Extreme multi-factor authentication involves maximizing the number of factors that make up the countermeasures/safeguards/controls. For example, a low-factor authentication method for SSO/Single Sign-On is reckless nowadays. Cybersecurity countermeasures/safeguards/components/protection/defense controls (such as identification, integrity/authenticity, authentication, confidentiality, availability, non-repudiation, authorization, access control, privacy, and traceability of actions (with factors such as logs, audit trails, SIEM, and data freshness with factors such as signed timestamps/watermarks, digital signatures, hashes, etc.) should be composed of a maximum/extreme number of tightly chained factors (operating as a single unit) to achieve greater robustness, reliability, maturity, cyber resilience, quality, efficiency, effectiveness, protection, fault tolerance, anti-hacking (against massive malicious AI/GenIA techniques), defense in depth, performance, etc. For example, a low-factor authentication (only one password, only one application, only one physiological/behavioral biometric mechanism) (Fingerprint/retina/iris, voice biometrics, image biometrics, videoconferencing, etc. are insufficient) can be increasingly easily breached with advanced deep-AI tools. Cybersecurity uses AI-based multidimensional inference with the capabilities of a set of deferred and real-time trained models to make faster logical decisions and more cybersecure operations based on live data (it is defensive, protective, but also offensive to be able to monitor/evaluate cybersecurity controls and proactively prevent infections, anomalies, and misbehavior using nomadic malware defense techniques such as DAIM, ethical hacking, network teams, forensic analysis (maintaining the chain of custody), penetration testing, etc. It gathers information/intelligence, scans, analyzes vulnerabilities, monitors exploitation attempts, privilege escalation, pivoting, lateral movement, attempts at concealment/mimicry, etc.)
COUNTERMEASURES/FACTORS IN MFE-CYBERSECURITY.
The repertoire of countermeasures/safeguards/controls in MFE-cybersecurity is growing daily; they include, among others, the following:
1- MFE-Confidentiality/MFEC-end-to-end-of-data/etc. (Confidentiality-with-multi-factor-extreme-componentization). This component/control is responsible for preventing the disclosure/knowledge/understanding/inference/deciphering/decoding/understanding of anything that is private/secret/hidden, such as identities, structured/unstructured data (and all its higher levels of elaboration: information, intelligence, wisdom, etc.), content/messages of all kinds (natural-legal persons, financial, health, military, industrial, diplomatic, etc.), copyrights, etc. It ensures that their existence, where they are, who they are, their location, their interrelationships with other entities, etc., are not known. This involves using a very high set of factors/mechanisms linked together as a whole, very robust (such as post-quantum end-to-end cryptography/encryption (with post-quantum cryptographic algorithms such as FIPS 203 (ML-KEM), FIPS 204 (ML DSA), SLH-DSA, etc.) and conventional cryptography of very high robustness (NG-3DES, NG-AES/AES-CRT-NIST-SP-800-38A, NG-RSA, NG-GM, NG-BG, NG-IDEA, ECC, FIPS-140-3-maximum-level, etc.), steganography/watermarking, subliminal channels/anonymity, OT, ZK, SMPC, ZT, Faraday cages (to prevent illegal capture of information through electromagnetic emanations from all types of devices, screens, controllers, PCs, etc.), Technology-deception, quarantine/sandboxing, honeypot/honeynets/DMZs, NF-VPN (hides the real IP address to protect the connection by continuously creating multiple virtual IP addresses), etc.). Prevents SNDL (Store Now Decrypt Later) cyber-attacks to decrypt or cyber-attack all types of pre/post-quantum cryptography, protects against BYOD (Bring Your Own Device) activities, data leaks with DLP for Email, provides data security on the Web, Endpoint Security (through EDR services - endpoint detection and recovery with cyber-threat telemetry), networks (with NGFW/New-Generation Firewalls), applications, data, Clouds, Edges, etc.
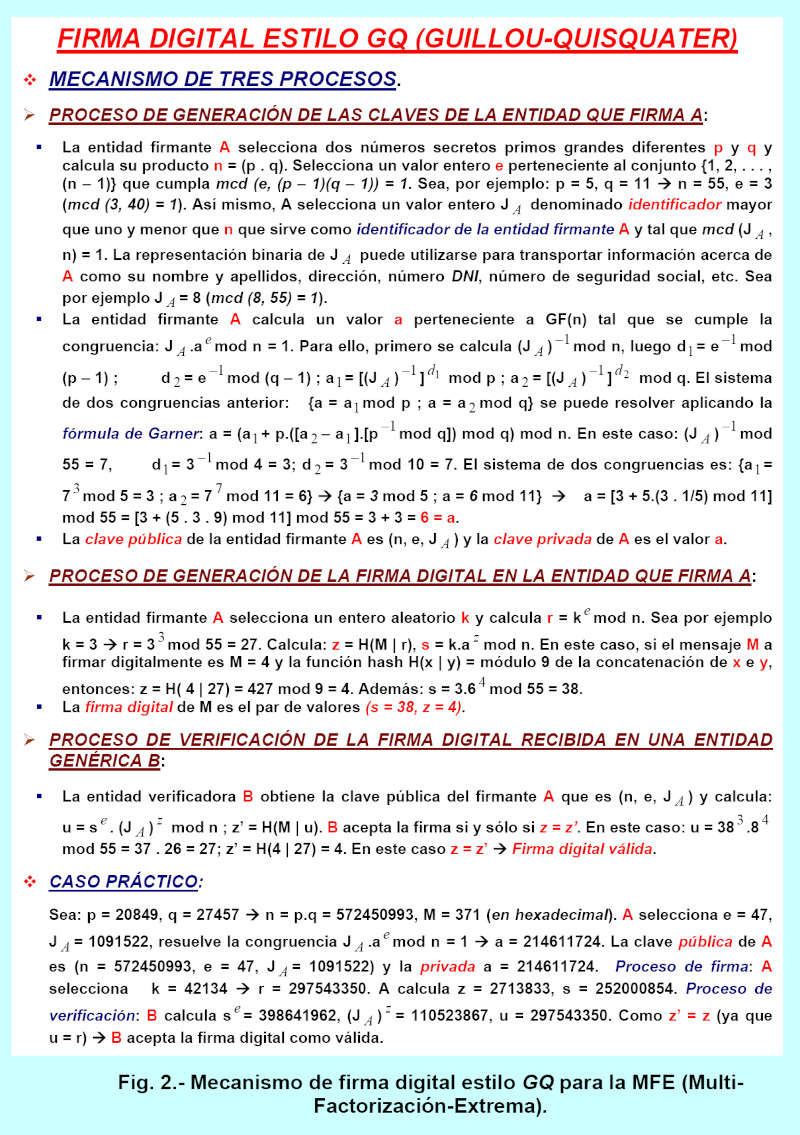
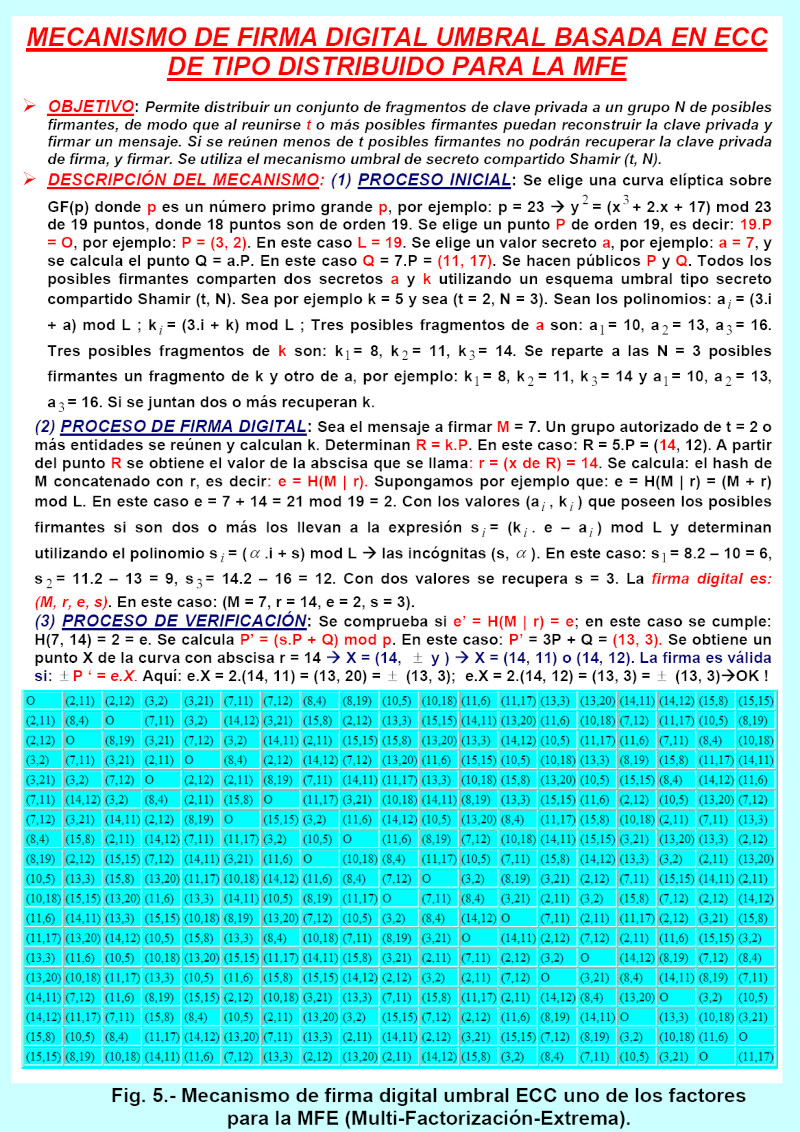
2- MFE-Non-Repudiation/MFENR-of-actions/operations/behaviors (Non-repudiation-with-extreme-multi-factoring). This component/control is responsible for preventing any type of entity (natural-legal person, computing device, AI-based personal assistant/AI robot, AMR-Autonomous-Mobile-Robot/AGV-Automated-Guided-Vehicles (with FMCW/PCR-24/60/122GHz radars), autonomous/intelligent vehicles, ecosystems-with-embedded-systems-technology/COM (Computer-On-Modules)-SGET (Standardization-Group-for-Embedded-Technologies), etc.) from denying that it has performed an operation/action/task/etc. This component uses a chain of multiple factors/technologies such as cryptography/digital signatures, multiple backups/extreme monitoring, TTPs (Trusted Third Parties), etc.
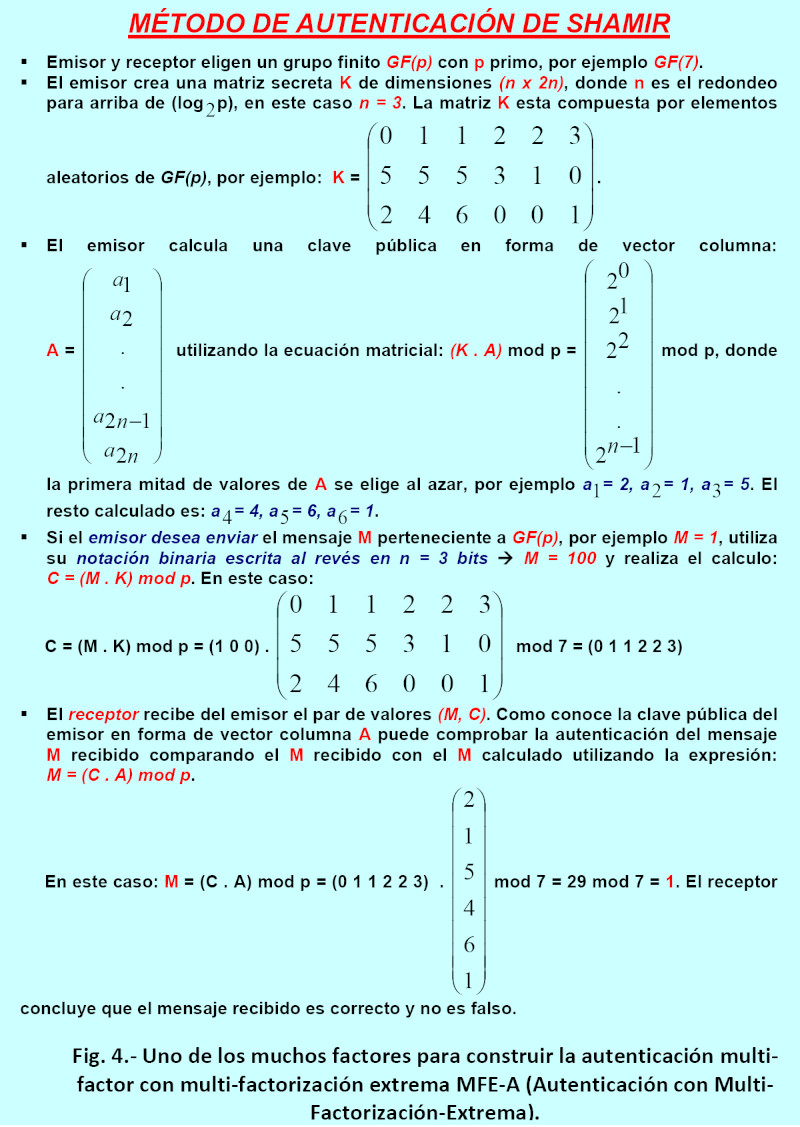
3- MFE-Authentication/MFEA-of-entities (Extreme Multi-Factor Authentication). This component/control is responsible for demonstrating/proving that an entity (person, machine, software, firmware, hardware, service, supplier, etc.) is who it claims to be using a very high set of technologies/factors: something secret that one knows (passwords of extremely high entropy (entropy is calculated as the decimal logarithm of CA raised to L where the length L must be very large, made up of numbers, uppercase/lowercase letters, special characters, Greek letters, etc., i.e., with a CA alphabet of very high cardinality); that the password is not a default and is different for each use, that it is updated very frequently (there are companies that prevent their users from updating their passwords and do not control the level of entropy of them, they don't care out of negligence or ignorance), when the user has gone to another company (they should be blocked), use of riddles/problem-solving, CAPTCHA (Completely Automated Public Turing Test to Tell Computers and Humans Apart) (allows differentiation between people and artificial beings/bots), keys, PINs, answers to a battery of questions unknown to others, etc.), something that one is (physiological biometrics (fingerprints, facial recognition, retina, iris, DNA, voice analysis, etc.) and behavioral biometrics (how one speaks/writes, walks, gestures, handwriting/graphology, etc.)), something that one has/wears (bionic implants, smart cards, bank coordinate cards that allow creating passwords, applications (like Okta), a mobile phone to receive a second/third/etc. OTP/One-Time Password, hardware tokens/hardware password generators, etc.), where one is located (outdoor geolocation using satellite networks (GPS, Galileo, Glonass, etc.) and indoor geolocation using Bluetooth, video cameras, sensors, etc.), video surveillance with untapped/authentic devices with multiple PUFs, etc.), what is the time (year/month/day/hour/minute/second/atomic clock/etc.)
 4- MFE-Availability/MFED-of-systems/data/MFE-Business-Continuity/MFECN (Multi-factored Availability for tolerance to any possible contingency/cyberattack/etc., achieving business continuity, defense in depth, etc.). This component is responsible for generating a large number of factors/options to prevent blockages/downtime/failures/non-functioning/unavailability of all kinds, in all types of systems/resources/products: hardware/firmware/software/communications/power supply/APPs/APIs/OSs/data/information, etc./supply chains/people/management/governance/SOCs/etc. Its mission is to provide multiple, chained, protected redundancy factors; for example, if the power supply is interrupted, having multiple backup UPSs (uninterruptible power supply systems). If communications fail, provide multiple alternative backup communication channels, such as via multiple known and unknown satellite networks (Galileo, GPS, GLONASS, BeiDou, etc.), or communications with other providers (cable, fiber, 4G, 5G, 6G mobile, etc.) to maintain uninterrupted communications. If cloud/edge storage is lost, have multiple private backup cloud/edge storage options. If a ransomware cyberattack is successful and we cannot access the software and data encrypted by us using MFC, provide a large number of encrypted backups in multiple different remote locations with continuous verification of their operational status. For example, in case of hard drive failure, use hard drive redundancy such as RAID (Redundant Array of Inexpensive Disks), etc. The CRA (Cyber-Resilience-Act) regulations promote improved availability and reliability of critical operations so they can continue running without interruption, for example, micro-segmentation in networks, operating with virtualization by creating isolated virtual environments with separate virtual machines (with separation of operational functions) and software/firmware hypervisors for maintenance tasks, updates, continuous OTA/On-The-Air software-firmware updates, implementation of zonal architectures in vehicles creating differentiated zones, etc.
4- MFE-Availability/MFED-of-systems/data/MFE-Business-Continuity/MFECN (Multi-factored Availability for tolerance to any possible contingency/cyberattack/etc., achieving business continuity, defense in depth, etc.). This component is responsible for generating a large number of factors/options to prevent blockages/downtime/failures/non-functioning/unavailability of all kinds, in all types of systems/resources/products: hardware/firmware/software/communications/power supply/APPs/APIs/OSs/data/information, etc./supply chains/people/management/governance/SOCs/etc. Its mission is to provide multiple, chained, protected redundancy factors; for example, if the power supply is interrupted, having multiple backup UPSs (uninterruptible power supply systems). If communications fail, provide multiple alternative backup communication channels, such as via multiple known and unknown satellite networks (Galileo, GPS, GLONASS, BeiDou, etc.), or communications with other providers (cable, fiber, 4G, 5G, 6G mobile, etc.) to maintain uninterrupted communications. If cloud/edge storage is lost, have multiple private backup cloud/edge storage options. If a ransomware cyberattack is successful and we cannot access the software and data encrypted by us using MFC, provide a large number of encrypted backups in multiple different remote locations with continuous verification of their operational status. For example, in case of hard drive failure, use hard drive redundancy such as RAID (Redundant Array of Inexpensive Disks), etc. The CRA (Cyber-Resilience-Act) regulations promote improved availability and reliability of critical operations so they can continue running without interruption, for example, micro-segmentation in networks, operating with virtualization by creating isolated virtual environments with separate virtual machines (with separation of operational functions) and software/firmware hypervisors for maintenance tasks, updates, continuous OTA/On-The-Air software-firmware updates, implementation of zonal architectures in vehicles creating differentiated zones, etc.
5-MFE-integrity/MFEI/MFE-authenticity/MFE-AU-of-data/devices (Integrity/authenticity-with-extreme-multi-factor-security). This component is responsible for protecting data/messages from alteration, change, or cloning of data/software/firmware/hardware/entities. If the data/information is changed, it becomes inauthentic. To achieve this, a large number of factors are chained together as a unit, such as digital signatures, hashes, PKI-X.509 certificates, etc. For hardware, multiple PUF functions are used to determine if a hardware product has been cloned or modified anywhere from its origin, in the supply chain, or even at its final point of use, including timestamps, steganography, PUFs, etc.
6- MFE-identification/MFE-ID-of-entities (Extreme Multi-Factor Identification). This component prevents an entity from deceiving others by attempting to present a false identity. Identities can be human (IH), non-human (INH), hybrid, reusable, decentralized, devices, programs, systems, applications/APPs/APIs, bots, service accounts, identities of things (IDoT) in the IoT context, digital twins, identities of entities in the metaverse and virtual worlds, VR (Virtual Reality)/AR (Augmented Reality), etc. Everything has an identity, and each identity has various privileges/rights. Protect against identity theft through cyberattacks such as scraping, phishing, and smishing; block session cookies; malicious QR codes/links/URLs (with invisible characters); malicious power outlets for PCs, mobiles, and vehicles; cyber scams involving account takeovers (ATOs); remote access trojans (RATs); and more. Factors used include ZK/ZT technologies, ITDR (Identity Attack Detection and Response), IGA (Identity Governance and Management), and others.
7- MFE-authorization/MFEAU-of-entities (Extreme Multi-Factor Authorization). This component controls which entity can access which resources and what operations/actions/access rights/privileges each active entity has to perform on those resources (read, write, execute, delete, encrypt, etc.) and at what time, location, and mode. It is essential to protect the assignment of access rights and correct authorizations to the correct entities for the correct specific resources and to control the correct operations/behaviors with the correct minimum privileges by chaining numerous defense/protection factors/controls such as ACLs (Access Control Lists; there are as many as there are columns in the MCA), Capability Lists/LCs (there are as many as there are rows in the MCA), access matrix/MA or access control matrix/MCA, etc.
8- MFE-access-control/MFE-CA-entity (Extreme Multi-Factor Access Control). This component controls the interaction between active entities/subjects and passive entities/resources/objects (ensuring that the former access authorized resources) while preventing illegal/malicious access. It integrates identification, authentication, authorization, account management, etc. There are many different types of access controls: RBAC (Role-Based Access Control), ABAC (Attribute-Based Access Control), PBAC (Policy-Based Access Control), etc. Countermeasures include IAM (Identity and Access Management), CIAM (Customer Identity and Access Management), PAM (Privileged Access Management), etc. All access controls must protect the who, what, when, where, and how of the interactions between all participants: systems, data, and other entities.
 9-MFE-Privacy/MFEP-of-identities-content-actions-geolocation-moment-metadata (Privacy-with-extreme-multi-factoring). This component of cybersecurity (privacy of content, identities, geolocation, associations and relationships between entities, time-based data, how to act, behave, think, being observed/monitored, etc.) and which also has its own identity is responsible for preventing numerous cyber-threats/cyberattacks such as: the secrecy with collection/retention/interception/poisoning-ARP/DNS, MITM-Man-In-The-Middle/processing/observation/monitoring/dissemination/invasion/leaks/traffic analysis, etc. malicious of all types of structured/unstructured data (information, intelligence, knowledge, etc.) about entities (people, subjects, devices, etc.); For example, eavesdropping using microphones and illegal image capture using webcams in elevators, TVs, mobile phones, computers, vehicle dashboards, etc.; protecting web browsing against trackers and cookies by implementing MF-VPN factors that continuously change the real IP address to a virtual one, etc.; tracking identity by monitoring the Dark/Deep Web; protecting against social engineering (manipulating people to voluntarily do what they wouldn't normally do), spoofing (using identity theft for illicit/malicious purposes), scavenging (obtaining information after a job is finished), shoulder surfing (physically spying on users), etc. Some of the factors used are: anonymity (concerns hiding entities, identities (of entities such as credentials, geographic location/geolocation (metadata from a photo must be professionally removed as it reveals geolocation and violates privacy), time, etc.) and content (stored, transferred, executed) - with encryption, steganography, subliminal channels, OT/ZK/SMPC, etc.; anonymity must be sender/receiver/bidirectional anonymity), use of pseudonyms, use of proxies/VPNs (which continuously change the real IP address to a virtual IPv4/IPv6), non-traceability (hides relationships), non-observability, plausible deniability (it cannot be known/proven that someone said or did something; makes malicious non-repudiation impossible)/OTR (Off-The-Record), private channels, private searches, differential privacy/K-Anonymity, location privacy (physical and logical), OT (Transfers n of m), ZK (Zero Knowledge), subliminal channels, network micro-fragmentation, homomorphic compromise/delivery, encryption, steganography/watermarking, DMZs (Demilitarized Zones), DAIM defense-malware, PIR (Private Information Retrieval), protection against data leakage through electromagnetic data emanations/use of Faraday cages, use of predictive DLP (Data Loss Prevention), use of deception technology and RF inhibitors, IDV (Digital Identity Verifier), etc.
9-MFE-Privacy/MFEP-of-identities-content-actions-geolocation-moment-metadata (Privacy-with-extreme-multi-factoring). This component of cybersecurity (privacy of content, identities, geolocation, associations and relationships between entities, time-based data, how to act, behave, think, being observed/monitored, etc.) and which also has its own identity is responsible for preventing numerous cyber-threats/cyberattacks such as: the secrecy with collection/retention/interception/poisoning-ARP/DNS, MITM-Man-In-The-Middle/processing/observation/monitoring/dissemination/invasion/leaks/traffic analysis, etc. malicious of all types of structured/unstructured data (information, intelligence, knowledge, etc.) about entities (people, subjects, devices, etc.); For example, eavesdropping using microphones and illegal image capture using webcams in elevators, TVs, mobile phones, computers, vehicle dashboards, etc.; protecting web browsing against trackers and cookies by implementing MF-VPN factors that continuously change the real IP address to a virtual one, etc.; tracking identity by monitoring the Dark/Deep Web; protecting against social engineering (manipulating people to voluntarily do what they wouldn't normally do), spoofing (using identity theft for illicit/malicious purposes), scavenging (obtaining information after a job is finished), shoulder surfing (physically spying on users), etc. Some of the factors used are: anonymity (concerns hiding entities, identities (of entities such as credentials, geographic location/geolocation (metadata from a photo must be professionally removed as it reveals geolocation and violates privacy), time, etc.) and content (stored, transferred, executed) - with encryption, steganography, subliminal channels, OT/ZK/SMPC, etc.; anonymity must be sender/receiver/bidirectional anonymity), use of pseudonyms, use of proxies/VPNs (which continuously change the real IP address to a virtual IPv4/IPv6), non-traceability (hides relationships), non-observability, plausible deniability (it cannot be known/proven that someone said or did something; makes malicious non-repudiation impossible)/OTR (Off-The-Record), private channels, private searches, differential privacy/K-Anonymity, location privacy (physical and logical), OT (Transfers n of m), ZK (Zero Knowledge), subliminal channels, network micro-fragmentation, homomorphic compromise/delivery, encryption, steganography/watermarking, DMZs (Demilitarized Zones), DAIM defense-malware, PIR (Private Information Retrieval), protection against data leakage through electromagnetic data emanations/use of Faraday cages, use of predictive DLP (Data Loss Prevention), use of deception technology and RF inhibitors, IDV (Digital Identity Verifier), etc.
10- MFE-Audits/Action-Traceability/Accounting-with-Extreme-Multi-Factoring. This component is responsible for analyzing and auditing to block vulnerabilities, misconfigurations, dangerous session cookies, etc. It uses factors such as Logs-monitor/Audit-Logs/Events/SIEM, SecDevOps, etc.
11-MFE-Anti-capture-of-emanations-and-block-electromagnetic-interference (Anti-capture-of-emanations-and-block-electromagnetic-interference-with-extreme-multi-factorization). This component is responsible for preventing information theft and EMI/RFI interference from disrupting operations.
12-MFE-Enclosures for storing or running infected software (Enclosures-for-storing-or-running-infected-/dangerous-software-with-extreme-multi-factoring). MFE-Quarantine Zones prevent the contamination of the rest of the computer ecosystem/network if infected files are stored in quarantine zones with isolation walls and extreme multi-factoring. MFE-Sandboxing consists of enclosures with multiple layers/walls of isolation for running infected files, preventing their malicious spores from escaping.
13-MFE-certification/accreditation/qualification (Certification-with-extreme-multi-factoring)-continuous. This component ensures that every product/element/component (hardware/firmware/software/devices/people/companies/supply-chains, etc.) has a very high level of continuously verified/evaluated/audited accreditations demonstrating that the element is MFE-cybersecure (has not been compromised in a supply chain, etc.). Many standards, criteria, norms, etc., must be audited/evaluated to receive certification/accreditation from an accredited external body. For example, an element can receive CC (Common Criteria) certification with the EAL4+ guarantee issued by an accredited external body such as Trust-CB. Other certifications, in this case for wireless products, include GSMA NESAS, German BSI NESAS, and CCS-GI. Other standards/regulations/frameworks to be certified are ENS/CCN, ISO/IEC-27001, ISO 17799, ISO-7498-2, BS-7799, SAS-70, DIN-EN-80001-1 (for risk assessment of devices such as cameras/PCs-tablets, etc.), ISO/IEC-27090, ZTA (Zero Trust Architecture)-defined-by-NIST-800-207, ISO/IEC-27563, DORA, ISO/IEC-5469/22440, MITRE-ATT&CK (Adversarial Tactics, Techniques and Common Knowledge), NIS2, CRA (Cyber Resilience Act), ISO/IEC-27002, NIST-CSF2.0 (Class II products: firewalls, IDS, microprocessors, etc.; Class I products: identity management systems, Software/hardware/firmware for privileged access management, access control readers, password managers, etc.), PCI-DSS, SOX, HIPAA, GDPR, CCPA, NIST-SP-800-63, ISO/IEC-38507 governance, etc. Other accredited external bodies authorized to evaluate, audit, and issue certifications include Applus, Leet-Security, ENAC, AENOR, and CCN (which certifies with a high level of qualification under the CPSTIC (Catalog of Security Products and Services for Information and Communication Technologies of the CCN) qualification), etc. It is not enough for individuals and companies to be aware; they must be trained through rigorous and accredited examinations and knowledge assessments to determine their competence in responding appropriately to cyber threats, cyberattacks, and cyberfakes. This training should utilize real-world audits, penetration tests, network teams, etc., and be conducted through ongoing examinations, trials, and evaluations.
SOPHISTICATION OF CYBERATTACKERS' ACTIVITIES.
Cyber attackers are increasingly exploiting vulnerabilities (people/hardware/firmware/software/supply chain/management/governance/etc.): (i) Default installations such as standard passwords for certain products, services installed without operator/user knowledge, minimal and overly basic cybersecurity levels, etc. (ii) Little to no user training/certification/evaluation with ongoing assessments; awareness alone is insufficient. For example, using the same password for all types of work and leisure activities such as social media, even for high-risk operations like multiple logins using SSO (Single Sign-On), writing the password near the workstation, etc. (iii) Open ports, unnecessary services installed, malware that stealthily opens ports, performs lateral movements (to advance its cyberattack and remain dormant), etc. (iv) Failure to delete default accounts of inactive, deceased, or departing users, etc. Failure to delete unused services (which are a source of cyberattacks), etc. (v) Failure to use robust antivirus software and fail to update it, and failure to apply patches and updates to software such as browsers, apps/APIs, and operating systems. Failure to address password vulnerabilities due to their weakness or low entropy. System updates are becoming increasingly essential; the time between the existence of a vulnerability (zero-day exploit) and cyberattacks exploiting those vulnerabilities is decreasing daily. (vi) Failure to continuously use SIEM (Security Information Event Manager) or auditing, forensic analysis, etc., tools that allow monitoring the status of the network/hosts, the value of event logs, log supervision, etc. Failure to use switches/L2 and instead using hubs/L1. (vii) Lack of shared responsibility in many supply chains. (viii) The large attack surface presented by Active Directory (AD) fosters an increase in Kerberoasting attacks. (ix) Increased cyber threats/cyberattacks due to deficiencies and flaws in governance, management, quality, and certification of all types of products (hardware, firmware, software, services, apps, APIs, etc.), suppliers, companies, individuals, etc. Furthermore, encryption must provide multi-factor protection, including post-quantum encryption, for all types of data/information created, stored, in transit, in execution, etc. (x) There is an exponential increase in the attack surface generated by the exponential growth of IoT ecosystems/devices (in all types of locations, including homes, modern cars, critical infrastructure, etc. Network support for numerous IoT devices using reduced capacity is creating a large number of entry points for malicious agents/actors/malware), edge ecosystems, etc. Vulnerabilities in communications of all types: IoT/IIoT/IoMT such as Zigbee/Thread/Sigfox/Matter/BLE-5.0 (Bluetooth Low Energy 5.0)/LoRaWAN/Wi-Fi 7/MIOTY/DEC-NR+ (Digital Enhanced Cordless Telecommunications New Radio Plus ETSI-ITU)/NB-IoT/LTE-M/etc. (xi) There is significant concern about the disruption of biometric authentication using AI-based deepfake technologies. Similarly, the widespread adoption of cloud/multi-cloud environments with difficult-to-identify vulnerabilities is leading to an increase in cyberattacks.
FINAL ASPECTS.
Currently deployed cybersecurity must operate proactively through technologies (confidentiality, integrity, non-repudiation, availability-business continuity-high availability, authentication, etc.), processes (management-analysis, governance, maturity, quality, continuous monitoring, ZT/Zero-Trust, SecDevOps, vulnerability hunting/management (0-day/n-day), patch management, continuous updates, traceability, threat hunting, continuous audits, penetration testing, red team, etc.), and above all: products, companies, suppliers, supply chains, IoT/Edge/multi-cloud ecosystems, 2.5G/3G/4G-LTE/5G-cellular/5G-non-cellular-DECT-NR+/6G infrastructures, people (awareness is no longer sufficient; there must be rigorous training/certification/evaluation), etc. that must be continuously certified/audited/evaluated (based on rigorous standards such as ISO, ENS/CCN, Common-Criteria/EAL, NIST, ISO/IEC-33000, MITRE, DORA, CRA, ISO-26262, PCI-DSS, etc.) with high qualification/rating by accredited external entities such as ENAC, AENOR, Trust-CB, CCN, LEET-Security, Applus, etc.
REFERENCES.
- Areitio, J. “Information Security: Networks, Computing and Information Systems”. Cengage Learning-Paraninfo-2024.
- Areitio, J. “Early Cancellation by DAIM/MIAD of Singularities and Techniques Generating Insidious Cyberattacks”. Conectronica Magazine. No. 256. May-2023.
- Gupta, I. “Operationalizing Expectations and Mapping Challenges of Information-Privacy and Data-Protection-Measures: A Machine-Generated Literature Overview”. Springer-2024.
- Hubbard, DW and Seiersen, R. “How to Measure Anything in Cybersecurity Risk”. Wiley John and Sons-2023.
- Wilson, DC “Cybersecurity”. The MIT Press Essential Knowledge Series. The MIT Press-2022.
- Stewart, AJ “A Vulnerable System: The History of Information Security in the Computer Age”. Cornell University Press-2023.
- Xu, Z., Choo, K.-KR, Dehghantanha, A., Parizi, R. and Hammoudeh, M. “Cyber Security Intelligence and Analytics”. Springer-2020.
- Di Pietro R. “New Dimensions of Information Warfare”. Springer-2021.
- Smith: JEH “The Internet Is Not What You Think It Is: A History, a Philosophy, a Warning”. Ed.-Princeton University Press-2023.
- Gupta, I. “Expectations vs Realities of Information Privacy and Data Protection Measures: A Machine-generated Literature Overview.” Springer-2023.
- Brooks, C. “Inside Cyber: How AI, 5G, IoT, and Quamtum Computing Will Transform Privacy and Our Security.” Wiley-2024.
Author: Prof. Dr. Javier Areitio Bertolín – Director of the Networks and Systems Research Group.