM (Non-Volatile Memory) or a dedicated security core.
The field extends to hardware-based security primitives and protocols such as block ciphers (like AES, 3DES, and IDEA) and stream ciphers (like OTP/Vernam) embedded in hardware, thereby improving the security of integrated circuits. At the application level, there is growing interest in hardware security for RFID/NFC systems and their associated system architectures. Digital keys are traditionally stored in Non-Volatile Memory (NVM) for cryptographic applications. However, digital keys in NVMs have proven vulnerable to invasive physical attacks. Complex tamper-proofing and tamper-sensing mechanisms have been implemented in hardware to protect digital keys in NVMs, but this significantly increases the device's power consumption, which also limits the use of such anti-tampering methods for resource-constrained devices such as smartcards, RFID/NFC tags, and so on. Some of the characteristics of PUFs are uniqueness, reliability, and unpredictability. The PUF solution from Intrinsic-ID is available for DesigWare ARC EM processors (http://www.synopsys.com/desigware). It allows designers to extract a unique "device fingerprint" from the standard embedded SRAM. This "hardware fingerprint" can be used as a device identifier or as a secret/private cryptographic key. In the latter case, it creates a secure key protection enclosure without the need to add NVM (Non-Volatile Memory) or a dedicated security core.
 TAXONOMY OF PUF ARCHITECTURE CLASSIFICATIONS FOR CONNECTED INDUSTRY 4.0.
TAXONOMY OF PUF ARCHITECTURE CLASSIFICATIONS FOR CONNECTED INDUSTRY 4.0.
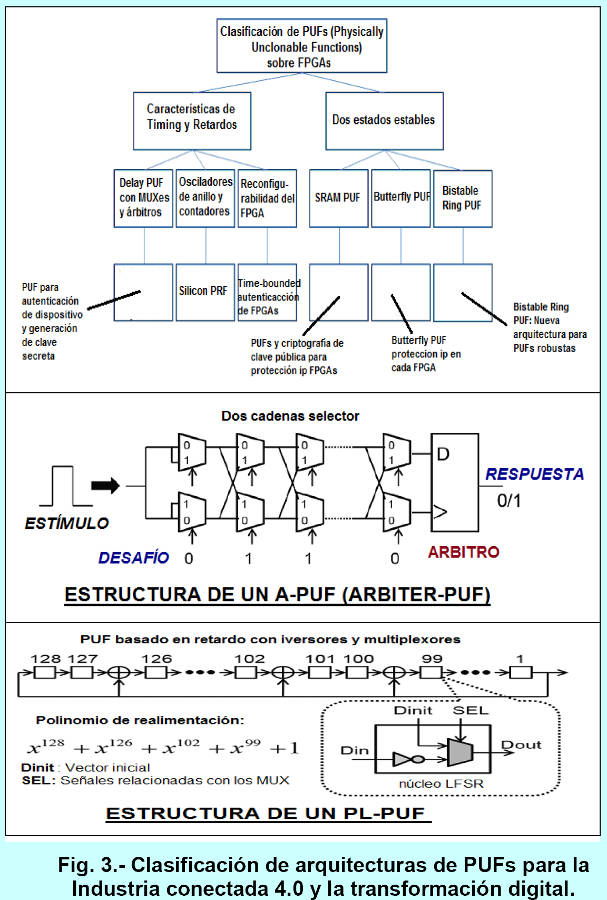
Throughout history, different methods for synthesizing PUFs have emerged, ranging from measuring the distortion of reflected light to relying on manufacturing inconsistencies between chips (physical properties of the materials in which they are instantiated). PUFs based on conventional microelectronic circuits, such as RO-PUFs (Ring Oscillator-PUFs), A-PUFs (Arbiter-PUFs), and SRAM-PUFs, exploit uncontrolled process variations in CMOS (Complementary Metal-Oxide-Semiconductor) manufacturing technology. In fact, the silicon-based identification circuits proposed in 2000 can also be classified as PUFs, as they too exploit randomness within the hardware device to generate a secret key. The next generation of PUFs is beginning to be implemented using emerging nanoelectronic and quantum devices. Nanotechnologies such as PCM (Phase Change Memory), STT-MRAM (Spin-Transfer Torque Magnetic Random-Access Memory), CNFETs (Carbon-Nanotube Field-Effect Transistors), and memristors (also known as bipolar memristor, memristive device, or RRAM; a contraction of the words "memory" and "resistor," a term coined in 1971 by Leon Chua. An example is the memristor-based nano-crossbar PUF architecture, or mrPUF) possess more severe levels of inherent randomness due to manufacturing process variations (e.g., thickness, cross-sectional area, or doping profile). In the quantum domain, the QR-PUF (Quantum-Readout PUF) is challenged using a quantum state. Some of the most commonly used PUF architectures, considering their composition, support, and structure, are:
1) Silicon PUFs and non-silicon PUFs, including crystal PUFs and timing PUFs.
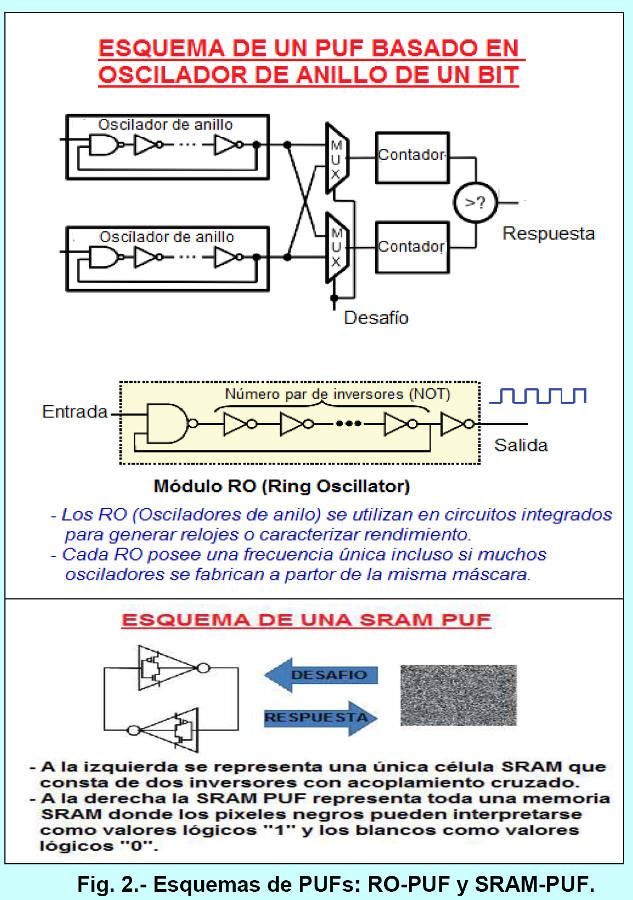
2) RO PUFs (Ring Oscillator-Based PUFs). These are based on the frequency differences of multiple ring oscillators. A ring oscillator is a cascaded connection of an even number of NOT inverter logic gates. Because there is an even number of gates, it will produce a continuously changing or oscillating signal. As a combination of circuits, the RO PUF can be instantiated on a piece of silicon as an FPGA or ASIC (Application-Specific Integrated Circuit). Depending on the number of inverter gates used, as well as the propagation delay of each inverter individually, the output frequency of one RO PUF can differ from another. The RO PUF is one of the leading microelectronic PUFs due to its high reliability.
3) Optical PUFs (O-PUFs). It consists of a transparent material to which many light-scattering particles are randomly added during its manufacture. When a laser beam is shone on the PUF, a random pattern of dots will appear. The position and angle of the laser represents the challenge, while the dot pattern is recorded, quantized, and encoded to form the PUF's response. An optical PUF is constructed by taking a transparent material and randomly coating it with light-scattering particles. A laser beam is focused on the material, and the resulting pattern is recorded. The image is processed and becomes the PUF's response.
4) APUF (Arbiter PUF). These use FPGAs (Field-Programmable Gate Arrays) and are based on the delay race between two symmetrical delay lines. They consist of selection chains in which the signal inputs are selected at the selectors that comprise the challenge, and the signal output from the arbiters is the response. If the upper signal reaches the lower arbiter before the lower one, the response is "one"; otherwise, it is "zero." The path of the selector chains and the delays that differentiate between two signals are determined by the challenge, so the response is a function of the challenge. Because the speeds of the two signals in the selector chains are affected by device variation, the response to a given challenge will not always be the same for different APUFs. Therefore, a set of Challenge Response Pairs (CRPs) from an APUF constitutes chip-specific information that can be used for authentication of that chip.
5) PL-PUFs (Pseudo-LFSR PUFs). These use FPGAs. They are delay-based PUFs with a structure similar to an LFSR (Linear-Feedback-Shift-Register), even using an irreducible feedback polynomial such as x128+x126+x102+x99+1. A PL-PUF is not composed of shift registers but of combinational logic consisting of multiplexers and inverters at each node.
6) SRAM-PUFs. They are based on the metastability of a cross-coupled device. It consists of two cross-coupled inverters and two additional transistors for external connection, for a total of six transistors. It is fast for short-term data storage.
 Another classification of PUFs, taking into account additional operational aspects, is:
Another classification of PUFs, taking into account additional operational aspects, is:
1) RPUFs (Reconfigurable PUFs). These have the ability to change their response to the same challenge instead of exhibiting static challenge-response behavior. They are useful in applications such as secret revocation or updates. They have the following properties: (i) CRPs are unpredictable after reconfiguration, even if the CRPs were known before the reconfiguration. (ii) The security properties of RPUFs are preserved after reconfiguration. (iii) The reconfiguration is uncontrollable, so it is not based on updating hidden parameters or devices. RPUFs allow extending the regular challenge-response behavior of a PUF with an additional operation called reconfiguration. This reconfiguration has the effect of changing the partial or complete challenge-response behavior of the PUF randomly and irreversibly, resulting in a new PUF. There are different implementations of RPUFs where the reconfiguration mechanism is an actual physical reconfiguration of randomness in the PUF. An extension of an O-PUF is to use a more powerful laser beam that causes a random rearrangement of the optical scattering, leading to a new challenge-response behavior.
2) CPUFS (Controlled PUFs). These use a robust PUF as a building block but add control logic surrounding the PUF. This logic prevents challenges from being freely applied to the PUF and prevents direct reading of its responses. This control logic can be used to prevent spoofing attacks. However, if the outputs of the embedded robust PUF can be directly examined, then it may be possible to spoof the robust PUF and break the controlled PUF's protocol. A PUF is said to be a CPUF if it can only be accessed using an algorithm that is physically linked to the PUF in an inseparable way. An attempt to break the link between the PUF and the access algorithm should lead to the destruction of the PUF. A CPUF combines a PUF with another cryptographic primitive. Some advantages of converting a PUF into a CPUF are: (i) A cryptographic hash function to generate the PUF challenges can prevent chosen challenge attacks, i.e., make model-building attacks more difficult. (ii) An error-correction algorithm acting on the PUF measurements makes the final response much more reliable, reducing the probability of a one-bit error in the response to virtually zero. (iii) A cryptographic hash function applied to the error-corrected outputs effectively breaks the link between the responses and the physical details of the PUF measurement. This makes model-building attacks much more difficult. When hashing a PUF response, error correction is essential since any minute deviation from the response yields an entirely unrelated hash result. (iv) The hash function that generates the PUF challenges can take additional inputs, allowing a PUF to have multiple personalities. This can be desirable when the PUF is used in privacy-sensitive applications.
3) POKs (Physically Obfuscated Keys). The only requirement for a POK is that the key is permanently stored in a physical form rather than a digital one, making it difficult for an attacker to learn the key through a probe attack. Furthermore, an invasive attack on the device storing the key should destroy the key and render its further use impossible, thus providing tamper evidence. POKs and PUFs are very similar concepts, and POKs can be constructed from PUFs (with tamper evidence) and vice versa.
4) PUF Recombination. Recombination can be applied to a system containing different types of PUFs. In genetic engineering, recombination refers to the process where genetic material (in this case, silicon PUF circuits) is rearranged and joined to generate other genetic material. Among its advantages, it is an excellent material for key generation and authentication, allowing for an increased challenge-response space (e.g., two to the power of one hundred and twenty-eight), increasing environmental stability, reducing complexity for key generation, and is achievable on FPGAs and ASICs, reducing the risks of ASIC deployments by using prototyping and fast FPGA emulation, and offering protection for FPGAs and ASIC-based systems and devices.
Depending on the number of Challenge Response Pairs (CRPs) a PUF can produce, PUFs can be classified into two main categories:
1) Weak PUFs. These support a small number of CRPs, so the CRPs can be completely read outward within a very short time once an attacker has full physical access to the PUF. A weak PUF is defined by two properties: (i) It is impossible to clone or physically duplicate. (ii) The number of CRPs is limited and depends linearly or polynomially on the number of bits in the challenge. Some examples of weak PUFs are SRAM-PUF, Coating-PUF, Butterfly-PUF, etc. They are used for key storage applications. For example, a unique internal secret key is obtained from the responses of several weak PUFs.
2) Robust PUFs (sometimes called PRFs, Physical Random Functions). They are defined by three properties: (i) Impossible to clone or physically duplicate. (ii) They support a very large number of CRPs, so an attacker cannot mount a brute-force attack within a realistic time, ideally demonstrated by an exponential number of CRPs. (iii) They are resilient to model building attacks by providing a polynomial number of chosen CRPs so that an attacker cannot predict the response of a PUF to a randomly selected, unused challenge. Some examples of robust PUFs are Optical-PUF, XOR-PUF, etc. Some applications of these PUFs are key establishment, identification, authentication, transcorded transfer, null knowledge proofs, SMPC (Secure Multi-Party Computation), etc.
Cybersecurity and privacy (protection against all types of attacks) must be paramount in the four most relevant aspects of Industry 4.0: vertical integration (high flexibility, zero batch size), people as the main drivers of the value chain (systems follow people's needs, skills development by people, and mass customization), horizontal integration (value chains spanning the globe), and consistent engineering (systems engineering throughout the entire lifecycle with digital production). Industry 4.0, through the IIoT, has opened Pandora's box to all types of cyberattacks, from the most conventional to the most advanced, such as APT-based attacks. Addressing cybersecurity and privacy protection is a top priority, and one of the tools for this purpose is Physically Unclonable Functions (PUFs). Sandia National Laboratory markets technology that uses cryptographic cybersecurity techniques based on PUFs (the device is called SecuritySeal) to protect physical objects from potential fraud, such as counterfeiting radioactive materials, pharmaceuticals in containers, and so on. Cyber-Physical Systems (CPSs) are a computing paradigm increasingly used in various technologies and are the foundation of Industry 4.0. Achieving reliable CPSs requires mechanisms that ensure the integrity and authenticity of these systems. PUFs based on semiconductor technologies are presented as a highly suitable solution for building connections between the cyber (digital) and physical (analog) worlds and protecting CPSs in avionics, autonomous vehicles, factory machinery, production systems, industries, critical infrastructure with and without SCADA, financial engineering, and more. Some tasks performed by secure hardware components such as PUFs include: key storage, asymmetric cryptography (signature and encryption), for example, based on ECC/RSA-CRT, session key generation, random number generation, access rights verification, integrity verification, secure data storage, resistance against hardware attacks, certification/attestation, etc. We can identify various secure hardware components in mobile phones: SIM cards, eSIMs, security chips, secure SD cards, etc. In March 2007, the Idaho National Laboratory of the U.S. Department of Energy conducted an experiment or test called Aurora to demonstrate how a cyberattack could destroy physical components of an electrical grid. The experiment used software that rapidly opened and closed a circuit in a diesel generator, causing it to explode. This vulnerability was named the Aurora vulnerability and can therefore be exploited by a cybersecurity threat. The Department of Homeland Security (DHS) has since been working with the electrical industry to prevent future threats of this type. Currently, there are already robotic vacuum cleaners that move autonomously and allow remote video surveillance via smartphone, making them vulnerable to hacking by any attacker. Even more dangerous are the latest generation of toys and baby monitors, such as My Friend Cayla dolls, Hello Barbie, the Fisher-Price Smart Toy Bear, and the i-Que smart robot, which connect to the internet, record conversations with children, and allow some remote interaction via the internet (photos taken by the Bear, etc.).
AUTHOR:
Prof. Dr. Javier Areitio Bertolín,
Professor at the Faculty of Engineering, University of Deusto.
Director of the Networks and Systems Research Group.
REFERENCES.
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2017.
- Areitio, J. “Exploration and cross-cutting analysis of the IoE from the perspective of cybersecurity and privacy”. Conectrónica Magazine. No. 193. February 2016.
- Areitio, J. “Systematic classification of cyberattacks and approaches to assessing cyber threats in IoE ecosystems”. Conectrónica Magazine. No. 199. September 2016.
- Areitio, J. “Identification, exploration and classification of cyberattack surfaces at the data and code level in the IoE”. Conectrónica Magazine. No. 200. October 2016.
- Intrinsic-ID spin-off company of Philips Electronics manufactures PUF for embedded authentication, URL: https://www.intrinsic-id.com/products/
- Wachsmann, C. and Sadeghi, AR “Physically Unclonable Functions (PUFs): Applications, Models and Future Directions”. Morgan & Claypool Publishers. 2015.
- Verayo Company founded in 2005, manufactures PUF technology, URL: http://www.verayo.com/
- Mukhopadhyay, D. and Chakraborty, RS “Hardware Security: Design, Threats and Safeguards”. Chapman and Hall/CRC. 2014.
- RAMI4.0 (Reference Architecture Model for Industry 4.0) by ZVEI (German Electrical and Electronic Manufacturers' Association).
- Tehranipoor, M. and Wang, C. “Introduction to Hardware Security and Trust”. Springer. 2012.
- Patterson, DG “Physical Security Protection Systems Implementation and Operation”. CRC Press. 2016.
- Bohm, C. and Hofer, M. “Physical Unclonable Functions in Theory and Practice”. Springer-Verlag. 2013.
- Sadeghi, AR and Naccache, D “Towards Hardware-Intrinsic Security: Information Security and Cryptography”. Springer. Berlin. 2010.
- Tehranipoor, M., Salmani, H. and Zhang, X. “Integrated Circuit Authentication: Hardware Trojans and Counterfeit Detection”. Springer. 2014.
- Qu, G. and Potkonjak, M. “Intellectual Property Protection in VLSI Designs. Theory and Practice. Kluwer. 2003.
- Dittmann, A., Heinrichs, B., Hellwig, S. and Seewald, MG “Internet of Things / Internet of Everything: A Practical Architecture Approach”. Cisco Press. 2016.
- Sadeghi, A.-R. and Naccache, D. “Towards Hardware-Intrinsic Security: Information Security and Cryptography”. Springer-Verlag.
- Project on PUFs: European H2020 HECTOR Project. URL: http://www.hector-project.eu/
.