Background to Development:
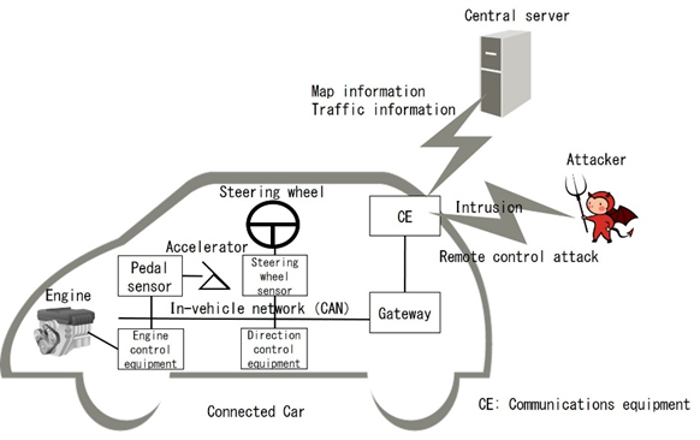
In recent years, cars connected to external networks, such as the internet, known as "connected cars," have been increasing in number, and technological development aimed at creating new services, including enhanced safety and autonomous driving capabilities, is ongoing. It has been noted, however, that there is a danger that connected cars can be remotely controlled through a cyberattack. By sending messages through the vehicle's network, called the controller area network (CAN), the behavior of the car's systems and operations can be controlled. An attacker executing a remote control attack on the system hijacks its communications equipment and the gateway that connects to the external network and sends malicious CAN messages. As a result, attackers could cause the car to do things against the driver's wishes, including sudden acceleration or braking, which could lead to a serious accident. In response to this type of attack, security countermeasures such as the following are indispensable at various stages.
Fujitsu Laboratories has developed technology to detect malicious messages using vehicle-mounted equipment known as electronic control units (ECUs).
1. Entry-point countermeasures to prevent hacking of communications equipment.
2. Vehicle-mounted equipment to detect malicious messages.
3. Automatic security updates of countermeasures based on analyses performed on the central server.
Issues:
Because there are limits to the computational performance of vehicle-mounted equipment, the detection equipment needs to have a low computational load. Furthermore, too many false positives can limit or completely stop the functionality of the communication equipment, hindering smooth driving. This can even create a situation where self-control becomes impossible. Since this can lead to dangerous situations, it is necessary to limit the number of false positives. Detection technologies detect that an attacker has sent a message by using the fact that CAN messages are sent regularly and then determining whether the transmissions fall outside the permissible interval between messages. However, because even genuine messages can be sent outside of regular intervals while driving, the problem has been that genuine messages are mistakenly detected as attacks.
About the technology developed
: Fujitsu Laboratories has now developed a method that can detect attack messages in real time while limiting the number of false positives, even when genuine CAN messages arrive later or earlier than ordinary cycles.
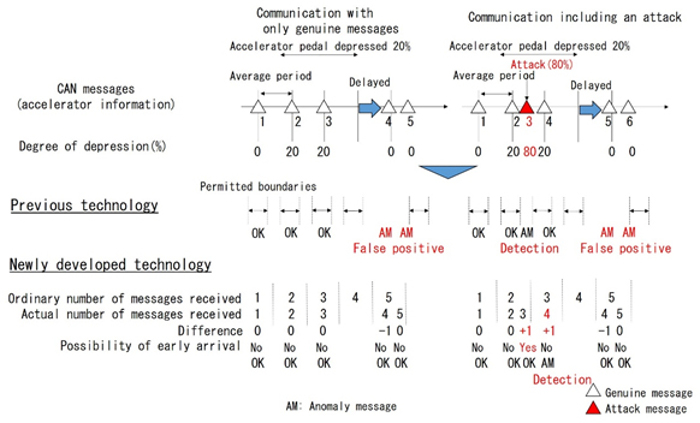 This method compares the number of messages received during normal message cycles with the number of messages actually received, checking for any discrepancies. If a discrepancy exists, the method determines whether it is a temporary problem or the result of an attack by relaying information about that discrepancy to subsequent cycles.
This method compares the number of messages received during normal message cycles with the number of messages actually received, checking for any discrepancies. If a discrepancy exists, the method determines whether it is a temporary problem or the result of an attack by relaying information about that discrepancy to subsequent cycles.
If a message is delayed (Figure 2, left):
In the case where genuine message number 4 is delayed, with existing technology it would be incorrectly identified as an attack, as it falls outside the permissible limits of the intervals between messages. However, with the new technology, the negative discrepancy in the number of messages received when message number 4 is received is not considered an attack. By relaying information about the missing message until message number 5 is received, the total number of messages actually received and the number of messages under normal conditions match, and the message is thus determined to be genuine.
If an attack message is received (Figure 2, right):
If an attack message is received after genuine message number 2, both the previous technology and this technology may detect it as an attack. With this technology, a positive discrepancy is recognized when an attack message is received, and this information is carried over until genuine message number 4 is received. Once genuine message number 4 is received, it is detected as an attack. If the actual interval between message transmissions within the vehicle is approximately 10 milliseconds, this method can detect attacks within a few dozen milliseconds of an attack message being received, detecting attacks in near real-time.
Effects:
When this technology was evaluated on approximately 10,000 simulated attack data patterns, in which messages from all known attack methods were inserted at various times into 600 seconds of CAN data recorded from a real car, it was confirmed that it could detect all attacks without generating false positives. This technology enables robust countermeasures through attack detection, supporting the provision of a safe and trouble-free journey.
future plans
include expanding its Mobility IoT platform business, which provides mobility solutions for society. To protect connected cars against cyberattacks, this platform will offer individual-level protections for entry point defense, in-vehicle network defense, and ECU defense. Fujitsu intends to commercialize this technology during fiscal year 2018 as a detection feature that supports the protection of connected cars.