Privacy, Security. Private External Information.
Information privacy is the ability of individuals and institutions to exercise a substantial degree of control over the collection, use, and disclosure of their personal information. In other words, it is the ability of individuals and institutions to control the terms under which their personal information is acquired and used. For example, controlling a company's reputation on high-performance search engines like Google, Yahoo, etc. Compliance policies such as LOPS/RMS exist. Information security, on the other hand, is the continuous and iterative process of protecting data and resources from unauthorized access, use, disclosure, destruction, modification, or disruption. Privacy enables individuals/institutions to control their personal/institutional information, while security enables the process of protecting any information or resource. Therefore, security can help establish privacy (but it is not privacy itself), and vice versa. Some commonly used privacy tools include cookie managers, anonymizers (Tor is an internet anonymity system that allows users to send messages that cannot be tracked, for example, while browsing the web, chatting, using P2P, etc. It currently supports a GUI in addition to the older CLI), encryption and steganography tools, disk wiping utilities, P3P user agents, ZKIP/CS technologies, email anonymity remailers, secure tunnels, anonymous banking, antivirus software with features for removing tracking cookies, Trojans, and spyware, etc. Private exo-information is the information derived from the data we generate during our information-seeking activities. Personal information is either information we unconsciously release—information whose release we cannot control, such as tracking cookies used in web browsing, webcams, mobile phone GPS, etc.—or information we are coerced into releasing, such as the terms and conditions imposed upon us to access a web service, social network, operating system, or any resource in general. Other examples of private external information include the tones generated when pressing keys on a telephone or keypad to open a door; these sounds reveal the number being called or the access code. Other examples include the social security number on some driver's licenses when used as an identifier, and unshredded credit cards found in some trash cans that provide a link between an individual's name and address.

Security Objectives and Their Interactions
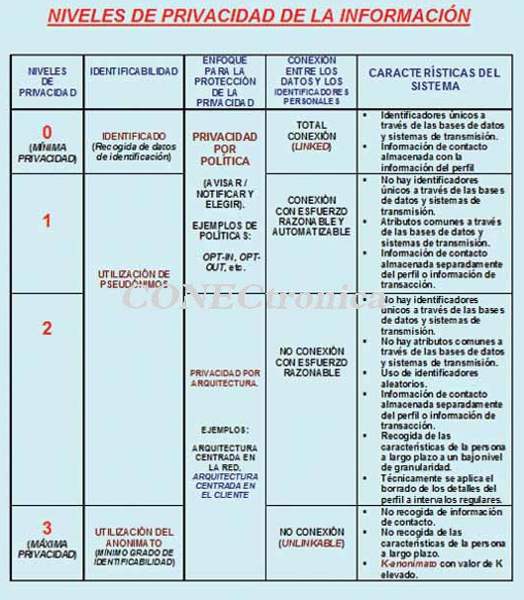
Among the main objectives we can identify in the context of security and privacy are: (1) Privacy. In its two facets of data confidentiality and participant anonymity. (2) Data integrity and participant authentication. (3) Accountability. In its two facets of resource availability and responsibility for the actions performed by participants, monitoring their operations with logging and audit logs; sometimes non-repudiation is also considered here, requiring that no one deny an action performed, such as sending or receiving. Data confidentiality refers to preventing unauthorized participants (users) from discovering the content/meaning of messages (in the context of communications) and/or locations (in the context of storage/repositories) and executions (executing without being able to read). Robust data encryption (based on symmetric, block, or stream cryptography, asymmetric, or quantum cryptography), data obfuscation (based on steganography), and restricted read access to data (based on access control, for example, role-based access in operating systems and applications) are used. Security policies allow for regulating/controlling who is allowed to read, write, change, or execute which data according to roles and privileges and under what conditions (using exceptions to the rules).
Anonymity allows a user (or participant) to access resources or services without revealing their identity, ensuring that the specific service or resource being accessed remains unknown and that senders and receivers cannot be correlated. This is achieved through the use of pseudonyms, anonymity networks (such as MIXes), proxy servers, and protocols like OT/CS/ZKIP. The goal is to conceal who is communicating with whom or reading what data. Data integrity allows us to know if unauthorized participants (users) are manipulating the data in any way (creation, deletion, modification). This is achieved through the use of conventional, blind digital signatures/multi-signatures, hash functions, and access restrictions (write, execute, etc.) based on access control. Authentication enables the determination (verification and proof) of the participants' (users') identities. If mutual authentication were currently in use, phishing would be more difficult, since both the client and the visited website would have to authenticate each other, not just the client as is currently the case (simple authentication, even if multi-factor). Authentication uses passwords (what you know—it's best to use virtual keyboards to protect against keyloggers—or what you recognize—visual passwords); shared knowledge. With ZKIP technology, this knowledge is not shared, so your password or bank account information is not leaked. Other methods include biometrics (identifying your identity, whether behavioral or physiological), PKI (Public Key Infrastructure), location (GPS, IP-L3 and MAC-L2 addresses, etc.), timestamps (time and date), real-time video with irrefutable proof of the other party's live time and date, and so on. This allows you to know who is using a system or sending a message. Availability aims to prevent potential unauthorized service disruptions. Some examples are CPU blocking of resources (printers, servers, etc.) by means of Java applets and network flooding (for example with emails) and applications.
 Responsibility aims to prevent, for example, the sender and/or receiver of information from denying having sent or received information (achieved through digital signatures and proof of communication/active agreement with a TTP), unauthorized access to databases, or the execution of critical applications, such as in the industrial sector in the context of PLCs/Programmable Logic Controllers and SCADA systems, etc. Security objectives are not always independent; anonymity weakens responsibility. Confidentiality weakens responsibility, and access control is based on identification/authentication and authorization (assigning permissions, privileges, roles, and exceptions). In our information and knowledge society, security must be multi-level and multilateral, so that each participant: (i) Has their own security needs. (ii) Can formulate their own problems. (iii) Exists conflicts that must be resolved and addressed. Some useful considerations in this area are: (a) Security is a continuous and iterative process with multiple levels of protection. (b) Security cannot be added; insecurity must be reduced to a level commensurate with the risk the organization assumes. (c) A system, network, or resource is never 100% secure. (d) Threats and the value of what is to be protected must be considered.
Responsibility aims to prevent, for example, the sender and/or receiver of information from denying having sent or received information (achieved through digital signatures and proof of communication/active agreement with a TTP), unauthorized access to databases, or the execution of critical applications, such as in the industrial sector in the context of PLCs/Programmable Logic Controllers and SCADA systems, etc. Security objectives are not always independent; anonymity weakens responsibility. Confidentiality weakens responsibility, and access control is based on identification/authentication and authorization (assigning permissions, privileges, roles, and exceptions). In our information and knowledge society, security must be multi-level and multilateral, so that each participant: (i) Has their own security needs. (ii) Can formulate their own problems. (iii) Exists conflicts that must be resolved and addressed. Some useful considerations in this area are: (a) Security is a continuous and iterative process with multiple levels of protection. (b) Security cannot be added; insecurity must be reduced to a level commensurate with the risk the organization assumes. (c) A system, network, or resource is never 100% secure. (d) Threats and the value of what is to be protected must be considered.
The principle of adequate protection states that network/computing resources should only be protected until they lose their value and should be protected to a degree consistent with that value. When protecting an organization's entities, in addition to people, the following are also considered: (i) Data. Information/knowledge/wisdom stored, in transit across networks, and running on physical and virtual computing and network systems. (ii) Resources. The computing devices themselves (PCs/Macs, tablets, PDAs, smartphones, RFIDs, PLCs, embedded electronics, etc.), transmission devices (routers, switches, UTMs, Wi-Fi access points, etc.), and storage devices (databases, buffers, caches). (iii) Reputation. Your organization's risk undermines its credibility and reputation ranking on high-performance search engines like Google, Yahoo, etc. If your organization does not manage its risk, it will be liable for intrusions or cybercrimes. The reasons for insecurity are varied: (1) Sharing key resources on social networks. (2) Complexity; it is increasingly difficult to see what is happening due to virtualization, cloud computing, complex protocols, etc. (3) Difficulty in defining boundaries. Increased mobile communications, ambient intelligence (AI), etc. With mobile communications, it is very difficult to establish robust perimeter defenses. (4) The existence of an increasing number of attack points: internal (employees, auditors, adversaries, spies, guests, subcontractors with SLAs, terrorists, etc.) and external (employees, adversaries, service/identity/security providers, spies, terrorists, competitors, the cloud, etc.). (5) Anonymity of attackers and encryption/steganography of their communications. (6) The existence of multiple routes between any two given nodes in a network.
Identification of controls.
Some of the relevant controls that must be in place are: (1) Inventory of physical components and software. It is currently essential to deploy automated asset search and inventory tools to build a real-time record of all systems connected to the corporate network, indicating their GPS location, network IP address, hardware MAC address, machine names (their hardware type: CPU-RAM, operating system name and version), the purpose of each system, the person responsible for each device, the department associated with each device, the company that provided the hardware, etc. To evaluate the effectiveness of the inventory tool, it is necessary to periodically connect and disconnect various new systems and measure the delay before each device is enabled or disabled in the inventory, along with the date and time of implementation or removal. It is also key to have automated tools that can search for and inventory all the software scattered across the organization's devices, including endpoints (servers, user computers), hard drives, virtual drives, workstations, laptop PCs/MACs, mobile devices (PDAs/iPhones/iPADs), smartphones/tablets, the cloud, etc.
The types, versions, and patch levels of operating systems, applications, programs, etc., will be collected. To evaluate the effectiveness of the automated inventory tool, various software, updates, and packages will be periodically installed/uninstalled, and the software inventory lag will be measured to indicate the changes made. These operations can be performed on control machines to avoid negatively impacting production systems. (2) Secure hardware and software configuration. This is necessary after thoroughly analyzing, approving, and documenting the security configurations of all system images and deploying them. They must correspond to the appropriate versions of the operating systems, plug-ins, and installed applications. Any deviation from the established value or subsequent updates must be documented and approved in the change management system. Periodically, assessment programs must be run that vary the configuration of some systems to measure the number that are or are not correctly configured according to the established configuration policies or guidelines. (3) Perimeter defense protection, defense in depth. Organizations should block communications from known/likely malicious IP addresses (blacklists/graylists) or restrict access to trusted sites (whitelists). They should also define network architectures that separate internal systems from systems connected to the DMZ (Demilitarized Zone) and systems on the extranet or the internet. Organizations should implement internal network segmentation schemes (e.g., based on VLANs with switches and IP subnets) to limit traffic to only those services necessary for the organization's use across the internal network (or intranet). Mutual and two-factor authentication should be required for all remote login access, such as VPN/SSL-TLS/SSHv2.
It is necessary to periodically check whether IP packets from blocked source addresses (blacklisted with malicious and unroutable addresses) manage to penetrate the perimeter of our internal network. For example, an intranet IP address cannot be the source IP address of a PDU originating from the internet. Other key controls include: (i) Network management protection control; for example, a QoS study can detect potential intrusion attempts in advance, even with encrypted traffic. (ii) Penetration testing/ethical hacking. This allows us to assess our resistance to potential attacks. Sometimes, penetration testing audits reveal the existence of illegal gambling programs installed on servers of institutions that provide critical services. (iii) Security incident response. An automated operating procedure must be in place for incidents. (iv) Data recovery. This includes regularly tested and operational procedures for backups and restoration to the state prior to the problem. (v) System and facility recovery in case of disasters. This can be achieved using hot and cold sites in geographically separate locations. Mandatory if the organization is publicly traded. (vi) Awareness plans supported by training and monitoring technology to build skills, reinforce the security culture, and address identified gaps in conduct. These employee support tools monitor non-compliance and errors (accidental and intentional) and allow the employee's workstation to be quarantined until they comply with the established policy. While quarantined, they cannot intentionally or unconsciously harm others, for example, by spreading worms acquired by plugging an infected USB drive into their workstation. Awareness without monitoring and without fostering responsibility is useless. (vii) Maintenance, monitoring, and analysis of audit logs, including those between administrators. (viii) Control of privilege usage, i.e., controlled use of administrative privileges, logging, analysis, and auditing of logs. Dumpsec is a tool that allows you to review users and security policies in Windows environments. It provides detailed information from domain controllers about policies, users, groups, rights, and services. It can be run from the command line on any system with domain administrator rights. (viii) Test password strength using password crackers such as JTR (John The Ripper) for Windows and Unix; see http://www.openwall.com/john. (ix) Controlled access based on individual needs. (x) Account control and monitoring. (xi) Protection against malware/spyware. (xii) Mobile device control. (xiii) Data loss prevention (DLP), for example, by encrypting all information that may be transmitted over the network, USB drives, CDs/DVDs, removable disks, or electromagnetic emissions using encryption-based Soft-Tempest.
Final Considerations
Our research group has been working for over twenty years in the field of security and privacy protection in various types of network environments, from (W)BodyAN to (W)WideAN, including (W)PersonalAN, (W)CampusAN, (W)LocalAN, (W)MetropolitanAN, (W)RuralAN, etc.
This article is part of the activities carried out within the LEFIS-APTICE project (funded by Socrates, European Commission).
Bibliography
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2010.
- Areitio, J. “New approaches in the analysis of systems for detecting, preventing and managing attacks and intrusions”. Conectrónica Magazine. No. 123. January 2009.
- Fry, C. and Nystrom, M. “Security Monitoring. Proven Methods for Incident Detection on Enterprise Networks”. O'Reilly. 2009.
- Norman, TL “Risk Analysis and Security Countermeasure Selection”. CRC Press. 2009.
Author: Prof. Dr. Javier Areitio Bertolín – Professor at the Faculty of Engineering. Director of the Networks and Systems Research Group. University of Deusto.




