INTRODUCTION.
NG-CS/CR is key not only for business continuity, productivity, competitiveness, etc., but also for the survival of our society. NG-CS/CR exhibits extreme effectiveness, efficiency, efficacy, and maturity, supported by a massive, advanced, superior, multidimensional, self-verified, self-tested, self-monitored, and continuously self-evaluated AI base, with extreme omnidirectional global inference and predictability capabilities across all types of assets: entities, data, networks, clouds, edges, IT/OT/CPS/IoT/IoMT/IoIT infrastructures, etc. It integrates a comprehensive, in-depth structure of protection levels and components, all certified according to the most relevant standards such as ISO/IEC, ANSSI, ENS, UNE, NIST, ETSI, CC-EAL, etc., by accredited external entities on an ongoing basis. It operates as a dynamic, automated/self-testing whole, with extreme factorization and very high predictability and anticipation in all areas/approaches/strategies/tactics/techniques/procedures/mechanisms at all levels, providing deep, total protection based on self-verified actions/safeguards/countermeasures with extreme factorization, both defensive and offensive. All types of defensive countermeasures/safeguards are used, such as CIA (Confidentiality-Integrity-Availability). Confidentiality aims to prevent all types of malicious, holistic observation/surveillance of sensitive data/metadata/information/intelligence/personnel, etc., acting against:
(1) All kinds of clandestine eavesdropping (tapping copper/fiber optic cables/etc.; malicious voice capture on mobiles/PCs/etc., EM signals (remote clandestine capture of signals from PCs/CPDs, data terminals, etc. as countermeasures Faraday cages), acoustic signals, etc. (as countermeasures limit surveillance/use of all types of signal jammers/RF/interference generators, encryption/steganography/end-to-end subliminal channels/etc.).
(2) Day and night clandestine optical surveillance in all possible vision spectra: visible/infrared/UV/etc. with photo/video/TV/etc. cameras of people/entities/etc. deployed on drones/streetlights/poles/satellites/ATMs, etc.
(3) Clandestine surveillance by geolocation using LEO/MEO/etc. satellite networks (Starlinks/GPS/Galileo/Glonass/Beidou/etc.) and clandestinely placing implanted chips in the body or in clothing/footwear to be able to know the geographical position and movements of the entities (people and non-people) to be tracked, know their place of work/home/leisure/etc.
(4) Clandestine surveillance of the times and moments in which the entities carry out their actions.
(5) Clandestine surveillance of our Web browsing: What are we looking for?, our tastes, who are we contacting: by instant messaging (Messenger/Whatsapp/Telegram/Line/ICQ/etc.), by email, Web, social networking websites/Social Media/etc.
(6) Clandestine surveillance of all our activity (work/payments-collections/transactions/tastes/fears/weaknesses/illnesses/interaction-with-other-people/etc.), bank cards, electronic-wallets-on-mobiles, loyalty cards in supermarkets/department stores, etc. Where?/Frequency?/Times?/Amounts?/etc.)); Authentication (its objective is to demonstrate that the identity of an entity is who it claims to be. For this, multiple factors are used such as: “what one knows” (e.g., high-entropy passwords/PINs, guessing riddles/problems/etc.), “what one carries” (e.g., smart cards/smartphones/ship games/chip implants in their body, etc.), “what one is” (physiological biometrics such as fingerprints, DNA, retina, iris, etc. and behavioral biometrics, such as: the way of walking, speaking, writing, signing, instinctive gestures, etc.), “where one is geographically located” (geolocation by satellite networks, by triangulation of antennas for mobile/cellular telephony, etc.), “the instant of time in which the authentication is carried out” (year/month/day/hour/minute/second/etc.); Availability (aims to provide backup resources/elements to offer "fault tolerance/cyber-attacks" such as encrypted backups (of hardware/firmware/software/APPs/APIs) located in several remote sites, replicated/redundant communication channels via fiber/copper/wire and satellites, redundant power supply using generators/UPSs/etc.); Authorization (aims to protect by specifying what operations each subject/entity can perform on an object/resource (such as read, write, execute, delete, create, etc.). For this, access control matrices are used where the columns are the subjects and the rows are the objects; the columns and rows of the matrix form the ACLs (Access Control Lists) and the CLs (Capability Lists)); Non-repudiation (aims to prevent any entity from denying an action/operation it has performed; TTPs/Trusted Third Parties are used); integrity (aims to protect against any illegal modification/change of hardware devices, stored, in transit, running, or updated content/software/firmware; countermeasures include the use of digital signatures/hash functions/NG-PUF hardware functions/etc.); privacy (which is a right, aims to protect/defend people from all kinds of actions/enemies against their lives/health/rights/attempts to modify their behavior, their personal/sensitive data/information, clandestine surveillance/freedom/socialization/etc. It is strongly related to confidentiality. It helps safeguard important values such as reputation/autonomy/dignity/freedom/health/etc.); access control (its objective is to protect access in general based on IAA).

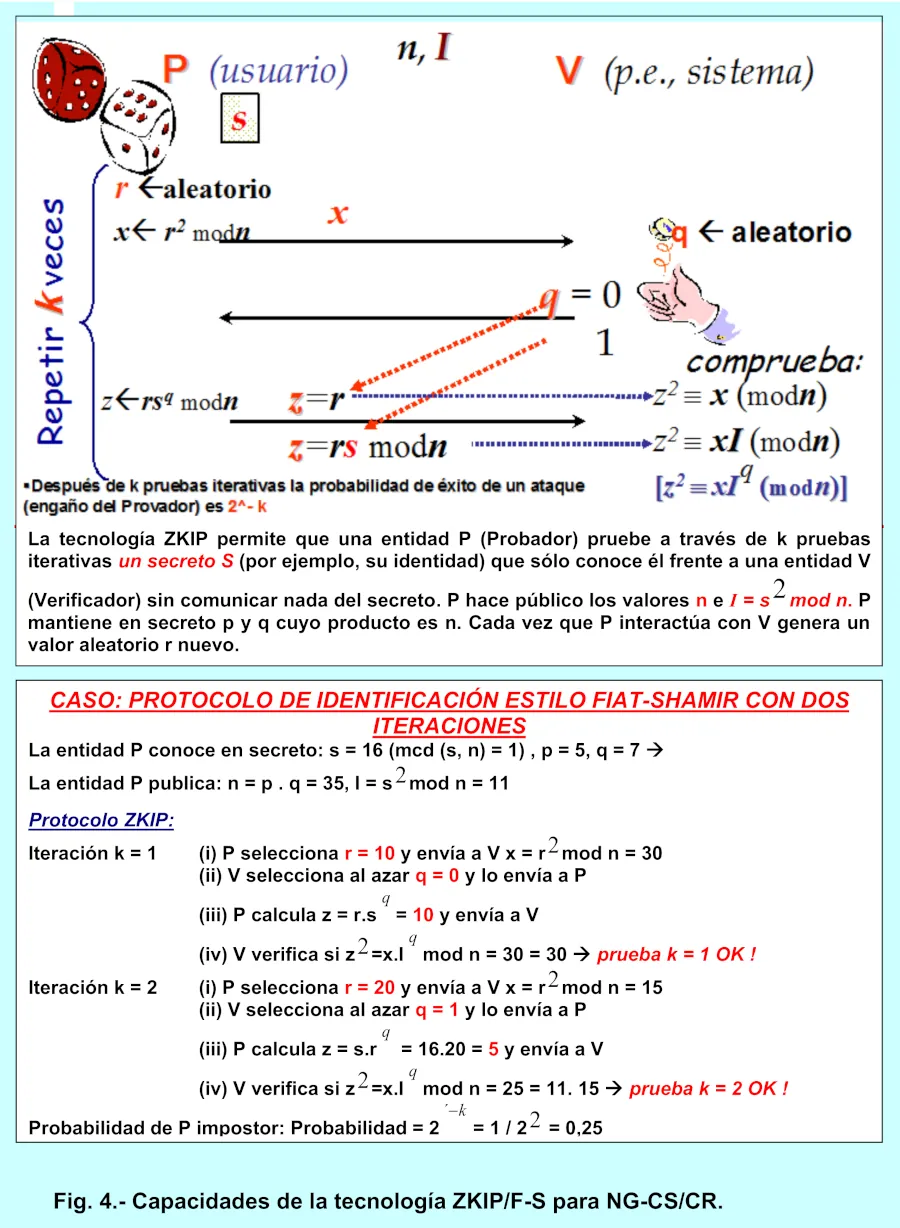
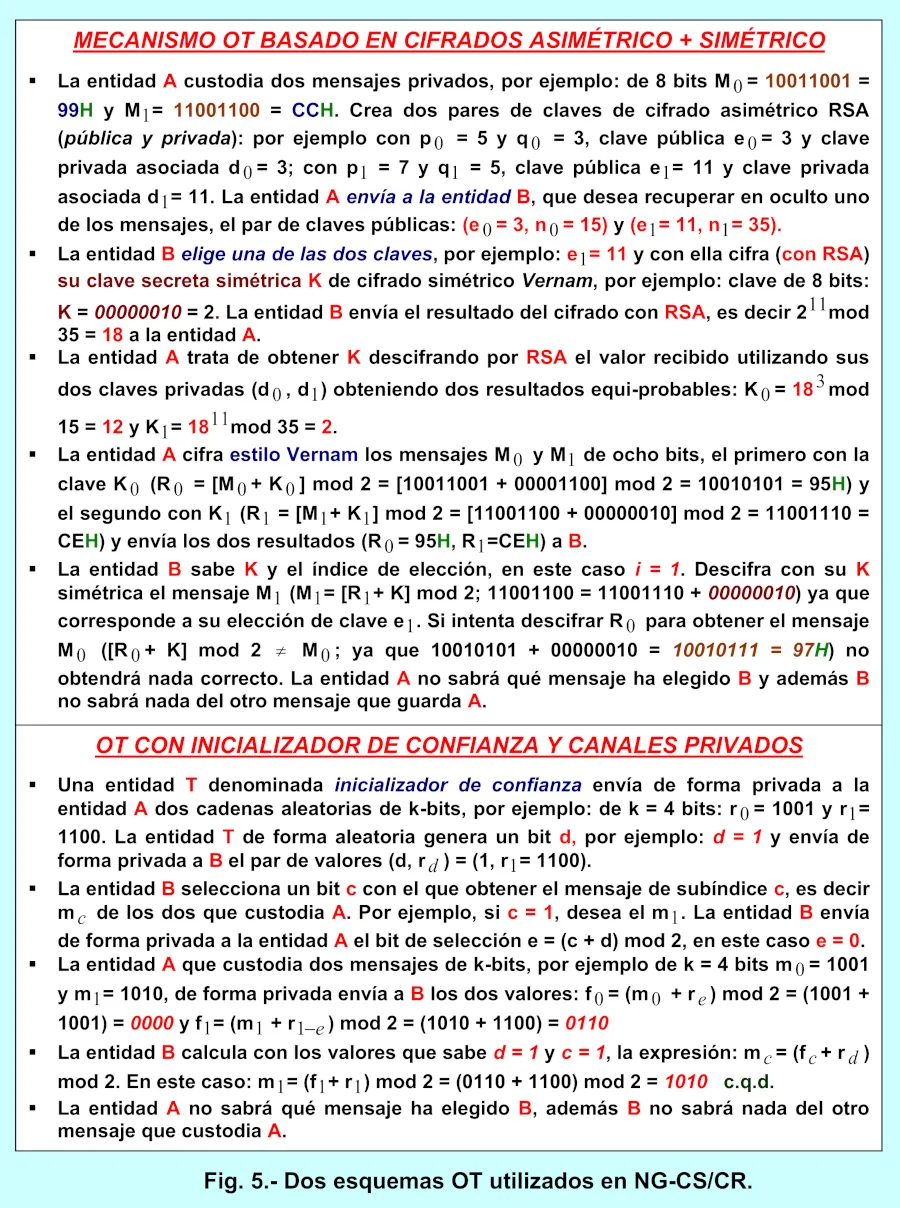
There are different ways to maliciously compromise and manipulate access control: “Triggers” modify behavior, for example, by using long arguments, flooding requests, etc. Trigger manipulation typically violates the expected properties of the input. “Reachability” is required to achieve the desired behavior, e.g., when a buffer overflow can only occur in the “password” field, reachability manipulation involves first providing a “login name.” “Enabling” manipulations improve control over behaviors/result limitations imposed by product behaviors; identification (aims to know the “identity/username/” of an entity using, for example, ZK technology); Extreme deception (deception technology, distortions, confusion/distraction/diffusion/illusions/chaos), maximum deterrence (with NG-Honey-Pots, NG-Honey-Nets, environments of fictitious profits and mirages of non-existent gains, mechanisms to instill fear, confusing, anesthetizing, displaying fictitious prizes), etc.). On the other hand, NG-CS/CR uses offensive safeguards: such as all kinds of strategies/tactics/techniques/procedures/mechanisms/functions/etc. from both Ethical Hacking and Malicious Hacking to monitor/detect/experiment/find in advance and cover/neutralize/nullify all possible holes/points/surfaces of weakness/vulnerabilities/etc. to cyberattack and infiltrate to carry out malicious actions. They are used for: surveillance/neutralization of cyber-attacks (NG-pentesting, NG-Red-Teams/Blue-Teams, NG-Sandboxing, NG-Bio-Hacking/Social-Engineering, NG-DMZs-for-testing/experimentation-and-total-observability, in-depth-audits/assessments, continuous-certifications, continuous/exercise/trials simulating TTPs (Tactics-Techniques-Procedures) of cyber-attackers, stress tests, nomadic-offensive malware of global active protection (DAIM style), etc.) for complete continuous surveillance with extreme anticipation. It includes next-generation processes and techniques: NG-end-to-end post-quantum multi-layer encryption, NG-steganography/watermarking, NG-subliminal channels, NG-digital signature, NG-hash, NG-firewall, NG-IAM (identity and access management), NG-vulnerability management/patches/updates/malware neutralization, NG-SIEM (security information and event management), NG-CASB (cloud/edge/network access security protection agent), OT (transcorded transfers), ZK (zero-knowledge), ZT (zero-trust), SPMC (Secure Multi-Party Encrypted Computing), extreme anonymity/mimicry, etc. Continuous certification in NG-CS/CR through accredited entities such as LEE Security, AENOR, etc., in standards such as ISO/IEC, is of vital importance. 27001 for cybersecurity, ISO/IEC 27701 for privacy, NIST SP 800-207 for ZT, ISO/IEC 42001 for managing AI, BS 25999 (British Standards Institute) withdrawn and replaced by ISO/IEC 22301 for business continuity, ISO/IEC 27036-3 for cybersecurity in the supply chain, ISO/IEC 31000 for risk management, ISO/IEC 27036-4 and ISO/IEC 27017 both for information security (cloud), ISO/IEC 27036-2 and 27036-3 for information security, LOPD-Spain/GDPR-Europe/HIPAA-USA for privacy, NIST-CSF for cybersecurity, CC (Common Criteria)/EAL (Evaluation-Assurance-Level) for the assessment-of-maturity-level.
IDENTIFICATION OF FUNCTIONS AND MATURITY LEVEL IN NG-CS/CR
Among the main functions of this NG-CS/CR symbiosis we can highlight:
(1) Identification/observability/intensive surveillance functions with extreme multifactorial analysis. Enables the early detection and neutralization of all possible cyber threat scenarios, known/unknown cyber attacks, and the identification and proactive action in all areas to improve procedures, processes, strategies, plans, policies, management practices, etc.
(2) Proactive defensive/offensive protection functions. This integrates the necessary safeguards/countermeasures to manage/neutralize/preemptively address cyber risks to all organizational assets, preventing the exploitation of vulnerabilities and critical points across all attack surfaces. It focuses on improving areas such as identity management, access control, data/metadata/information/intelligence security, platform cybersecurity, privacy, infrastructure cyber resilience, etc. Defensive measures include encryption/steganography/digital signatures/end-to-end watermarking, extreme factor authentication, access control, anonymization, etc. Offensive/experimental measures include NG-pentesting/NG-red-teams/NG-sandboxing/NG-blue-teams/audits/cyberattack tests, etc.
(3) Early detection and predictive functions. These enable faster response times for discovering all potential cyber threats and analyzing, neutralizing, or mitigating adverse cyber events that indicate possible cyberattack attempts. These functions are related to early response to cyber incidents and proactive recovery measures to neutralize all known and unknown cyber threats.
(4) Proactive response and extreme factoring functions. These provide proactive actions to take against potential cyber threat attempts. This includes the neutralization/management of cyber incidents/vulnerabilities, and their analysis/blocking.
(5) Preventive and proactive recovery functions. They identify in advance assets and operations that cyber-attacks attempted to impact, enabling the organization to resume normal operations.
(6) Governance functions (management, policies, practices, strategies, etc.). These functions are responsible for orchestrating, globally and automatically, all protection capabilities, actions, functions, etc., both defensive and offensive. This enables the proactive neutralization, freezing, blocking, and cancellation of all cyber risks (cybersecurity/cyber-resilience), including those related to assets, roles, responsibilities, supply chains, vulnerabilities, authorizations, regulatory compliance, and continuous standardization and accreditation, across all dimensions, levels, aspects, capabilities, and contexts.
The NG-CS/CR meets EAL-7+ (Evaluation Assurance Level 7-PLUS), which is the highest maturity level according to the CC/EAL standard. The maturity levels in the CC/EAL evaluation standard are, in ascending order: (1) EAL-1 (Functionally tested). (2) EAL-2 (Structurally tested). (3) EAL-3 (Methodically tested and verified). (4) EAL-4 (Methodically designed, tested, and reviewed). (5) EAL-5 (Semi-formally designed and tested). (6) EAL-6 (Semi-formally designed, verified, and tested). (7) EAL-7 (Formally tested and verified design). It is applicable to the development of cybersecurity Targets of Evaluation (ToEs) for applications in extremely high-risk situations.
ANALYSIS OF PROTECTION STRATEGIES. ZT/ZTA IN NG-CS/CR.
The NG-CS/CR analyzes and neutralizes all attempts at potential cyber threats/cyberattacks using a comprehensive set of strategies/TTPs/etc. The following phases of cyber-hacking, which operate in parallel, can be identified within them:
(1) Reconnaissance. The cyber-attacker (malicious or defensive) collects meta-data/data/information/intelligence about the entire set of assets (organizations, infrastructures, suppliers, clouds/clouds/networks, supply chains, entities) and their relationship to everything that is supposedly intended to be cyber-attacked.
(2) Initial compromise. The cyber attacker attempts to compromise suppliers/supply chains/etc., for example, their VPN accounts, phishing external technicians, accessing RMM (Remote Monitoring Management), etc. The NG-CS/CR will neutralize this and make the attacker believe they have succeeded
(3) Bridges to the organization. All loopholes/paths are exploited, such as permits, supplier access to access internal infrastructures (IT/OT/CPS/IoT, etc.).
(4) Lateral movement (cyber-metastasis). Once inside, cyber attackers attempt to move stealthily and laterally in a seemingly chaotic manner across the network of assets/systems, seeking valuable targets while leaving malicious agents hidden. Network infiltrations are not usually immediate, meaning the cyber attacker doesn't gain access to a critical/valuable server instantly. There is typically a gradual process, starting with initial access and slowly escalating privileges; this is similar to what is known as cyber-infection/cyber-sepsis. Generally, cyber attackers monitor the network, gaining more privileges by infiltrating more accounts of privileged users. This increase in privileges helps cyber attackers achieve their ultimate goals. One well-known technique used by cyber attackers is the hijacking of the Remote Desktop Protocol (RDP). This technique allows cyber attackers (malicious or defensive) to exploit, monitor, and neutralize a previously logged-in remote session without needing to steal user credentials (e.g., via phishing emails). Once the old RDP session resumes, the cyber attacker can move undetected, as monitoring mechanisms will only identify this as an authorized user logging in remotely. Network segmentation/microsegmentation is one strategy that allows for neutralizing and preventing lateral movement. The NG-CS/CR continuous action plan includes numerous control points to authorize access to critical resources. These control points, which protect sensitive resources, prevent cyber attackers stealthily lurking on the network from accessing them. Massive machine learning enables the early detection and neutralization of anomalous, illegal, or malicious behavior.
(5) Execution. This allows for malware activation, data exfiltration, and the simulation of destructive actions based on the objectives to be achieved. These objectives can range from accessing corporate mailboxes and exfiltrating sensitive data to compromising Active Directory/LDAP, inserting incorrect configurations, and tampering with updates. The theft of data, metadata, information, and intelligence is one of the malicious objectives of cyber attackers after compromising one or more networks, clouds, infrastructures, etc. Information theft can occur through previously established Command & Control (C&C) communication channels or newly established encrypted channels. Some malware can automatically steal data through a C&C channel using web protocols such as HTTP POST requests. Hostile actors use phishing emails to install Trojans on the victim's computers. Malware in emails can be embedded in attachments, links, malicious QR codes, and other malicious elements. This software acts as a file browser component and a theft module in the victim's computer's configuration folder. A browser lists these files on the victim's system; then, files with extensions specified by the C&C server are searched for. If found, the files are compressed into a file (pe-zip/arp/etc.) and encoded as files with a specific extension. These files are sent through a C&C channel via a POST request and extracted from the disk according to the command sent by the C&C server. A command can also be sent to delete all traces of the specified files from the victim's server. Data/metadata/information/intelligence theft can be completely neutralized in many ways, such as by reducing or neutralizing the available access paths to sensitive data. This includes enabling ports and communication channels only when necessary and leaving them disabled the rest of the time. It is also important that access to data, metadata, information, and intelligence be controlled and limited only to entities that legally require it. A more effective way to manage all the gaps in cybersecurity and cyber resilience that could cause data loss is to configure Next-Generation Data Loss Prevention (NG-DLP) mechanisms that monitor exit points such as emails, USB drives, endpoint devices, etc. Continuous and thorough audits of exchange servers and removable storage are key. The consequences of well-executed cyberattacks can be devastating for any infrastructure, entity, organization, etc. NG-CS/CR neutralizes any attempt to lose, modify, or render unavailable sensitive data, metadata, information, and intelligence, which could have a much greater impact than just lost revenue. The NG-CS/CR integrates NG-SIEM capable of detecting anomalous behavior in advance, correlating seemingly unrelated events that occur on the network, and executing preemptive neutralization procedures to contain/neutralize all attempts at cyber-attacks.
(6) Detection and Response. It allows for the early detection, neutralization/containment, and proactive response to all types of known and unknown cyber threats. The NG-CS/CR is based, from its inception, design, analysis, development, testing, etc., on the Zero Trust (ZT) paradigm, which remains in place throughout its evolution, adaptation, transformations, updates, etc., deploying a comprehensive, multidimensional Zero Trust Architecture (ZTA). A ZTA is a complete architecture based on ZT principles and designed to prevent, with extreme anticipation, all possible attempts to breach data/metadata/information/etc. and to impede all possible malicious lateral or internal movements. ZT is a paradigm focused on protecting all types of resources/assets with the unbreakable premise: “trust is never implicitly granted, but must be intensively/continuously monitored/evaluated; never trust, always verify/check.” Zero Threshold Architecture (ZTA) is an end-to-end approach for all resources, assets, data, etc., with identity (both human and non-human entities such as programs, devices, algorithms, machines, etc.), credentials, access management, operations, endpoints, hosting environments, clouds, exchange infrastructures, and so on. ZTA provides a set of elements (active and passive) designed to neutralize/override all types of cyberattack attempts, enabling access decisions on demand with least privilege across all kinds of information systems and services, thus preventing compromised networks. A ZTA can also be viewed as a plan that utilizes ZTA elements, relationships between components, workflow planning, and access policies. A ZTA structure is a physical and virtual network infrastructure and operational policies that ensure that this structure operates under a ZTA architecture plan. The NG-CS/CR is a complete body of unique/singular/self-orchestrated/holistic actions, that is, an indivisible whole that integrates self-governance with countless levels, governances/managements, dimensions, operations, processes, reviews, updates, etc.
FINAL ASPECTS.
NG-CS/CR integrates SecDevOps into all phases of its construction and operational lifecycle. Currently, it is regrettable and reckless negligence not to use SecDevOps/DevSecOps as a mandatory practice for the creation/development of all types of software, firmware, and hardware entities in each phase of the entity creation lifecycle, even before planning, discussions, design, analysis, integration, testing, delivery, deployment, etc. SecDevOps/DevSecOps represents an evolution in the way all types of software, firmware, and hardware entities are developed. Separate environments are used to apply NG-CS/CR measures, along with a separate QA (Quality Assurance) environment to test these measures. SecDevOps/DevSecOps integrates NG-CS/CR in an extremely agile way into all processes and mechanisms for creating software, firmware, and hardware resources, even well before planning and analysis. This prevents hidden vulnerabilities and exorbitant costs associated with resolving any deficiencies in the resources to be created (lifecycle under the strict presence and actions of NG-CS/CR). IoT (Internet of Things)/IoMT/IoIT ecosystems connect industrial (analog/digital) machines, household/hospital equipment, wearables, etc., to the internet, enabling individuals and organizations to interact. This connectivity offers numerous benefits, but also introduces increasingly complex and sophisticated cyber risks, as IoT devices are frequent targets of cyberattacks due to their more vulnerable mechanisms.
REFERENCES.
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo-2025.
- Areitio, J. “Exponential Empowerment of Cybersecurity in Protection, Cyber-Resilience, and Maturity Based on the MFE of Defense/Protection Components”. Conectronica Magazine. No. 265. February-March-2025.
- Areitio, J. “Early Cancellation by DAIM/MIAD of Singularities and Techniques Generating Insidious Cyberattacks”. Conectronica Magazine. No. 256. May-2023.
- Fuguet, G. “Hacking Home Devices II: POCs & Hacks Just for Fun”. Oxford-2025.
- Forbes, A. “A Foolproof Guide to Cloud Computing Vulnerabilities: The Effects of Security Threats on the Application Programming Interface”. Independently-published-2023.
- Thomas, GM “The Dark Art and Science of GPS Spoofing: Satellite Wars, Hijacking Signals and the Invisible Threat.” Ed. Publication-Independent-2025.
- Kathy, BH “Advanced Cybersecurity for Critical Infrastructure”. Montecito Hot Springs-2024.
- Infanti, E. “The Human Firewall: Bridging ux and Cybersecurity to Maximize Cyber Resilience.” Ed. Independent Publication-2025.
- Jajodia, S., Samarati, P. and Yung, M. “Encyclopedia of Cryptography, Security and Privacy”. Springer-2025.
Author: Prof. Dr. Javier Areitio Bertolín – Director of the Networks and Systems Research Group.



