 When we need to protect a laptop, PC, Mac, or server from theft, we can anchor it to the workstation with welded brackets or use removable steel cables with padlocks. We can also enclose PCs, switches, routers, patch panels, etc., in armored cabinets. Often, it's necessary to physically protect WiFi access points and all types of antennas, and the solution is to hide them in false ceilings (like plasterboard) or conceal the antennas inside false chimneys (applying the saying: out of sight, out of mind).
When we need to protect a laptop, PC, Mac, or server from theft, we can anchor it to the workstation with welded brackets or use removable steel cables with padlocks. We can also enclose PCs, switches, routers, patch panels, etc., in armored cabinets. Often, it's necessary to physically protect WiFi access points and all types of antennas, and the solution is to hide them in false ceilings (like plasterboard) or conceal the antennas inside false chimneys (applying the saying: out of sight, out of mind).
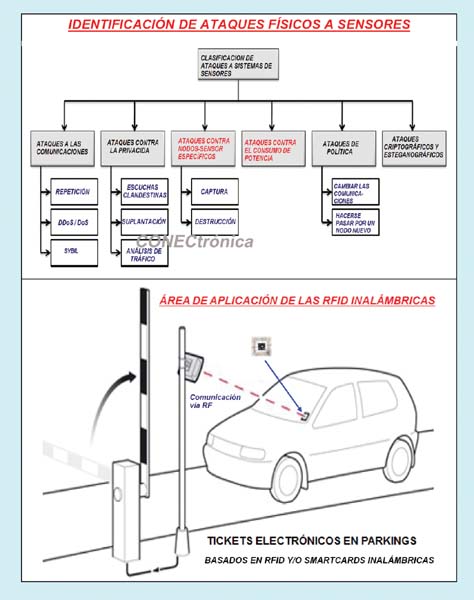
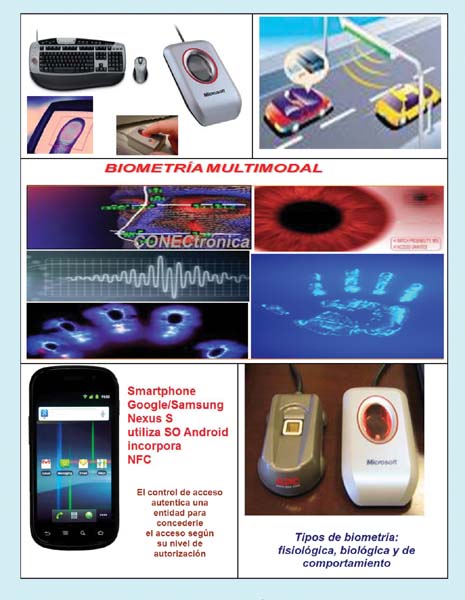
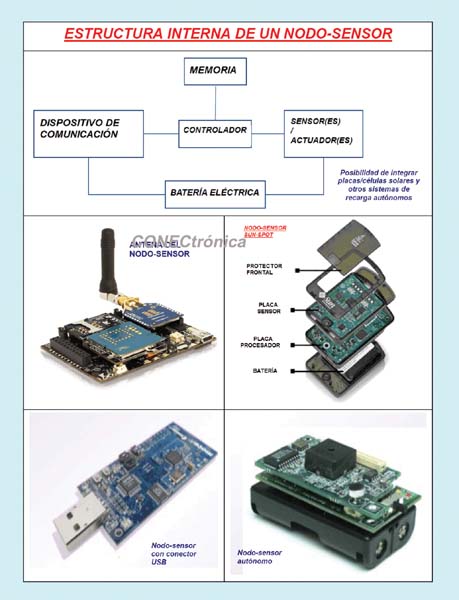
Sometimes the deployed Wi-Fi access points are satellite-type with minimal functionality and depend on a complete main base station to operate. Therefore, if a satellite access point is stolen, it is useless without the main base station. To protect mobile devices such as tablets and smartphones from theft, satellite beacons can be used. If sensor nodes have been deployed as a network in a hostile area controlled by enemies, as a physical countermeasure, each sensor node can be equipped with an internal mechanism that disintegrates or renders it unusable if it detects tampering or an attempt to access its contents. This could be achieved by, for example, burning itself, exploding, encrypting and erasing all its data, etc. When physical protection of data entry keyboards is required, vandal-proof (MIL standard) keyboards resistant to fire, explosions, acid, etc., can be used. When we need to physically protect a computer system, such as a server farm, we might consider enclosing it in a data center or a windowless, well-ventilated room with a door, or in a safe equipped with locks, bolts, or padlocks. Locks can use keys, cards, or biometrics. Keys can be mechanical (lock picks are a common attack tool), electronic (with RFID/NFC, RF/light emission), or magnetic. Access cards can be punched cards, magnetic stripe cards (three tracks: the first for the user's name, format, etc., for example, 79 characters; the second for the account number, expiration date, issuing bank, etc., for example, 40 characters; and the third often unused), optical cards with 1D barcodes (Code 39) or 2D barcodes (QR codes), and smartcards with galvanic contact. Wireless smartcards, RFID, and NFC are also used. Locks can be mechanical/magnetic key locks or mechanical/electronic combination locks. Nanotechnology-based invisibility paints are being researched to make computing devices, sensor nodes, and video cameras invisible, preventing theft or damage. Perimeter and volumetric alarms based on multiple sensors, capable of triggering loud sounds (many decibels to stun), sounds audible only to animals or teenagers, or sounds silent only to the police, can aid in physical protection. For physical protection, we also find fences, walls, barbed wire, ditches, minefields, TV cameras, webcams, satellite surveillance, radars, drones (UAS/Unmanned Aerial System, UAV/Unmanned Aerial Vehicle, VANT/Unmanned Aerial Vehicle), pressure, voltage, temperature, light, sound, magnetic field detectors, etc., as well as specialized personnel such as sworn/armed guards, police, security guards, bodyguards for people and robots, trained animals such as dogs, birds, reptiles, insects, sharks and even intensive surveillance robots.
Physical Cybersecurity in Smartcards/SIMs:
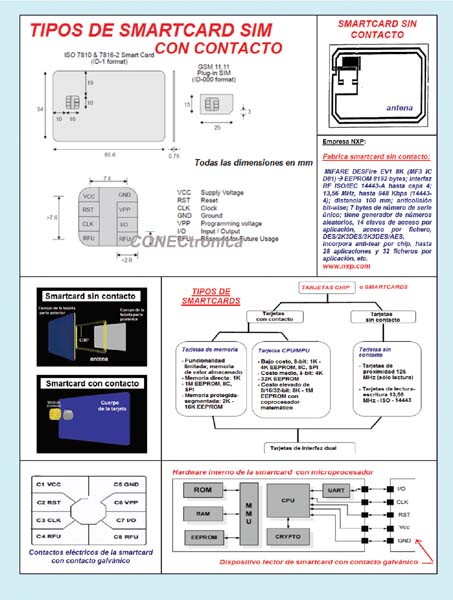
A SIM (Subscriber Identity Module) card is a type of smartcard issued by a network provider. It is a chip or integrated circuit that contains personal information and keys that allow the user to authenticate themselves to a network or entity.
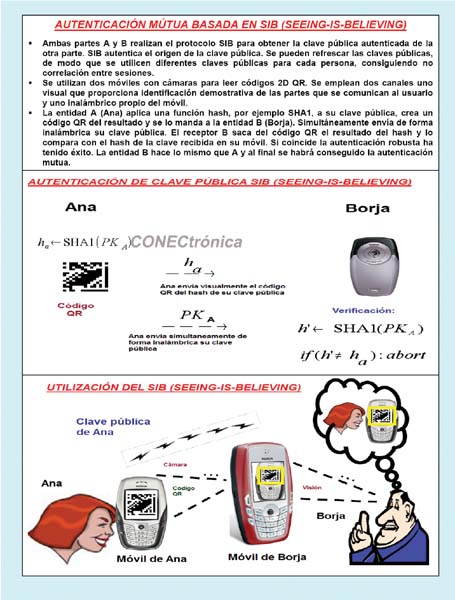
The following components are integrated into this chip, interconnected via buses: a CPU/processor, memories (ROM, EPROM, Flash-E2PROM, FRAM, RAM), a one-bit serial communication module with galvanic connection, and a wireless communication module for the smartcards themselves. JavaCard smartcards support the Java programming platform and enable DES/AES/RSA encryption, SHA-1 hashing, asymmetric key generation, and more. There is a trade-off between their cost and their resistance to physical intrusion (unauthorized access). They integrate protected memory for storing secrets and possess cryptographic capabilities such as SHA-1 hashing, RSA/AES/3DES/IDEA encryption, asymmetric key pair generation, and more. The galvanic-connected SIM cards connect to a CAD (Card Acceptance Device) using a one-bit serial link and receive their clock and power from it.
It comes in two formats: (i) a miniature SIM for embedding in a mobile phone/smartphone; and (ii) a credit/debit card/ID card-sized SIM for galvanic or wireless connection. The information a SIM can store is highly varied: from SMS/MMS messages, contact lists, account numbers, PIN (Personal Identifier Number) and PUK (Personal Unblocking Key, an eight-digit code used if the user forgets their four-digit PIN), IMSI (International Mobile Subscriber Identifier), a 64-bit/fifteen-digit personal identifier of the owner's network and country, ICC-ID (Integrated Circuit Card-Identifier), an 18-digit hardware identification plus a check digit, Ki security authentication value, encrypted information, and more. Although various levels of security can be defined internally, the fact remains that the protected content can be physically accessed by malicious means.
The main levels of access defense are: (1) Prevention of unauthorized access and use using a four- to eight-digit PIN and a PUK of up to nine digits, local security measures where the network is not involved. (2) Authentication of customer identity. Using the A3 authentication algorithm and the A8 encryption key generation algorithm. Both algorithms are stored on the SIM card. (3) Anonymity. This consists of sending TMSI (Temporary Mobile Subscriber Identity) instead of IMSI. (4) Encrypting information transmitted over the air. Using the A5 encryption algorithm embedded in hardware, where a new encryption key Kc is used for each call, and the Ki and Kc keys are not transmitted over the network. Physical protection involves the use of physical means to protect valuables, information, or access to restricted resources. The main areas of physical protection are: (a) Hardware attacks. Attacks against hard drives, CPUs, smart cards, etc. (b) Eavesdropping. Attacks that monitor signals emitted from or exchanged between computing devices (electromagnetic emissions from computers, Bluetooth, etc.). (c) Attacks on physical interfaces. Exploiting weaknesses in the physical interfaces of systems. (d) Location protection. Protecting the location where the hardware resides if it includes GPS/Galileo/GLONASS/QZSS or if the generated signals are triangulated. (e) Physical intrusion detection. Detecting intrusions at the location where the hardware resides.
Physical attacks on smart cards. Countermeasures.
The following types of attacks on the physical cybersecurity of a smartcard can be identified:
(1) Invasive attacks. By definition, these destroy the chip, require sophisticated and expensive equipment (microscope with laser cutter), and are useful when very little is known about the chip. They are characterized by exposing the chip itself, exploring/monitoring its surface to extract information, interacting with that surface to modify the chip, reverse-engineering the chip, analyzing the collected information, and understanding the chip's functional units. Once the data and secret codes are obtained, a new smartcard can be cloned. Countermeasures to this type of attack include surrounding the chip with an opaque substance that cannot be separated from the chip without burning it.
(2) Non-invasive (side-channel) attacks. These are easier, cheaper, and faster to perform, and they do not destroy the chip. They are characterized by monitoring execution characteristics such as execution time, radiation level, power consumption, etc. Normal operations are observed, or faults are induced. They are classified as follows:
(i) Passive attacks. These involve monitoring outputs from the chip, such as electromagnetic radiation, power consumption, execution time, etc.
(ii) Active attacks. These involve carefully injecting data, clock signals, and power into the chip, and then measuring the chip's behavior. Some active attacks include:
(a) Glitch attacks. Various methods are used, such as generating a sharp voltage spike, increasing the clock frequency, subjecting the chip to an electric field, intense cold, etc., with the aim of causing a computational error that leads to the leakage of sensitive data, such as a key dump.
(b) Timing attacks. The following method is used: generate a large number of “encrypt this file with your secret key” messages and send them to the smartcard, measure the time required to perform the operations and deduce the cryptographic key from these measurements.
(b) Power analysis attacks. This involves drawing conclusions about the chip's internal behavior from measurements of its power consumption. Different machine instructions are known to consume different amounts of power. Internal buses also consume power when the bus lines change from logic zero to logic one, so the number of bits changing on the bus can be estimated by measuring the amount of power consumed. The attack is simple: an electrical resistor is placed across the chip's power supply line, a high-resolution voltmeter with high sampling frequency capability is placed across this resistor, and a computer is used to store and analyze the resulting traces. Counter noise in the measurements is averaged over a large number of transactions. Two different types of power analysis can be identified for extracting smartcard/SIM keys: (i) SPA (Simple Power Analysis). This is the simplest method. (ii) DPA (Differential Power Analysis). This uses statistical techniques.
Countermeasures to these types of attacks include: (i) Obfuscation. This involves inserting false instructions into conditional jumps. (ii) Interleaving multiple threads of control; this presents difficulties in smartcards due to their limited computing resources. (iii) Randomization. This involves generating an internal clock signal by inserting random delays into the external clock. (iv) Proactivity. This involves anticipating attacks. Smartcards should be part of a system's overall security architecture. This architecture should detect anomalies to minimize losses, and security should be updated regularly. (v) Environmental sensors. This involves detecting if an attacker reduces the clock signal to more easily monitor the chip's internal calculations.
Direct physical cyberattacks against computing devices.
Currently, an attacker can damage a computing device whether they have direct physical access to it or are simply in its vicinity. Users of computing systems are sometimes untrustworthy. Some of the most relevant direct cyberattacks are:
(1) Eavesdropping. This is defined as secretly listening to the communication of another entity/person. Therefore, it is necessary to protect the environment in which a computer system is used. Two types of eavesdropping can be identified:
(i) Passive eavesdropping. This consists of monitoring communication without leaving a trace, for example, using wired or wireless sniffers. Over-the-shoulder techniques involve installing small hidden video cameras/webcams or observing with binoculars through windows, even using infrared vision to see in the dark. Countermeasures at ATMs include limiting the viewing angle of their displays, protecting the keystrokes, and altering the physical location of the keys after each key press. Eavesdropping can be carried out over guided and unguided media: (a) Over coaxial cable and twisted pair. Measure the leakage electrical impulses. The cable is cut and a branch is made to a secondary wire. In Ethernet cable, briefly disconnect and insert a passive listening device. Layer 2 switches include a mirror port that allows monitoring of the other ports. (b) Fiber optic cable. Bend the cable and read the escaping light with an optical sensor. Another method is to cut the fiber and reconnect it with an 80/20 inline splitter; 80% of the signal is transmitted and 20% is used for monitoring. (c) Satellite and microwave communications. The attacker positions themselves near the receiver/victim to read their communication. Some countermeasures against eavesdropping include: brief cable disconnection detectors, signal power reduction detectors, end-to-end encryption, and cable cut detectors using reflectometry. As countermeasures to countermeasures: boost the signal to mask the signal loss, and carry out the attack at night when it is less likely to be detected. Clandestine wiretapping by monitoring energy emissions can be classified according to the type of energy signal: (i) Electromagnetic radiation. Monitoring of CRT, LED, and LCD displays. Signal emissions from servers. (ii) Optical emissions. Cathode ray tube and LED/LCD displays emit light pulses that can be monitored with photosensors, and the screen image can be reconstructed remotely. (iii) Acoustic emissions. By listening to keystrokes with directional microphones, 78.8% of the keystrokes can be reconstructed.
 Listening to a CPU can reveal the instructions it executes.
Listening to a CPU can reveal the instructions it executes.
Software keyloggers are introduced into a victim machine as malware programs and allow for the clandestine capture of sensitive information (everything typed, such as BIOS and operating system passwords, account numbers, etc.). One countermeasure is to use single-use virtual keyboards on the screen, which don't require typing but rather selecting with the mouse and accepting what is displayed on the screen. Hardware keyloggers (which have internal memory, don't require operating system drivers, include an internal clock, support WPA-2/WPA/WEP, generate email reports, and connect to the internet wirelessly) are hardware devices that can be installed between the keyboard and the computer via USB-to-USB or PS/2-to-PS/2 connectors to capture everything typed, such as passwords, keys, and account numbers, to flash memory. The attacker can either recover the physical device or the device can autonomously transmit the data wirelessly via Wi-Fi or Bluetooth in encrypted form. It can capture BIOS passwords, granting complete control over the machine. Hardware keyloggers are used to monitor emails, web browsing, chats, and social media activity by minors and employees to track employee productivity and protect minors from potential pedophiles and other online predators. To be legal, companies must explicitly disclose their use.
(ii) Active eavesdropping. This involves modifying or creating/fabricating falsified communication; this is the case of MITM attacks.
(2) Tempest. This is a US government standard designed to limit the emission of electromagnetic/energy signals carrying sensitive information from computer equipment. The protection zones defined in the NATO/SDIP-27 standard are: (i) Level A. Near immediate access. At a distance of one meter; for example, an adjacent room. (ii) Level B. At a distance of twenty meters or a similar level of attenuation; for example, inside a building. (iii) Level C. At a distance of one hundred meters or equivalent attenuation. Some countermeasures against Tempest electromagnetic emissions are: (a) Blocking emissions. Three possibilities can be identified depending on the type of energy emitted: (i) Blocking visible light. Use windowless rooms or cover windows with opaque or unidirectional material. (ii) Blocking acoustic emissions. (a) Use rooms lined with sound-absorbing materials or deploy highly sophisticated acoustic systems capable of generating acoustic signals with opposite polarity that cancel out the original sound/noise. (iii) Electromagnetic radiation blocking. This involves using a Faraday cage, that is, surrounding the room/building/card to be protected with metallic material (plates, mesh) or special plastics capable of blocking electromagnetic signals. (b) Modifying/masking emissions. This involves generating and spreading random noise signals (jamming/interference) so that the signals carrying information are lost in the noise. This is similar to RF jamming devices used to prevent mobile phones from having coverage in party venues or police/military buildings, or to prevent a bomb from being detonated by RF as a military vehicle passes by.
(3) Forensic Techniques. This involves identifying, preserving, recovering, analyzing, and presenting digital evidence (facts and opinions) about information found on digital storage media for use in legal proceedings or to improve security. Forensic techniques can be used by attackers to extract information from computing devices (PCs, smartphones, etc.). They allow for the recovery of deleted files since most operating systems only remove the metadata of a deleted file and do not overwrite the file itself for actual destruction. Some overwritten files can be recovered because magnetic traces may remain. Some useful countermeasures are: overwriting the files in multiple passes with random data or physically destroying the disk with fire, drills, explosives, etc. A cold boot attack involves freezing the DRAM of a running computer, shutting down the computer, booting the system with a live external boot drive, and extracting the disk encryption key from RAM. As a countermeasure, do not store encryption keys in plaintext in RAM.
(4) External bootable storage media (DVD, CD, USB). A bootable computer operating system stored on external media (DVD, CD, USB drive) allows a computer to be booted without its hard drive. Attackers can boot a computer using this storage medium, bypassing its native operating system and any authentication mechanisms, which allows them to read and modify the data on the hard drive. Some useful countermeasures to protect hard drive data when an attacker steals a laptop include: installing BIOS passwords so the computer cannot boot without the authentication password; setting a password on the hard drive; encrypting the hard drive; or installing security tools to disable the PC in case of theft.
(5) Attack against availability. For example, injecting jamming/interference signals so that it cannot open a key lock based on an RF emitter.
Final Considerations
Today, protecting access to all types of computing devices is crucial, both from a physical and digital perspective. While we access them through networks, keyboards, or other digital interfaces, we can also access data centers using jackhammers, SIM cards to clone them, sensor nodes to disrupt networks, PCs to steal or modify their contents, the contents of smart cards using surgical techniques via laser with an electron microscope and even liquid nitrogen, etc.
This article is part of the activities developed within the LEFIS-Thematic Network.
Author:
Prof. Dr. Javier Areitio Bertolín – E.Mail:
Professor at the Faculty of Engineering.
Director of the Networks and Systems Research Group. University of Deusto
Bibliography
Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo. 2012.
Areitio, J. “Evolution of Threats and Trends in Network Security in the Web Context”. Conectrónica Magazine. No. 142. November 2010.
Areitio, J. “Identification and Analysis of Web Application Protection”. Conectrónica Magazine. No. 143. January 2011.
Schneier, B. “Economics of Information Security and Privacy”. Springer. 2011.
Whitman, ME and Mattord, HJ “Principles of Information Security”. Thomson. 2009.
Nicastro, FM “Security Patch Management”. CRC Press. 2011.
Norman, TL “Risk Analysis and Security Countermeasure Selection”. CRC Press. 2009.



