INTRODUCTION.
For some time now, a new generation of cyber resilience has been under development based on superior/advanced-massive-multidimensional AI, operating with continuous and extreme anticipation and maximum level/degree of observability, robustness, maturity, flexibility, quality, speed, efficiency, fault tolerance, resistance, performance, versatility, automation, orchestration, invisibility, effectiveness, cancellation of all types of attempts at possible damage/impacts, etc. The end result is NG-CR capable of automating the complex/extensive and anticipating the unexpected/invisible (with extreme observability of clues, traces, indications, anomalies, failures, errors, slowness, non-continuous verification, defects, sensor awareness, solid predictions, etc.) and neutralizing/blocking/erasing in all phases in advance all possible indications/attempts of damage/vulnerabilities in all types of infrastructures with all kinds of assets/entities-H/NH from all IT/OT/IoT worlds, etc., encompassing what exists and what may exist in the future.
CATEGORIES OF FUNCTIONS/MECHANISMS.
Some of the categories of functions/mechanisms in NG-CR are:
(1) Prevent, identify, protect, detect early, respond/defensive-offensive actions, fully recover, etc. Continuously verify before, during and after in a complete manner with ZT/ZK technology.
(2) Enabling computer systems to operate without interruption and recover from even very subtle cyberattack attempts.
(3) Allowing the existence of potentially compromised components using technologies such as homomorphic encryption that makes it possible to run functions in untrusted processing environments without revealing the functions or data they process.
(4) Enable dynamically deploying a complete set of reliable components (in PUFs, WORM, NAT/Network-Address-Translation, ECC/Error-Checking-and-Correcting, VPN/Virtual-Private-Networks, etc.) on which missions can depend.
(5) Allow the inclusion of out-of-band functionalities to observe/monitor the system and restore in advance the capabilities of the mission-critical system that is being targeted.
(6) It integrates a comprehensive set of extreme predictive and inferential capabilities in parallel, with a "WHAT-IF" philosophy (what if… a subtle attempt occurs, what if an invisible attempt is detected, what if an indication of an anomaly appears, what if a perversion value is measured, etc.) based on exhaustive parallel extreme dynamic analysis with sound, justified hypotheses and unlimited cardinality. It utilizes situational awareness, providing proactive, anticipatory actions to protect all types of assets, processes, infrastructure, etc. It can respond to all kinds of cyber incident attempts with the capacity to prepare and defend all types of critical infrastructure.
(7) Continuous self-monitoring and self-verification of performance in real time for all types of entities (infrastructures, micro-networks, dynamic cyber-attack surfaces, etc.) and extreme and advanced self-simulation of all possible problematic environments
(8) Predictive self-maintenance and evaluation of quality, maturity, reliability, robustness, etc. of systems, micro-grids, etc. by analyzing with massive Advanced AI to predict unprecedented patterns and information.
(9) Extreme observability with proactive feedback on efficiency, robust cybersecurity, etc., for all types of assets (devices, ecosystems, networks, servers, etc.). Potential for extreme parallel self-creation of digital twins for all-around observability where multiple dynamics interact seamlessly. This makes it possible to obtain virtual replicas of any system/environment/asset by combining them with real-time system data.
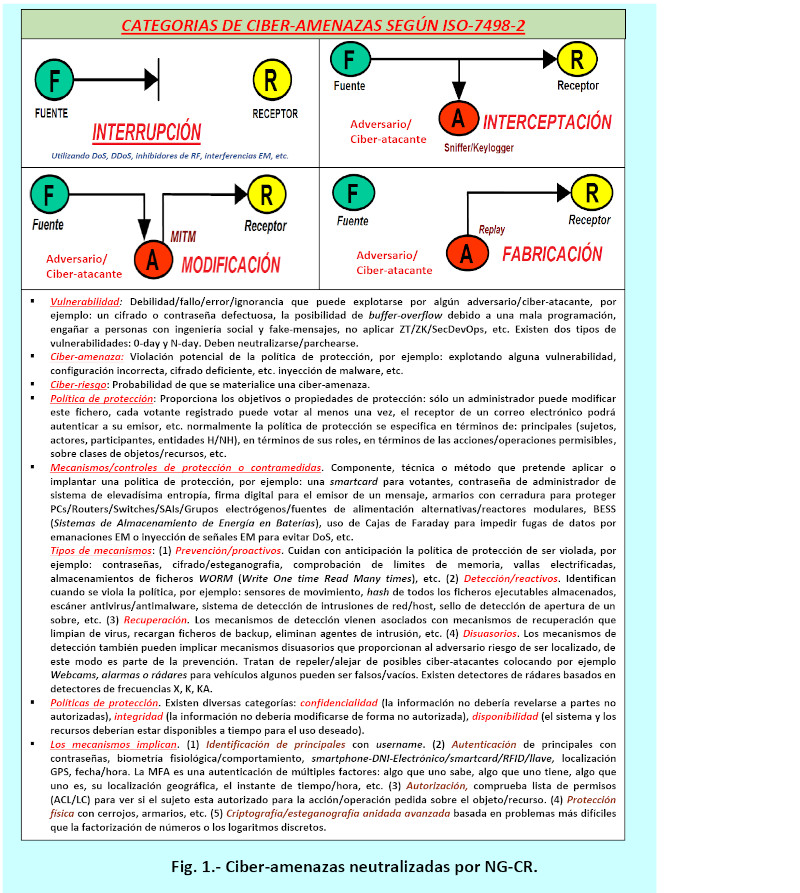
Figure 1: Cyber-threats neutralized by NG-CR
OPERATIONAL MECHANICS. CORRELATION BETWEEN CAPABILITIES, PROCESSES, TECHNIQUES/TECHNOLOGIES AND CONTROLS IN NG-CR.
The NG-CR is characterized by including a complete set of capabilities/potentialities, such as, for example:
(1) Extreme anticipation. This allows for maintaining a continuous state of readiness with MF (with an extreme number of factors), which means preventing potential compromises to any of the mission functions in the face of potential adverse conditions (attempted cyberattacks, cyber incidents, vulnerabilities, etc.). This involves knowing and understanding (using situational awareness by discovering, analyzing, and observing behaviors, and predicting and exploring scenarios) through asset and dependency management, with dynamic/extreme cyber threat/vulnerabilities management and scenario management.
(2) Extreme resilience. This enables the maintenance of normal operations, meaning the continuation of mission functions despite any potential attacks, adverse conditions, etc. It utilizes parallel, dynamic cyber-resilient architectures, strategies, tactics, and techniques based on extreme anticipation, with containment, micro-segmentation, and defensive/offensive/response operations. (3) Extreme recovery. This allows for the rapid restoration of mission functions in the face of all types of potential malicious attacks and adverse conditions. It utilizes proactive risk management and remediation, the use of multiple encrypted backups (data, electricity, software/firmware/hardware/apps/APIs/OSs, backup channels (terrestrial and satellite communications), and proactive return-to-normal activities, etc.
(4) Extreme evolution. This enables dynamic and highly proactive changes to mission functions and support capabilities to prevent potential impacts from current or predicted adverse conditions. It utilizes metrics/outcomes analysis, root cause/cyber-incident analysis, etc. It redefines processes/plans and ensures extreme proactive measures based on crisis simulation, scenario testing, recovery testing, stress testing, red-team/blue-team deployments, dynamic penetration testing, sandboxing, etc., all continuously and adaptively.
The NG-CR integrates a very large group of techniques/technologies, such as, for example, the following:
(1) MF Anticipatory Adaptive Response. Enables dynamic, parallel, and precise/appropriate response to all types of situations using anticipatory agile contingency operational techniques to maintain necessary operational capabilities and avoid potential consequences and possible destabilizations/desynchronizations by taking action in advance where necessary at all times.
(2) Observability (allows understanding the causes, the why and the how of any potential malicious activity/problem; observability integrates several pillars: temporal correlation, predictive analytics, drill-down analysis (i.e., viewing data in greater detail to detect anomalies and anticipate cyber incidents before they occur, etc.)/continuous extreme MF monitoring/surveillance. It continuously and in parallel collects, merges, and analyzes all types of data/metadata/etc. from logs/SIEM/metrics/telemetry/traces/context/etc. to utilize cyber threat intelligence, identify zero-day/n-day vulnerabilities, find early indicators/signs of potentially adverse conditions, and proactively identify potential attempts at damage/infections/malicious actions/open ports/passageways, etc. The monitoring system compares integrity measurements with well-known measurements provided by TPM (Trusted Platform Module) systems where it stores hashes/digital signatures, PUFs, etc.
(3) Coordinated defenses in depth. It makes it possible to coordinate an extreme number of different mechanisms (defensive and offensive actions in depth) in parallel to protect to the maximum extent all types of resources/assets (human and NH) (critical and additional) distributed from all ecosystems, layers, systems/subsystems, organizations, etc.
(4) Extreme use of deception/confusion, anonymity, subliminal channels, steganography, post-quantum MF nested encryption, etc. Allows confusing, deceiving, inducing/leading to erroneous conclusions, etc., all possible adversary agents/entities attempting something malicious.
(5) Extreme MF diversity. Enables the use of an extremely heterogeneous set of technologies, data sources, processing locations, communication paths, backup power supplies/UPS/Generator sets, encrypted backups, etc. to neutralize all types of malicious actions/failures, including cyberattacks that attempt to exploit vulnerabilities (0-day/n-day), contaminated APPs/APIs, outdated hardware/software/firmware, compromised supply chains, etc.
(6) Extreme dynamic positioning. Allows anonymous distribution and dynamic relocation of functionalities and assets.
(7) Extreme dynamic representation. Enables support of mission situation awareness and response using dynamic representations of components, systems, services, adversary activities and other adverse situations and the effects of altering courses of action.
(8) Non-persistence. Allows retaining information, services, electricity and connectivity for a period of time in order to neutralize possible attempts at exposure to corruption, modifications or usurpation.
(9) Privilege restriction. Enables dynamically and in parallel the restriction of privileges to users and cyber-entities and the establishment of privilege requirements to resources based on criticality and ZT.
(10) Realignment. Allows resources to be aligned (or realigned) with mission-critical functions, thereby reducing potential cyber-attack surfaces, the potential for unintended consequences, the potential for cascading failures, possible oscillations, etc.
(11) Extreme redundancy. Provides multiple protected instances of critical information and resources.
(12) Segmentation/Separation. This allows for the dynamic separation (logically and physically) of components based on criticality and trustworthiness to limit the extent of potential damage attempts. It utilizes network microsegmentation, multi-layered containment/quarantine zones, sandboxing, etc. Associated with this is a dynamic set of controls such as protected domain processing, flow control policies, etc.
(13) Extreme proven integrity. Provides mechanisms to find out extremely early if critical services, current information storage, components, etc. have been targeted for damage.
(14) Unpredictability. Allows dynamic/continuous parallel and random changes to make potential cyber-attack surfaces unpredictable/unoperational.
The NG-CR integrates a very large group of approaches/processes, such as, for example, the following:
(1) Knowing-understanding/cognitive approach. NG-CR maintains useful representations of mission dependencies and the status of all resources/assets with respect to all possible attempts at adversity/deception/infection. It correlates with the techniques: Observability-monitoring-vigilance-extreme-continuous, deception, extreme dynamic positioning, extreme dynamic representation, proven integrity, and unpredictability.
(2) Continuous preparation. This allows for maintaining a set of parallel courses of action that predict all types of adversary/cyber-attacker attempts with extreme anticipation. It correlates with the following techniques: continuous, extreme, observability, monitoring, surveillance, coordinated defenses, and extreme dynamic representation.
(3) Prevention and avoidance with extreme anticipation. This makes it possible to prevent or avoid the successful execution of potential cyberattacks or any anticipated attempt to create adverse conditions. It correlates with the following techniques: coordinated defenses, extreme use of deception, extreme MF diversity, extreme dynamic positioning, non-persistence, privilege restriction, segmentation/separation, and unpredictability.
(4) Continuity. It allows maximizing the duration and viability of essential mission functions during potential adverse conditions. It correlates with the following techniques: adaptive anticipatory response (MF), observability, coordinated defenses, non-persistence, privilege restriction, realignment, segmentation, and proven integrity.
(5) Reduce. It makes it possible to dynamically limit and constrain potential attempts at harm and adverse conditions. It correlates with the following techniques: anticipatory adaptive response (MF), coordinated defenses, mass deception, diversity, positioning, non-persistence, massive redundancy, proven integrity, and unpredictability.
(6) Rebuild-reconstitute. This allows for the dynamic reorganization and transfer of resources to adequately provide a set of mission functionality following potential adverse conditions. It correlates with the following techniques: adaptive anticipatory response (MF), continuous extreme observability/monitoring/vigilance, coordinated defenses, massive redundancy, and proven integrity.
(7) Transform. This enables the dynamic and parallel change of behavioral aspects (technological, organizational, control, governance, management, etc.) with great speed in response to prioritizing the neutralization of potential adverse conditions or cyberattacks. It correlates with the following techniques: extreme dynamic representation and realignment/realignment.
(8) Re-architecture. Allows dynamic modification of all sub-architectures for continuous global improvement of cyber-resilience.
It correlates with the following techniques: extreme MF diversity, extreme dynamic positioning, and non-persistence.
Some strategic mechanisms that NG-CR dynamically activates are:
(1) Redundancy with diverse implementation.
(2) Certify and provide hardware-based testimony PUF, TPM, etc.
(3) Make dynamic changes to connectivity.
(4) Apply multiple alternative modes of operation in parallel.
(5) Automated reproduction of operating system images.
(6) Massive use of MTD (Moving Target Defense) generating a constantly evolving dynamic across multiple dimensions of the system to force cyber attackers to question whether the vulnerabilities they find are real or fake, whether the systems are decoys, whether the distribution/layout/composition of the networks are genuine or a mirage, etc.
NG-CR operates/acts as a whole with extreme proactive anticipation in parallel against all types of vulnerabilities (neutralizing, blocking, overriding, patching), indications/attempts of intrusion, defects, failures, slowness, non-ZT, attempted cyber-incident, errors (H/Human-NH/Non-Human), ACEs (Adverse-Cyber-Events) such as cyberattacks with malware/virus, hardware/software/firmware failures/bugs/vulnerabilities/errors/human-weaknesses/misconfigurations, etc. Using in parallel a set of elements with extreme factorization to act long before any of the MEFs (Mission-Essential-Functions) provided by devices, ecosystems, infrastructure with all types of assets/resources: data, IT, OT, CPS, IoT/Internet-of-Things, IoE/Internet-of-Everythings, Industry 4.0, CPDs for AI, IAaaS, Web3, etc. arrive and are affected, and achieve absolute business continuity, reliability, fault tolerance, availability, continuous improvement, etc.
DIMENSIONS IN THE NG-CR.
The NG-CR enables mission assurance, through its extreme anticipation based on superior AI and protection and resilience/survivability capabilities, despite the potential for unexpected adverse cybersecurity events. It provides the capabilities to ensure that all types of IT/OT/IoT systems and infrastructure can continue operating under adverse or stressful conditions, even in a minimally degraded or weakened state, while effectively maintaining operational capabilities and recovering a fully effective operational posture consistent with mission requirements. The NG-CR integrates a comprehensive set of dimensions/capabilities/technologies/planes into a centralized whole:
(1) AI (Superior/Advanced-Massive Multidimensional Artificial Intelligence, tested in parallel). It is fully automated, self-orchestrated, self-systematized, autonomous, extremely mature, self-tested and self-verified, with maximum reliability, robustness, extreme quality, multi-layered-multidimensional, redundant, replicated, self-repairing, self-protected, self-verified, ZT-continuous, self-updated, operates covertly in both fixed and mobile modes, tracks, neutralizes, blocks, nullifies, eliminates cyberattack surfaces and vulnerabilities, integrates (ML/Machine-Learning, DL/Deep-Learning, NLP/Natural-Language-Processing, MD/BD/AD/Data-Mining/Big-Data/Analytic-Data, SE/Expert-Systems, multiple layers of neural networks (a multidimensional cognitive platform/structure for automated/orchestrated, anticipatory, and very low-level decision-making and predictions), machine learning systems, and uses neuroscience connections. intelligent) self-certified/accredited by standards on an ongoing basis (Standards of: data quality-ML ISO/IEC-5259, security ISO/IEC-27000/27090/27563, safety/operational security ISO/IEC-5469/22440, software quality processes/products ISO/IEC-5338/25000/25059/25058/12207/33000, management ISO/IEC-42001, governance ISO/IEC-38507/38000, robustness ISO/IEC 24029-1,-2.-3, performance ISO/IEC 4213, transparency ISO/IEC 12792, fairness ISO/IEC 12791, sustainability ISO/IEC 20226, reliability ISO/IEC 24027/24028/24368/6254/8200, global standards such as ENS, NIST-SP-800-193/NIST-SP-800-53R4, incorporates TCP/Trusted-Computing-Base/Orange-Book, etc.) holistic global in all directions. It hides from all malicious entities, extremely deceives all possible insidious, malicious agents, performs defensive/protective and offensive capabilities to audit, evaluate, neutralize, eliminate, and erase all types of malicious attempts, vulnerabilities, bots, malicious crawlers, flaws, and errors, closes maliciously opened ports, acts against ignorant and unprepared human errors and social engineering, prevents identity theft, capture of passwords and sensitive or confidential information, prevents modifications of all types of information and denial of service, neutralizes authorization attacks, eliminates malware, prevents malicious configuration changes, blocks malicious, deficient, incorrect, and erroneous configurations, cancels malicious modifications, prevents clandestine eavesdropping on all types of fiber, copper, air, and satellite channels, neutralizes malicious code injections, the use of PowerShell to automate cyberattacks, credential theft (for example, in password managers and browsers), gathers intelligence on victims, and has mechanisms to try to guarantee its persistence (for example, during system reboots). system), disable protections, etc.
(2) Fixed and mobile operational capabilities. Use of hidden entities based on fixed and mobile/nomadic DAIM-type defensive-offensive malware, monitoring/monitoring trackers, and comprehensive extreme surveillance to proactively neutralize potential attempts, traces, etc., of harmful/malicious actions, vulnerabilities, etc. Multi-layered homomorphic encryption to protect information (in confidentiality and integrity) stored, in transit, being transmitted, and in use/execution. Integrates nested anonymity/concealment/mimicry/camouflage/steganography mechanisms with multiple layers of extreme confusion, OT, SMPC, ZK, ZT, subliminal channels, network microsegmentation, etc. NG-CR integrates robust protection capabilities such as confidentiality against eavesdropping, integrity against modification, availability against DoS/DoS attacks, non-repudiation against denial-of-service attacks, business continuity, extreme resistance to malware infection (such as ransomware, Trojans, sneakthief/digital theft, etc.), privacy breaches, and the neutralization of identity theft attempts, authorization/IAM attacks, access control, etc. It neutralizes potential attempts to capture electromagnetic (EM) emissions for eavesdropping and EM/EMI interference injections for DoS attacks. It includes out-of-band monitoring/observability capabilities for physical phenomena associated with computing.
(3) Defensive-offensive protection capabilities for dynamic multidimensional protection with extreme anticipation and self-exploration: pentesting, red-team, cyber-crisis simulations, audits, self-assessment, sandboxing, multi-layered quarantine zones, DMZs, reverse-engineering and editing of malicious code to neutralize it, micro-segmentation of all types (networks, entities), etc., continued in parallel.
FINAL ASPECTS.
Next-generation cyber resilience (NG-CR) provides automated, proactive, and extreme anticipation by integrating all types of capabilities in parallel, such as comprehensive observability, simultaneous operations on all possible planes, extreme concealment/deception/confusion against cyber attackers, use of fixed and mobile/nomadic sensors based on multidimensional agents/trackers with superior/massive advanced AI, DAIM-style defensive/offensive malware, and all types of predictors with scalable reasoning/awareness of harmful behaviors, traces, indications, disturbances, anomalies, IoCs (Indicators of Compromise), etc., with actions to block, neutralize, prevent, nullify, and delete all types of harmful attempts, infections, adverse process startups, vulnerabilities, errors due to ignorance/deception, etc.
REFERENCES.
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo-2024.
- Areitio, J. “Exponential Empowerment of Cybersecurity in Protection, Cyber-Resilience, and Maturity Based on the MFE of Defense/Protection Components”. Conectronica Magazine. No. 265. February-March-2025.
- Areitio, J. “Early Cancellation by DAIM/MIAD of Singularities and Techniques Generating Insidious Cyberattacks”. Conectronica Magazine. No. 256. May-2023.
- Forbes, A. “A Foolproof Guide to Cloud Computing Vulnerabilities: The Effects of Security Threats on the Application Programming Interface”. Independently-published-2023.
- Hubbard, DW and Seiersen, R. “How to Measure Anything in Cybersecurity Risk”. Wiley John and Sons-2023.
- Thomas, GM “The Dark Art and Science of GPS Spoofing: Satellite Wars, Hijacking Signals and the Invisible Threat.” Ed. Publication-Independent-2025.
- Kathy, BH “Advanced Cybersecurity for Critical Infrastructure”. Montecito Hot Springs-2024.
- Oakley, JG, Butler, M, York, W., Puckett, M. et al. “Theoretical Cybersecurity: Principles and Advanced Concepts.” Press-2022.
- Infanti, E. “The Human Firewall: Bridging ux and Cybersecurity to Maximize Cyber Resilience.” Ed. Independent Publication-2025.
- Sario, AH “Advanced Cybersecurity Solutions”. Tredition GmbH-2024.
- Kaushik, K., Dahiya, S., Maleh, Y. and Bhardwaj, A. “Internet of Things and Cyber Physical Systems: Security and Forensics”. CRC Press-2022.
- Ramsey, C. “Cybersecurity Secrets: Insider Tips and Lifehacks for Digital Defense.” Independently-published-2024.
- Moseley, R. “Advanced Cybersecurity Technologies”. CRC Press-2023.
- Rodriguez, P. “Revealing the secrets of Cybersecurity: Protecting Your Digital World (From zero to ninety)”. Independently-published. 2024.
- Hodson, CJ “Cyber Risk Management: Prioritize Threats, Identify Vulnerabilities and Apply Controls”. Kogan-2024.
Author: Prof. Dr. Javier Areitio Bertolín – Director of the Networks and Systems Research Group.



