According to CISA, there has been a dramatic increase in the degree to which critical infrastructure relies on the Global Positioning System (GPS)/Global Navigation Satellite Systems (GNSS) (GPS/GNSS) for time dissemination. While the use of GNSS-based time has become more vital for critical infrastructure operations, the security of the GNSS signal itself has become increasingly vulnerable to a wide range of interference and spoofing threats, both intentional and unintentional.
Given the inherently fragile nature of GNSS signals, a key way to protect GNSS reception is through improved visibility into real-time GNSS signal characteristics, including conducting GNSS signal tests and measurements and identifying anomalies. While this work was previously performed in a laboratory setting and troubleshooting required extensive GNSS expertise, the latest performance monitoring software solutions provide operators with a simple way to understand the overall health of GNSS reception.
The de facto global time standard.
According to CISA, GPS has become the de facto time standard for many business users due to its relatively low cost and ubiquitous availability. There is also increasing adoption of GNSS devices like those that use GPS. Until recently, GPS devices were considered simply radio receivers. However, these devices are actually computers, with similar security risks. Threats include denial-of-service attacks (jamming) and the introduction of erroneous data into the system (spoofing). The advent of software-defined radios has increased the ease and reduced the cost with which such attacks can be launched. Efforts should be made to ensure accurate and robust synchronization for your GPS devices.
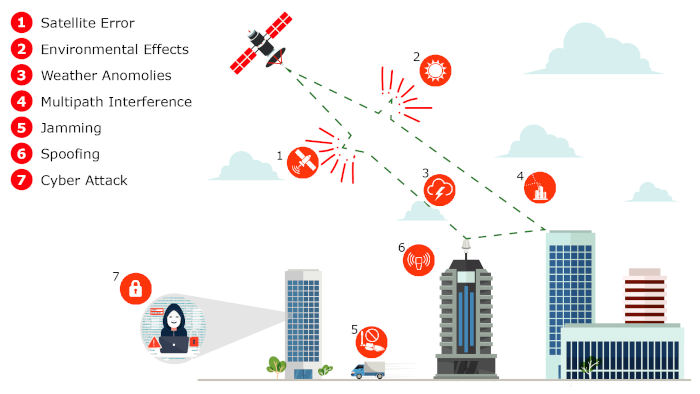
GNSS signals are inherently fragile. GNSS interference typically falls into two categories: "jamming," which renders the GNSS signal undetectable by overpowering it with a locally generated signal on the same frequency, and "spoofing," in which a false GNSS signal is created and tricked into following the receiver. The false signal contains inaccurate information, such as false location data.
The GNSS signal is very weak and largely detectable only with a clear view of the sky. Given the significant distance the signal must travel from satellites orbiting more than 20,100 km above the Earth's surface, GNSS signals have a very low power level (typically -133 dBm) when they reach the Earth's surface.
Reports of interference across large geographic areas are now common worldwide. Furthermore, intentional threats are not the only vulnerability category to be concerned about (see Figure 1). Errors due to weather, atmospheric conditions, and even the operation of GNSS satellite control systems can affect reliable GNSS reception. This has occurred globally, both for GPS in 2016 and, more recently, with the unavailability of Galileo in 2019.
The defense against these threats is visibility, which begins with monitoring.
From Monitoring to Characterization:
GNSS monitoring is the first step, providing network operators with the bird's-eye view they need to examine their critical infrastructure. When an anomaly or outage occurs, the most immediate need is to quickly identify whether the event is isolated to a specific location, affects a regional area, or is caused by a global situation. If the impact occurs in a single location, the cause is most likely a problem such as multipath interference, a local weather anomaly, or a potential jamming/spoofing threat (a common example being a vehicle with a jamming device).
If the impact affects multiple locations, it is likely a more complex issue, and determining the root cause is more difficult, especially in cases like the 2016 GPS anomaly and the 2019 Galileo outage.
Once the scope of the problem has been identified, the next step is to delve into the details. This requires a more specific characterization of the signal to identify the root cause.
GNSS simulators typically have highly sophisticated recording capabilities that developers of GNSS receivers and related equipment have been using for years to test and measure GNSS signals. This equipment is effective for laboratory or even manufacturing environments; however, this instrumentation is expensive and requires highly trained instrumentation specialists. Software now exists that allows network operators to simplify these important measurement and diagnostic functions. One example is Microchip's TimePictra® with its BlueSky performance monitoring capabilities. Table 1 below provides a sample of some of the signal metrics and characteristics that can be tracked with it.
Table 1: Typical Characteristics of a GNSS Signal
Visibility of Timing Anomalies
Although GNSS systems are best known for "navigation," the fundamental operation of GNSS depends entirely on accurate timing. When determining whether GNSS reception is working properly, measuring the phase difference between the expected and received signal is a useful signal characteristic to visualize (see Figure 2).
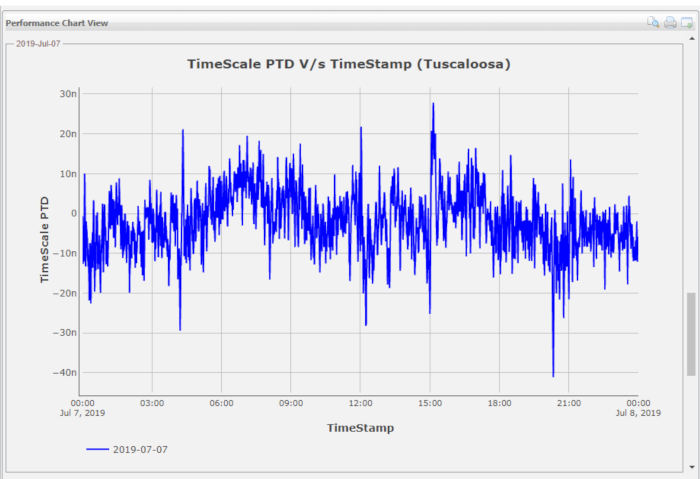 Figure 2: GNSS Receive Phase Measurements.
Figure 2: GNSS Receive Phase Measurements.
Under normal conditions, the phase shift should typically be in the range of ±50 ns, as seen in the graph above. Given this small acceptable performance range, detecting a timing anomaly can be quite difficult and is one of the most important techniques for protecting against GNSS vulnerabilities. Timing anomalies can be gradual, sudden, or complex, such as repeated phase jumps. Timing errors can cause serious disruption and confusion, as such errors can cascade down the underlying timing distribution systems operating in a large data center or mobile switching office.
An example of a timing anomaly is shown below, where a repeated phase shift of approximately 150 ns is generated (see Figure 3). With this type of repeated event, a typical GNSS receive/timing system could be jumping in and out of slack, causing significant disruption to the operation of critical infrastructure.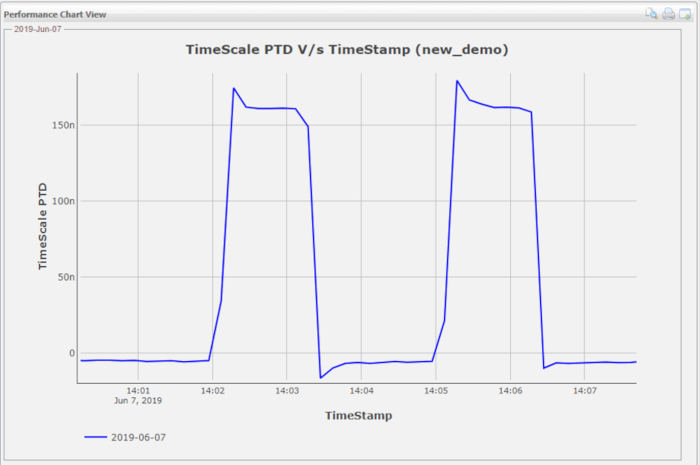
Visibility of Position Anomalies:
In the case of critical infrastructure, the GNSS antenna is usually installed in a fixed location with a clear view of the sky, and its exact position is determined using the coordinates programmed into the receiver. When the GNSS receiver is used for timing, precise antenna recognition is necessary to ensure the most accurate timing performance possible. Any type of offset and/or false position data can degrade the GNSS receiver's timing performance and ultimately cause it to lose the ability to track satellites altogether.
In the following example, under normal conditions, the position received by the GNSS receiver is approximately 1–5 meters off compared to the measured position of the GNSS antenna. The first graph in Figure 4 shows the normal position fluctuation; however, once a day, there is also a position deviation of about 15–20 meters. The graph below shows a phase shift of approximately 100 ns (peak-to-peak) simultaneous with the position shift in the first graph. This position shift, likely the result of multipath interference, is impacting timing performance. The characteristics of the multiple GNSS signals are displayed together to help network operators better understand the cause-and-effect relationship.
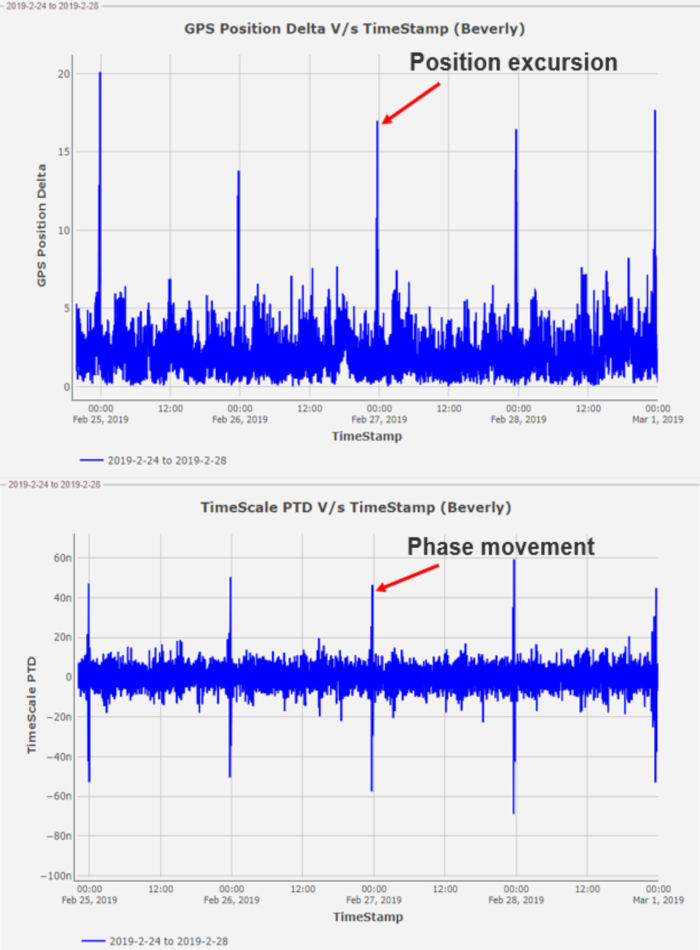 Figure 4: Position deviation that creates phase jumps
Figure 4: Position deviation that creates phase jumps
Visibility of Spoofing:
Spoofing attacks can be difficult to detect because they involve manipulating the GNSS data itself. Like threats to data networks, GNSS spoofing is a continuous and evolving threat vector that requires a defense system that can be updated to protect against new threats.
As shown in Figure 5, a GNSS receiver is tracking six satellites under normal conditions, and then the satellites begin to be dropped prematurely. Over the course of approximately three minutes, all the satellites are no longer tracked. This rapid disappearance of satellites is abnormal and serves as a simple example of how spoofing can create a confusing situation for a GNSS receiver attempting to track satellites.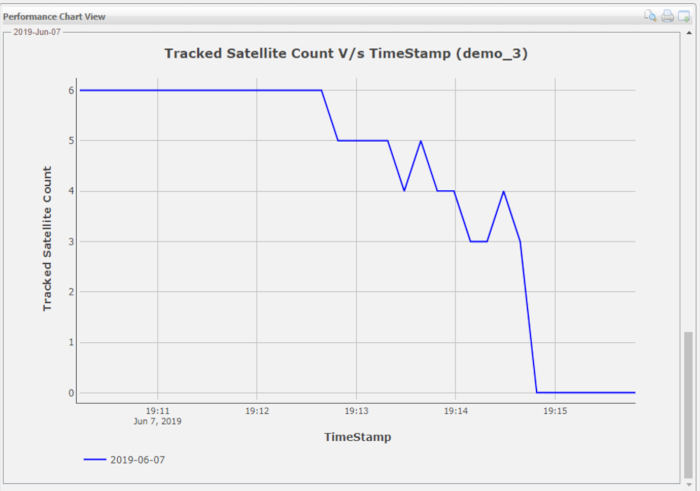
Protection of all devices
Security has become the most important requirement for critical infrastructure operations. Any device connected to critical infrastructure can become a target for attack and must be as secure as possible. Strengthening the security of a GNSS system is an ongoing process due to the constant emergence of new threats. Just like network security vulnerabilities, new GNSS vulnerabilities are on the rise, and GNSS signal visibility is a vital capability for helping to determine the root cause of a GNSS vulnerability, especially before a minor disruption becomes a more serious one.
When a GNSS vulnerability is detected, current performance monitoring software allows for monitoring the quality of GNSS reception without having to send network operations personnel on a costly visit to check an antenna on the roof of a tall building. It allows critical infrastructure operators to quickly identify whether the problem is specific to a location or affects a wider geographic area. It also enables the next step in the mitigation process, providing operators with the key performance metrics needed to gain the visibility required to take swift and cost-effective action.
About the author:
Greg Wolff has worked in the timing and frequency industry since 1988 and was one of the early pioneers in commercializing network timing solutions for major critical infrastructure operators worldwide. Greg actively contributes to emerging standards that support PNT (Position Navigation and Time) resilience and, most recently, as part of Microchip Technology's Frequency and Time Systems group, launched the BlueSky GNSS Firewall.
By Greg Wolff, product line manager, frequency and timing systems, Microchip