In a 2009 article by M. Chertoff titled “Managing Identity: A Global Challenge, Notes from Homeland Security” (Secretary of the US Department of Homeland Security), it is stated that one of the greatest challenges of this new century concerns identity. According to a Gartner report, identity management gaps lead to trillions of dollars in losses each year, and this is increasing with new technologies such as social media and cloud computing. According to a report by Forrester Research, Inc., the global identity management market was worth $3.8 trillion at the end of 2009, was projected to grow by 13% between 2010 and 2013, and exceed $12 trillion by 2014, with 57% for software and 43% for services. Furthermore, by the end of 2013, the EMEA region was expected to dominate the global market with 40% of the total. The role of identity management is to: manage credentials, manage user access to technology assets (hardware, software, and services), reduce usernames/passwords, link usernames/passwords to real people, enable a defined and repeatable process for requesting and granting access to systems, allow planned access reviews, enable consistency in granting access to systems, automate the administrative burden associated with granting access to systems, give people the right information at the right time to do their jobs, etc.
Identity management in an organization integrates numerous functionalities such as the identification of entities (people, services, etc.), multi-factor authentication, authorization, tracking access to services/resources, and the provisioning/deprovisioning of identity (for various types of user accounts, such as end users, application administrators, IT administrators, supervisors, developers, account administrators, etc.). Privileges are what an entity can do (read, execute, write, etc.). Roles refer to who the entity is (super-administrator, guest, HR manager, employee, outsourced personnel, etc.) and can be used for policy-based privileges, where both concepts are complementary for authorization. Some of the key questions that should be considered in this context are: How do people use the services they claim to have? Are they members of the company, and if so, what role? Do they have the minimum permissions necessary to act according to the established business model? How is their privacy protected?.
Characterization and evolution of identity management
Identity management, also called IAM or simply IdM (Identity Management), can be defined from many different perspectives:
(1) Identity management is an architectural framework for maintaining a comprehensive set of identity information for individuals across multiple business contexts. Identity management unifies disparate identity data to improve data consistency, data accuracy, and system and data security in an efficient manner. Identity management requires the integration of technologies such as directories, single sign-on (SSO), user provisioning (reducing help desk costs), and delegated administration, as well as coordination with business processes surrounding the management of user information, access rights, and related policies.
 2) Identity management encompasses a variety of functionalities (a multifunctional suite) that handle: user accounts, access rights, passwords, authentication, authorization, etc. Identity Management (IdM) is responsible for managing identities (creating, modifying, or deleting; password synchronization; self-service password resets; workflow and delegation), access control (role-based access control, policy-based access control, ESSO (Enterprise Single Sign-On), federation, RSSO (Reduced Single Sign-On), WSSO (Web Single Sign-On)), directory services (directories are a critical infrastructure component containing identity repositories, metadata replication/synchronization services, and directory virtualization), separation of duties (critical for internal controls; implements individual verification; reduces the danger/risk of individual actions; aids auditing/compliance), and auditing/compliance. Identity management encompasses three paradigms: (i) Pure identity. This focuses solely on identity, handling identity management: creation, deletion, and updating of identities. Note that access rights are not defined. (ii) User access. This focuses on the use of digital identity, which is typically unique. A unique identity simplifies monitoring and verification. This includes authentication, authorization, and logging/auditing/reporting. (iii) Services. This focuses on the resources used to deploy services; examples include servers, applications, network devices, VPNs, etc. It allows for a more comprehensive and broader view, typically from the perspective of the audit/compliance team. A layered structure could be represented, with employees occupying the innermost layer, surrounded by another layer of user accounts, and in turn surrounded by an outermost layer containing applications.
2) Identity management encompasses a variety of functionalities (a multifunctional suite) that handle: user accounts, access rights, passwords, authentication, authorization, etc. Identity Management (IdM) is responsible for managing identities (creating, modifying, or deleting; password synchronization; self-service password resets; workflow and delegation), access control (role-based access control, policy-based access control, ESSO (Enterprise Single Sign-On), federation, RSSO (Reduced Single Sign-On), WSSO (Web Single Sign-On)), directory services (directories are a critical infrastructure component containing identity repositories, metadata replication/synchronization services, and directory virtualization), separation of duties (critical for internal controls; implements individual verification; reduces the danger/risk of individual actions; aids auditing/compliance), and auditing/compliance. Identity management encompasses three paradigms: (i) Pure identity. This focuses solely on identity, handling identity management: creation, deletion, and updating of identities. Note that access rights are not defined. (ii) User access. This focuses on the use of digital identity, which is typically unique. A unique identity simplifies monitoring and verification. This includes authentication, authorization, and logging/auditing/reporting. (iii) Services. This focuses on the resources used to deploy services; examples include servers, applications, network devices, VPNs, etc. It allows for a more comprehensive and broader view, typically from the perspective of the audit/compliance team. A layered structure could be represented, with employees occupying the innermost layer, surrounded by another layer of user accounts, and in turn surrounded by an outermost layer containing applications.
(3) According to the Burton Group, Identity Management (IdM) is defined as the set of business processes and infrastructure that support the creation, maintenance, and use of digital identities. The core functions of IdM are identity establishment (proving and investigating identity) and user authentication and authorization. The supporting infrastructure for these core functions includes directory services, Reverse/SSO, role- and privilege-based authorization automation, and identity federation.
(4) According to The Open Group, Identity Management (IAM) is a convergence of technologies and business processes; therefore, there is no single approach to identity management because the strategy must reflect the specific requirements within each organization's business and technological context.
(5) IAM includes various factors such as: (i) The processes responsible for creating an electronic identity for individuals. (ii) The relationships of individuals with the institution. (iii) The declaration of these electronic identities and the relationships that allow access to resources. (iv) The technology to support the secure and efficient operation of IAM services. In other words, an identity management infrastructure is a set of technologies and policies that allows networked computing systems to determine who has access to them, what resources a person is authorized to access, while at all times protecting the privacy of individuals and access to confidential information. IDaaS (Identity as a Service) is essentially identity management in the cloud, outside of the applications (and even the providers) that use them. If an analysis is performed on the evolution of IAM, several stages of maturity can be identified, which, from oldest to most recent, are: (a) Stage 1. The application maintains unique identity information and credentials for each user. (b) Stage 2. Credentials are centralized, for example with Kerberos, LDAP/Active Directory, but applications maintain all user identity information. (c) Stage 3. Core credentials and identity information are centralized, and the application only maintains application-specific user data.

Technologies Integrated into an IAM System:
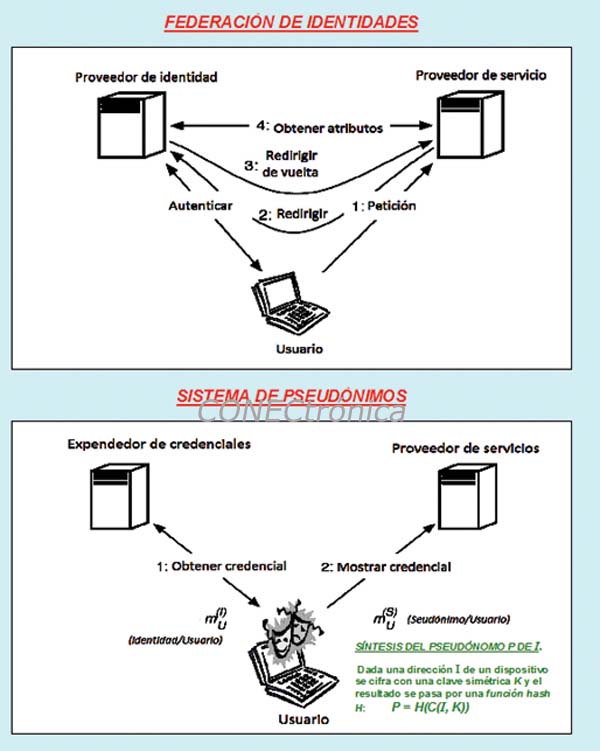
An IAM system combines several types of technologies: (1) To establish an identity data infrastructure. This includes the functionalities that form the identity information layer: directories, meta-directories, and virtual directories. (2) To manage accounts and privileges. This includes the functionalities that manage user accounts, attributes, and credentials with provisioning/deprovisioning, role management, password management, and privileged user management. Self-service and delegated administration functionalities are also integrated. (3) To control access to ICT resources. This coordinates user access to multiple applications using ESSO (Enterprise Single Sign-On), WSSO (Web Single Sign-On), and federation. Rights management is also included. (4) To audit access and administrative activities. Organizations need identity auditing functionalities to demonstrate that access controls and account administration are performed according to policy. These functionalities combine and correlate activities and events across the entire identity infrastructure, as well as privilege attestation to certify that the privileges associated with a user are correct. Role management is also included, which serves to codify policies and validate their applications. (5) For robust, risk-based authentication, using smart cards, digital certificates, biometrics, etc.
Final Considerations
Our research group has been working for over twenty years in identity and user management, a constantly evolving field where we have addressed the development and synthesis of tools, as well as the analysis and evaluation of systems and practical deployments, and the performance of scenario tests aimed at minimizing increasingly sophisticated attacks such as identity/session hijacking and other forms of theft.
This article is part of the activities carried out within the LEFIS-Thematic Network.
Bibliography
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2011.
Areitio, J. and Areitio, A. “New approaches in the analysis of firewall technology, an essential component for network security”. Conectrónica Magazine. No. 122. November 2008.
Paschoud, J. “Access and Identity Management: Controlling Access to Online Information”. Neal-Schuman Publishers. 2010.
Takahashi, K. “Identity Management: Concepts, Technologies and Systems”. Artech House Publishers. 2011.
Todorov, D. “Mechanics of User Identification and Authentication: Fundamentals of Identity Management”. Auerbach Publications. 2007.
Buecker, A., Annas, A., Faustini, A. and Sanui, T. “Identity Management Advanced Design for IBM Tivoli Identity Manager”. IBM.Com/Redbooks. 2006.
Benantar, M. “Access Control Systems: Security, Identity Management and Trust Models.” Springer. 2005.
Williamsar, G., Yip, D., Sharoni, I. and Spaulding, K. "Identity Management. A Primer." McPress. 2009.
Scheidel, J. “Designing an IAM Framework with Oracle Identity and Access Management Suite.” McGraw-Hill. Osborne Media. 2010.
Windley, PJ “Digital Identity”. O'Reilly Media, Inc. 2005.
Birch, D. “Digital Identity Management: Technological, Business and Social Implications.” Ashgate Publishing. 2007.
Santuka, V., Bauga, P. and Carroll, BJ “AAA Identity Management Security”. Cisco Press. 2010.
Authors:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto.
Prof. Dr. Ana Areitio Bertolín – E.Mail:
Applied Computing Laboratory. University of the Basque Country (UPV/EHU)



