 Finally, suitable asymmetric cryptographic mechanisms are specified to improve their security-privacy behavior in critical infrastructure applications such as smart-metering and smartphone MANETs, without infrastructure, for deployments in situations of mobile communication saturation and disaster cases where there are no 2G/2.5G/3G/4G base stations and antennas (such as GSM/GPRS/UMTS/WCDMA/HSPDA/LTE, etc.)
Finally, suitable asymmetric cryptographic mechanisms are specified to improve their security-privacy behavior in critical infrastructure applications such as smart-metering and smartphone MANETs, without infrastructure, for deployments in situations of mobile communication saturation and disaster cases where there are no 2G/2.5G/3G/4G base stations and antennas (such as GSM/GPRS/UMTS/WCDMA/HSPDA/LTE, etc.)
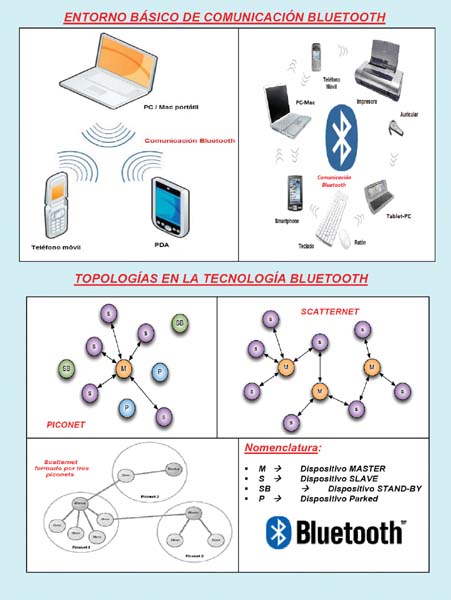
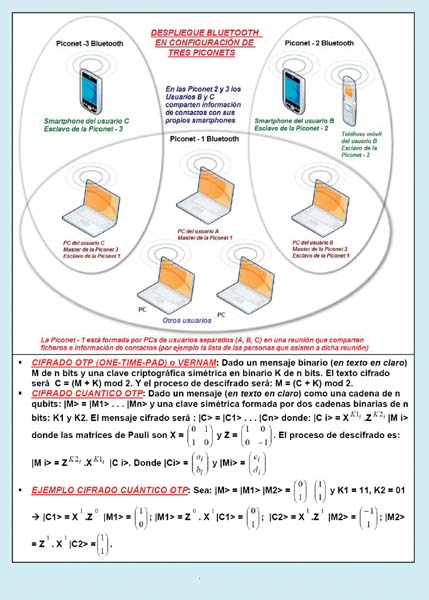
Bluetooth allows multiple devices (PCs/Macs (laptops, desktops, and palmtops), tablet PCs, mobile phones and smartphones, GPS receivers, gaming devices, wireless headphones, printers, smart card and barcode readers, cameras, digital pens, DVD/Blu-ray drives, coffee makers, mice, keyboards, PDAs, iPads/iPods, sensors in healthcare facilities, hardware modules for embedded electronics, etc.) to establish either ad-hoc networks (Piconets) or more complex networks (Scatternets). Ad-hoc networks are the most common, providing easy connection between mobile devices in the same physical area (e.g., the same room) without the need for infrastructure devices such as fixed access points. A Bluetooth client is simply a device with radio hardware and Bluetooth software that incorporates the Bluetooth protocol stack and interfaces. Bluetooth allows the deployment of mobile mesh or ad-hoc/MANET networks with smartphones, even when base stations, cell towers, and Wi-Fi access points are inoperative due to saturation or natural or intentional disasters. Each Bluetooth unit has a 48-bit Ethernet address. Authentication between two Bluetooth units requires entering a common PIN on each unit. A Piconet has one master and up to seven slaves. Communication is protected with a stream cipher using a link key. However, the link key can be the unit key of one of the parties in the communication. If unit C connects to unit A and uses unit A's unit key, then C can eavesdrop on the communication between B and A if that communication also uses A's unit key.
Bluetooth Protocol Stack:
The Bluetooth (BT) specification provides a separation of responsibilities for performing the functions of the protocol stack, whose layers, from bottom to top, are:
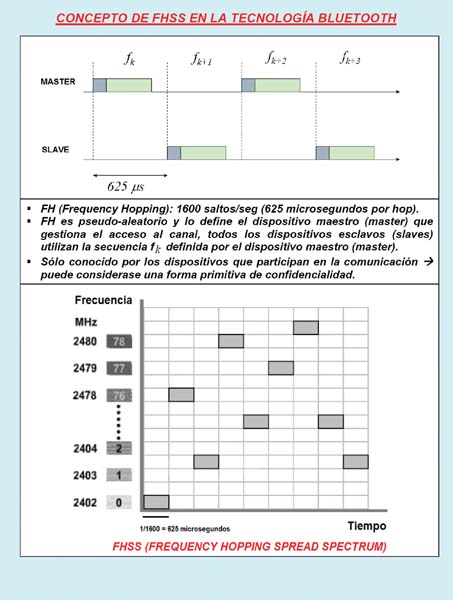
(1) Host Controller, or simply controller. It is responsible for the lowest levels. From bottom to top, these are identified as the radio layer, above the baseband layer, which provides radio access to the upper layers, and above that, the link manager layer, where the Link Manager Protocol (LMP) is located. The LMP manages connections and is used to control the radio link between two devices. It is implemented in the controller. The baseband layer operates in the ISM band at 2.4 GHz with 79 channels, each 1 MHz wide, and 1600 hops per second. It uses FSK (Frequency Shift Keying) modulation and DQPSK (Differential Quadrature Phase Shift Keying) for higher data rates. The medium access is FHSS and TDMA, using frequency hopping with 1600 hops/sec (conventional or adaptive frequency hopping is used to prevent interference) and time-division duplex for sending/receiving separation. The network topology uses the basic unit called a piconet, and overlapping piconets form a scatternet. The maximum distance is 100 meters, and even 300 meters in open spaces, or more with suitable antennas and amplifiers. Data rates depend on the version: up to version 1.2, 1 Mbps; and versions 2.0 and higher, at least 3 Mbps.
(2) Host. It is responsible for higher-level protocols such as:
(i) L2CAP (Logical Link Control and Adaptation Protocol). It is used to multiplex several logical connections between two devices using different high-level protocols. It provides packet segmentation and reassembly. In basic mode, it provides packets with a configurable payload of up to 64 KB, with 672 bytes as the default MTU and 48 bytes as the minimum supported mandatory MTU. It can be configured in retransmission and flow control modes for isochronous data (voice) or reliable data per channel, performing retransmissions and CRC checks. Two additional modes are: ERTM (Enhanced ReTransmission Mode), an enhanced version of the original retransmission mode, which provides a reliable L2CAP channel; and SM (Streaming Mode), a very simple mode without retransmission or flow control, which provides an unreliable L2CAP channel. Only L2CAP channels configured in ERTM or SM can operate over AMP logical links.
(ii) SDP (Service Discovery Protocol). This protocol allows Bluetooth devices to search for services they provide. It enables a device to discover services supported by other devices and their associated parameters. For example, when a mobile phone connects to a Bluetooth headset, SDP is used to determine which Bluetooth profiles the headset supports (headset profile, hands-free profile, A2DP (Audio Distribution Profile), etc.), and the protocol configures what is necessary to connect them. Each service is identified by a UUID (Universally Unique Identifier), with official services (Bluetooth profiles) assigned a shortened form of the UUID (16 bits instead of the full 128 bits).
 (3) Applications. This section includes management, telephony, vCal/vCard, audio, data, and other applications. The OBEX (Object EXchange) protocol is used to exchange objects such as calendar entries, business cards, and data files between devices using a client-server model. The RFCOMM (Radio Frequency COMMunications) protocol is used to replace the wired connection, creating a virtual serial data stream. RFCOMM provides binary data transport and emulates EIA-232 (formerly RS-232) over the Bluetooth baseband layer. RFCOMM provides the user with a simple, reliable data stream similar to the TCP transport protocol. It is used directly by many telephony-related applications as a carrier for AT commands (used to control modems) and also serves as a transport layer for OBEX over Bluetooth. Many Bluetooth applications utilize RFCOMM due to its widespread support and publicly available API in most operating systems. Applications that use a serial port for communication can quickly utilize RFCOMM. The Bluetooth Network Encapsulation Protocol (BNEP) is used to transfer data from another protocol stack using an L2CAP channel. Its primary function is the transmission of IP packets in the Personal Area Networking Profile (PANP). The Audio/Visual Control Transport Protocol (AVCTP) is used by the remote control profile to transfer AV/C commands over an L2CAP channel. The music control buttons on a Bluetooth stereo headset use this protocol to control the music player.
(3) Applications. This section includes management, telephony, vCal/vCard, audio, data, and other applications. The OBEX (Object EXchange) protocol is used to exchange objects such as calendar entries, business cards, and data files between devices using a client-server model. The RFCOMM (Radio Frequency COMMunications) protocol is used to replace the wired connection, creating a virtual serial data stream. RFCOMM provides binary data transport and emulates EIA-232 (formerly RS-232) over the Bluetooth baseband layer. RFCOMM provides the user with a simple, reliable data stream similar to the TCP transport protocol. It is used directly by many telephony-related applications as a carrier for AT commands (used to control modems) and also serves as a transport layer for OBEX over Bluetooth. Many Bluetooth applications utilize RFCOMM due to its widespread support and publicly available API in most operating systems. Applications that use a serial port for communication can quickly utilize RFCOMM. The Bluetooth Network Encapsulation Protocol (BNEP) is used to transfer data from another protocol stack using an L2CAP channel. Its primary function is the transmission of IP packets in the Personal Area Networking Profile (PANP). The Audio/Visual Control Transport Protocol (AVCTP) is used by the remote control profile to transfer AV/C commands over an L2CAP channel. The music control buttons on a Bluetooth stereo headset use this protocol to control the music player.
The host functions are performed by a computing device such as a laptop, smartphone, or desktop PC. The host controller functions are performed by an integrated or external Bluetooth dongle (e.g., via USB). The host and host controller exchange information using the Host Controller Interface (HCI), which is a command-line interface for accessing baseband functions. Above this, HCI is implemented in software. HCI enables standardized communication between the host stack (e.g., a PC or a mobile phone operating system like Android) and the controller (the Bluetooth chip or integrated circuit). This standard allows the host stack or the controller integrated circuit to be interchanged with minimal adaptation. Several HCI transport layer standards exist, each using a different hardware interface to transfer the same commands, events, and data packets. The most common are USB (in PCs) and UART/miniUSB (in mobile phones and PDAs). In Bluetooth-only devices (e.g., Bluetooth headsets), the host and controller stacks can be implemented on the same microprocessor. In this case, the HCI is optional, although it is often implemented as an internal software interface. In many cases, the host and host controller functions are integrated into a single device (an example being Bluetooth headsets).
Key security features
of BT include the ability to establish WPANs (Wireless Personal Area Networks). BT connectivity allows for the deployment of ad-hoc networks in a star cluster called a piconet (master and slave devices). A BT access point can also be used. Up to seven active and 255 inactive slave devices can be deployed on a single connection. It is also possible to form a scatternet by sharing common slave devices or assigning different roles to a single device across two piconets. Devices typically exchange data at 723 Kbps, operating in the unlicensed 2.45 GHz radio band. The range of a BT device is classified into one of three classes according to power level: (i) Class 1: High power of 100 milliwatts and a range of 100 meters. (ii) Class 2: Medium power of 2.5 milliwatts and a range of 10 meters. (iii) Class 3: Low power of 1 milliwatt and a range of 10 meters. Note that eavesdropping can be carried out from very long distances, even via satellite, if sufficient power and antennas are available. BT's Generic Access Profile (GAP) security architecture supports: (1) Three security services: (i) Authentication. Verifies the identity of communicating devices. This is commonly done using a PIN. (ii) Authorization. Enables resource control, checking whether a device is permitted to use a service. (iii) Confidentiality using encryption. Protects exchanged information so that it cannot be understood except by the designated recipient. (2) Three security modes: (i) Mode 1 (Not secure). No security measures are included: authentication, authorization, encryption. Both devices and connections are vulnerable to attack. (ii) Mode 2 (Service-level security). Security measures are not stringent. Security procedures are applied when a service request is made. Links can be established insecurely. (iii) Mode 3 (link-level security). Security measures are strict and begin when the link is established. There is a difference between security modes 2 and 3. In mode 3, three phases are defined: (a) Initialization phase: Building trust and exchanging cryptographic keys. (b) Meeting phase: Authenticity is verified. (c) Communication phase: Data is exchanged securely. (3) Two security levels for devices: (i) Trusted. (ii) Untrusted. (4) Three security levels for services: (i) Accessible to all devices: No PIN or password required. (ii) Authentication only: Password required. (iii) Authentication and authorization: Password required followed by an authorization procedure. (5) Key generation, encryption, pseudo-random numbers, etc. Some BT security weaknesses are: (1) Vulnerabilities and poor performance of the E0 and E1 algorithms based on SAFER+. (2) Unit key. (3) PIN and initialization key. (3) Vulnerabilities in the implementation of the algorithms. As possible countermeasures: (a) Use random and very long PINs and the AES-256 algorithm. (b) Do not use a KA unit key as a link key; instead, use a KAB combination key. (c) Use security mode 2, or better yet, mode 3, and simultaneously activate all three functionalities: authentication, authorization, and encryption. The three main types of Bluetooth attacks are: Bluejacking (sending unsolicited messages), Bluebugging (attacking a Bluetooth mobile device and causing it to dial), and Bluesnarfing (extracting data objects from the victim, such as their calendar, address book, etc.).
 Versions of Bluetooth Technology:
Versions of Bluetooth Technology:
In 1994, Ericsson Mobile Communications was the first company to recognize the need to replace wired connections between phones and their accessories. They proposed their solution and are consequently considered the precursor and inventor of Bluetooth. Bluetooth takes its name from Harald Bluetooth Gormsson, a medieval Danish king (940-981 AD) from the 10th century who united Denmark and Sweden. The Bluetooth logo contains the runic characters H (for Harald, resembling an asterisk) and B (for Bluetooth, shaped like a pointed B). The Bluetooth name and logo are registered trademarks of the Bluetooth SIG (Special Interest Group), founded in 1998 and comprised of leading companies in telecommunications, computer networking, industrial automation, automotive, and other industries. The approximate lifespan of Bluetooth technology is twelve years, with four main versions. It is characterized by maintaining backward compatibility between versions based on a speed of 1 Mbps. Bluetooth v4.0 LE (Low Energy) is compatible with dual-mode chips. Briefly reviewing its history, we find the following versions: in 1998, Bluetooth voice and data technology was officially introduced, and the Bluetooth SIG was formed.
In 1999, the Bluetooth 1.0 specification was introduced.
In 2001, the Bluetooth 1.1 specification was released.
In 2003, the Bluetooth SIG finalized the Bluetooth Core Specification (BCS). Bluetooth version 1.2 incorporated improvements such as Adaptive Frequency Hopping (AFH), which enhances Frequency Hopping Spread Spectrum (FHSS) by avoiding channels prone to interference. Bluetooth v1.1 and v1.2 operate at a raw speed of 1 Mbps (equivalent to a data rate of 720 Kbps).
In 2004, Bluetooth version 2.0 + EDR (Enhanced Data Rate) was introduced, operating at a raw speed of 3 Mbps (equivalent to a throughput of 2.1 Mbps). Its improvements included higher speed and lower power consumption.
In 2007, the Bluetooth SIG adopted the BCS (Bluetooth Core Specification) version 2.1 + EDR, also operating at a raw speed of 3 Mbps (equivalent to a throughput of 2.1 Mbps). Improvements included SSP (Secure Simple Pairing), reduced power consumption compared to version 2.0, support for NFC as an out-of-band channel, improved device filtering before establishing a connection, and enhanced security by allowing encrypted links for the periodic exchange of encryption keys.
In 2009, the Bluetooth SIG adopted the Bluetooth Core Specification (BCS) version 3.0 + HS (High Speed), supporting a theoretical data transfer rate of up to 24 Mbps. This was achieved not through a dedicated Bluetooth link, but rather by using the Bluetooth link for negotiation and establishment, while the high-speed data traffic was carried over a co-located IEEE 80.11 link (typically Wi-Fi). Its main new feature was AMP (Alternate MAC/PHY), which added Wi-Fi as a high-speed data transport method. Two technologies were proposed for AMP: Wi-Fi and UWB (UltraWideBand), although the latter was ultimately not included. It allowed service data to be sent without establishing a dedicated L2CAP channel and used AES encryption. In 2010, the Bluetooth SIG adopted Bluetooth version 4.0, characterized by a speed of 24 Mbps, reduced power consumption, and improved security. It integrated Bluetooth Classic, Bluetooth HS (High Speed), and Bluetooth LE (Low Energy). Bluetooth HS is based on Wi-Fi, while classic Bluetooth consists of traditional Bluetooth protocols. Bluetooth LE allows for two types of implementation: (i) Dual mode. In this implementation, Bluetooth LE functionality is integrated into the classic Bluetooth controller. The resulting architecture shares many of the functionalities and radio capabilities of classic Bluetooth, resulting in a minimal cost increase compared to classic Bluetooth. Manufacturers can use traditional classic Bluetooth in the form of Bluetooth v2.1+EDR or Bluetooth v3.0+HS integrated circuits with the new Low Energy (LE) stack, enhancing the development of classic Bluetooth and enabling devices with new capabilities. (ii) Single mode. These chips only include the new LE protocol stack and are not compatible with previous Bluetooth versions (v2.1 and v3). Gartner's report, "Ten Mobile Technologies to Watch in 2010 and 2011," specifies the top 10 mobile technologies with the greatest impact for 2010-2011, and Bluetooth 3.0 and Bluetooth 4.0 are ranked first. Bluetooth 3.0 is useful for interacting with Wi-Fi and achieving faster data transmission, while Bluetooth 4.0 (speeds up to 24 Mbps) introduces Low Energy (LE) mode, enabling communication with external peripherals and sensors. Bluetooth 4.0 and its LE technology will enable a range of new sensor-based business models in industries such as healthcare, fitness, and environmental monitoring. It will also be used in headphones and PC peripherals to enable new features such as PCs that automatically lock when users move away from them. It's worth noting that as of mid-2011, manufacturers like Samsung were still selling phones with Bluetooth v2.1, and Android v2.2 tablets with Bluetooth v2.1 were still being sold. The IEEE 802.15 working group has defined various classes of WPANs, such as IEEE 802.15.1 (Bluetooth). Near Field Communication (NFC) technology can provide a setup service to simplify the somewhat complicated process of configuring longer-range wireless technologies like Bluetooth, Wi-Fi, etc. Bluetooth technology can bridge diverse industries such as mobile phones, computing, and automotive. Bluetooth simplifies and combines different forms of wireless communication. Bluetooth is a wireless technology for short-range data exchange between fixed and mobile devices, enabling the creation of WPANs (Wireless Personal Area Networks). Originally conceived as a wireless alternative to wired RS232 connections, it can connect various devices, overcoming synchronization issues. Currently, its applications are vast: headphones, data synchronization, access points (e.g., connecting PCs to the internet), dynamic social networks in large nightclubs, and more. Bluetooth is also an industrial specification for WPANs. It's an inexpensive, short-range technology (10 to 30 meters) with low complexity, operating in the 2.4 GHz ISM (Industrial, Scientific, and Medical) band. (The entire spectrum from 2.4 GHz to 2.4835 GHz is divided into 79 1 MHz channels, and FHSS/Frequency Hopping Spread Spectrum is used.) It's linked to the IEEE 802.1.15.1 standard. Unlike Wi-Fi/WLAN and WiMAX/WMAN, Bluetooth doesn't have a centralized security control point. Authorization, authentication, and encryption rely on a shared secret link key. This link key is generated during a pairing process the first time two devices communicate. The PIN code, which is fixed or user-selectable, must be difficult to guess and long (e.g., 16 characters). Authentication is based on a challenge-response mechanism, at the end of which both parties share the same link key. The encryption key is calculated from the link key and is changed with each new connection.
Final Considerations
Our research group has spent many years analyzing, evaluating, and synthesizing Bluetooth applications and generating WPAN networks from a practical perspective, exploring their possibilities in WPAN/WBAN environments, and deploying protection mechanisms. Bluetooth has evolved while maintaining compatibility, from basic piconet services operating at 1 Mbps to the new multi-Mbps services being proposed. This article is part of the activities developed within the LEFIS-Thematic Network.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto
Bibliography
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2012.
Areitio, J. “Analysis of the risks and countermeasures in security-privacy of NFC technology in mobile devices”. Conectronica Magazine. No. 156. April 2012.
Bluetooth SIG (Special Interest Group): http://www.bluetooth.com/; http://www.bluetooth.org/
Wireless vulnerabilities and exploits: http://www.wirelessve.org/
Pearson, B. “Wireless Network Security. A Beginner's Guide”. McGraw-Hill Osborne Media. 2011. Burmester, M. and Yasinsac, A. “Security Issues in Ad-Hoc Networks”. Springer. 2006.
Cayirci, E. and Rong, C. “Security in Wireless Ad-Hoc and Sensor Networks.” Wiley. 2009.



